


https://wiki.hackerspaces.org/
Related: FABLABS, HACKING, libresHaving trouble grasping object-oriented programming? Read Plato. - Jason Salas' WebLog Appropriately, I've got a new "philosophy" when it comes to teaching new programmers about object-oriented programming (OOP). Not being a schooled computer scientist myself, I had a tough time when I was first learning OOP concepts and practices when I took up .NET, and many people learning the ropes of current-day coding apparently share the same frustrations. Fortunately, I've found a cool way of making the tough concepts easier to grasp, through the teachings of Plato. Specifically in his work with his theory about Forms, there are lots of cool analogies directly applicable to OOP one can ascertain from Plato's writing.
Poachers kill 300 Zimbabwe elephants with cyanide Poachers killed the elephants over the past three months by lacing waterholes and salt licks with cyanide. Animals are drawn to them during the dry season in the already arid and remote south-eastern section of the 5,660-square mile park. After the elephants died, often collapsing just a few yards from the source, lions, hyenas and vultures which fed on their carcasses were also struck down, as were other animals such as kudu and buffalo that shared the same waterholes. Zimbabwe's authorities say the cyanide has been planted by villagers who sell the elephants' tusks for around £300 each to cross-border traders. They can be resold in South Africa for up to £10,000 a pair, according to court papers relating one recent incident, sometimes re-emerging as carved artefacts such as bangles in Cape Town's craft markets. In 2011, at least 17,000 African elephants were killed for their tusks according to Cites, the international body that focuses on endangered species.
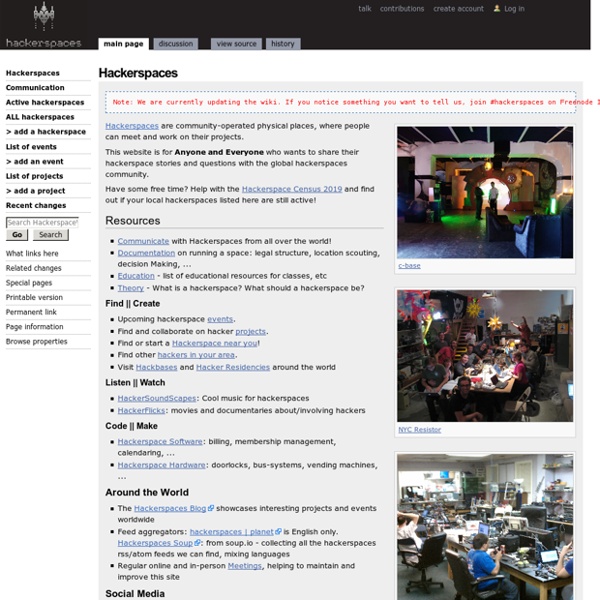
Search Whipcar for Montreal, canada Dear customers and friends, When we launched WhipCar in April 2010, we embarked on a very exciting mission. We were the first to offer car owners the chance to make better use of their cars and offset the rising costs of motoring by renting to their neighbours. We are sad to say that, at this time, we have decided to close WhipCar. In many ways, WhipCar has been a success. We were able to shift commonly-held perceptions of car sharing and ownership with the help of so many integral WhipCar community members. Hackerspace Software Running a hackerspace is a lot of work, and a lot of spaces have rolled their own software to automate some of that work. Most of that code is not maintainable enough to be reused by other spaces. To make things better, folks from the Metalab started their own hackerspace operating system and opensourced it.
ARTICLE : the secret world of hackers -En Hackerspaces are the digital-age equivalent of English Enlightenment coffee houses. They are places open to all, indifferent to social status, and where ideas and knowledge hold primary value. In 17th-century England, the social equality and merit-ocracy of coffee houses was so deeply troubling to those in power that King Charles II tried to suppress them for being "places where the disaffected met, and spread scandalous reports concerning the conduct of His Majesty and his Ministers". What if Aristotle Were a Software Engineer? Download sample - 59.9 KB Introduction In the late seventies, Marvel Comics, the famous comics publisher (of Spider-Man, Iron Man, Captain America, The Fantastic Four, and many others) published a new and rather unique series of comic books – the “What If…” series (“What if Spiderman Had Joined the Fantastic Four”, “What if Captain America Became President”, etc.), whose declared goal was to “explore the road never traveled”. The starting point of each book in that series was an extreme situation that went far beyond the usual narrative of Marvel Comics books. In this article, we will try to walk on the unexplored roads that those two words – what if – might open for us, but we, of course, will do it in another domain – the software design world. The title of this article implies that the imaginary situation that we are going to use is a situation where Aristotle is living in our time, working as a software engineer.
Gray whale dies bringing us a message — with stomach full of plastic trash Image Credit: Geograph / Richard Humphrey By: Brian, Live Free Live Natural. Open Source Blueprint for a Sustainable Civilization One Community is open source project-launch blueprinting and free-sharing everything needed to simultaneously address all the challenges currently facing humanity and build 7 different sustainable village prototypes for sharing it. The 7 village prototypes will be the first of a global cooperative of self-replicating teacher/demonstration hubs purposed to share and spread this model for comprehensive sustainability and collaborative global change for The Highest Good of All. Our initial focus is the following areas: More specifically, we are designing and free-sharing everything needed for duplication of each component and/or all of One Community including:
Theory Theory about hackerspaces comes from various disciplinary traditions and cuts across methodological and theoretical traditions. The following is therefore a loose and evolving set of links that reflect the diversity of interest in hackerspaces loosely organized from micro (individual) to macro concerns. Areas[edit] Learning theory - how can the activities in hackerspaces be seen as learning? Rafi Santo's hacker literacies video article Critical making Matt Ratto's critical making lab at the University of Toronto lab article Garnet Hertz' critical making book (art) Carl DiSalvo's work on adversarial design (design approach) Beth Kolko runs a program called "hackademia" Jentery Sayers tinker-centric pedagogies Critical theory and cultures of hackerspaces - what are are the intersections between hackerspaces and shared culture (F/OSS, hacker culture, etc.)? How do they relate to larger political and economic issues?