


Google hacking Basics[edit] One can even retrieve the username and password list from Microsoft FrontPage servers by inputting the given microscript in Google search field: "#-Frontpage-" inurl: administrators.pwd or filetype: log inurl password login NSA files decoded: Edward Snowden's surveillance revelations explained Two factors opened the way for the rapid expansion of surveillance over the past decade: the fear of terrorism created by the 9/11 attacks and the digital revolution that led to an explosion in cell phone and internet use. But along with these technologies came an extension in the NSA’s reach few in the early 1990s could have imagined. Details that in the past might have remained private were suddenly there for the taking. Chris Soghoian Principal technologist, ACLU
dutchreleaseteam torrent search Torrentz Age: 1d | 3d | 7d | 1m Quality: any | good | verified 8,654 torrents (0.013s) Order by rating | date | size | peers The Bucket List 2007 NL subs xvid DutchReleaseTeam avi » movies Creating an Effective Sock Puppet for OSINT Investigations – Introduction – Jake Creps Introduction and Philosophy In recent light of the epic failure by Surefire Intelligence to frame Robert Mueller for sexual assault allegations, I feel it’s important to discuss and unpack how to make a good sock puppet for OSINT operations. If you aren’t familiar, just google Jacob Wohl or Surefire Intelligence and you will likely be flooded with information about the scandal. For further details on the unraveling of the socks Wohl made, check out Aric Toler’s threat on Twitter @arictoler from Bellingcat. Now, without further ado, let’s get started on constructing a sock puppet for OSINT investigations.
Friends and enemies in the Middle East. Who is connected to whom? - interactive As the US and UK are set to again commit to military involvement in the Middle East, this interactive visualises the intricate, complex and sometimes hidden relationships and alliances across the region. Its tangled, opened state is meant as a kind of visual joke, showing how its fabric defies simple solutions. You can filter relationship types ‘on’ and ‘off’ in the bottom left and also rollover and click on different players to get a clarified view.
Clustering Engine Carrot2 Search Results Clustering Engine Carrot2 organizes your search results into topics. With an instant overview of what's available, you will quickly find what you're looking for. Choose where to search: Mastering Google Search Operators in 67 Easy Steps See Also:• Google Search Operators - Best Practices• 25 Killer Combos for Google's Site: Operator Any SEO worth their sustainably harvested pink Himalayan salt knows that Google offers a variety of advanced search operators – special commands that take you above and beyond regular text searches. Learning search operators is a bit like learning chess, though. It's easy to memorize how each piece moves, but that's about 1% of your path toward mastery.
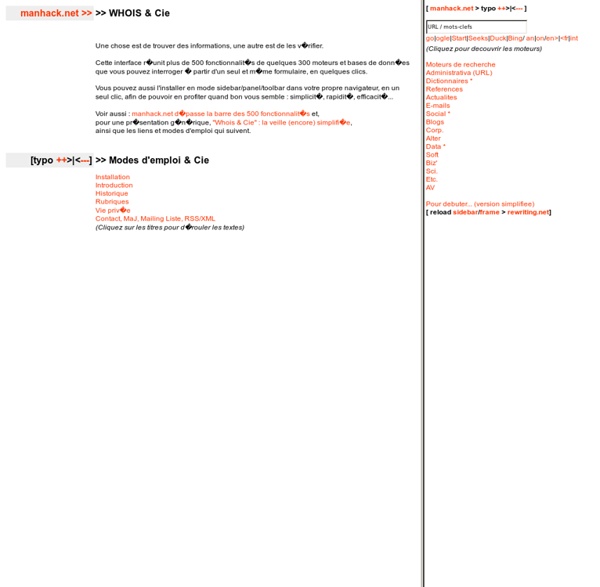
Journalism Tools sur Pinterest Pinterest Today Explore When autocomplete results are available use up and down arrows to review and enter to select. Touch device users, explore by touch or with swipe gestures. Metasearch engine A metasearch engine is a search tool[1][2] that sends user requests to several other search engines and/or databases and aggregates the results into a single list or displays them according to their source. Metasearch engines enable users to enter search criteria once and access several search engines simultaneously. Metasearch engines operate on the premise that the Web is too large for any one search engine to index it all and that more comprehensive search results can be obtained by combining the results from several search engines. This also may save the user from having to use multiple search engines separately. The process of fusion also improves the search results.[3]
How to Search Twitter - The Best Twitter Search Tricks The Twitter Archiver and Twitter Bots app fire each time a new tweet is found that match your search query. You can write simple search queries (like #Oscars) or more complex query (like obama min_retweets:10 filter:news) that uses one or more Twitter search operators. Here’s a complete list of Twitter search operators that can help you perform more accurate searches on Twitter: from:BarackObama All tweets sent by a particular Twitter user filter:verified cool OR amazing Only show tweets from verified Twitter accounts (with the blue tick)
20 tools and resources every journalist should experiment with Tools have always come from the need to carry out a specific task more effectively. It's one of the main differences between human beings and the rest of the animal kingdom. We may still be slaves to the same old evolutionary urges but we sure know how to eat noodles in style. In journalism, an abstract tool for uncovering the most interesting and insightful information about society, we can generally boil the workflow down to four stages: finding, reporting, producing and distributing stories. So with that in mind, here are a range of tools which will – hopefully – help you carry out your journalism tasks more effectively. 1. 100 Incredibly Useful and Interesting Web Sites - PCWorld Even as the Web has become more entertaining--and certainly better looking--over the past 15 years, it has also become much more useful and practical, as the 100 sites in this feature will demonstrate. I've organized the sites in the list by the type of task they help you with. It is not a ranking; in each category I recommend sites that specialize in a different area than the others.
Experts: Spy used AI-generated face to connect with targets LONDON (AP) — Katie Jones sure seemed plugged into Washington’s political scene. The 30-something redhead boasted a job at a top think tank and a who’s-who network of pundits and experts, from the centrist Brookings Institution to the right-wing Heritage Foundation. She was connected to a deputy assistant secretary of state, a senior aide to a senator and the economist Paul Winfree, who is being considered for a seat on the Federal Reserve. But Katie Jones doesn’t exist, The Associated Press has determined. Instead, the persona was part of a vast army of phantom profiles lurking on the professional networking site LinkedIn. And several experts contacted by the AP said Jones’ profile picture appeared to have been created by a computer program.