


Besoin de trouver un mot de passe... J'ai ça en stock depuis un bon moment maintenant et je me dis, pourquoi ne pas en faire profiter au lecteur de Korben.info ? Si vous cherchez le mot de passe de MSN Messenger, Windows Messenger (Windows XP), Yahoo Messenger (Version 5.x/6.x), ICQ Lite 4.x/2003, AOL Instant Messenger, AOL Instant Messenger/Netscape 7, Trillian, Miranda, et GAIM... Si vous voulez faire apparaitre un mot de passe caché derrière des asterisques (étoiles ******) ... Si vous avez perdu votre mot de passe de connexion à Internet, cliquez ici. Si vous cherchez à récupérer les mots de passe planqués dans Internet Explorer... Si vous avez besoin de trouver le mot de passe d'un accès réseau Windows... Si vous avez perdu votre mot de passe de messagerie, peu importe que vous utilisiez Outlook Express, Microsoft Outlook 2000, Microsoft Outlook 2002, IncrediMail, Eudora, Netscape Mail, Mozilla Thunderbird... Si vous cherchez votre clé WEP... Si vous avez besoin du mot de passe de votre session Accès au Bureau à distance...
HDDlife – программа для защиты ваших данных от сбоя жесткого диска! 21 Free Brochure Templates PSD, AI, EPS Download Found the best free brochure templates in psd, vector file format for free download which can be used in your design projects. From simple one page brochure to bi fold, tri fold brochures can be used for your business advertising. While business can be transformed through any kind of media these days, brochure templates can also be used for additional benefit on marketing a product. Photoshop, illustrator software are the requirement to edit these psd download files layer by layer. Modification and customization of these free brochure templates is possible as these templates are perfectly grouped for easy editing. It is advised to completely alter the files to get a unique brochure designed for your corporate firm or business. The magic thing about these brochure template is you can convert them to use with any kind of design purpose anytime. Find similar articles for graphic designs. Free Tri-fold Corporate Brochure PSD Download Tri-fold Brochure Template | Freebie PSD Download Download
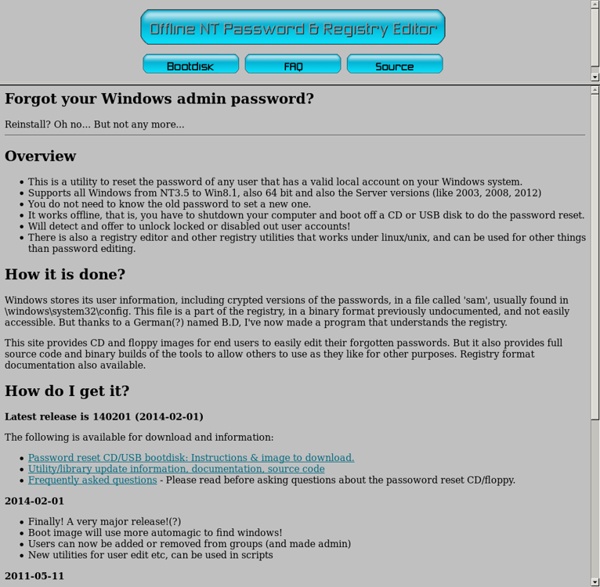
Ayawooga: Mot de passe Windows perdu ? Vous êtes sous Windows, et impossible de retrouver votre mot de passe... Voici comment vous sortir de ce mauvais pas : Tout d'abord, rassurez-vous : vos données ne sont pas perdues ! Vos données ne peuvent être perdues qu'en cas de vol, de défaillance du support de stockage (disque dur), ou (au cas échéant) de la perte de la clé de cryptage de ces données. Sachez que, au cas où votre système ne démarre plus (écran bleu, fichier de démarrage manquant, plantage, etc.), il est toujours possible de lire et de récupérer les données : on peut le faire à l'aide d'un "live CD" (voir la partie Vista ou Seven, plus bas) ou en adaptant le disque sur une autre machine (comme pour un disque externe).Si vous êtes sous Windows XP, cela peut être simple : Il suffit de démarrer en mode sans échec : (Re)Démarrez la machine et frappez longuement la touche F8 de votre clavier lors du démarrage. Si vous ne faites rien, au bout de quelques secondes, l'ordinateur démarrera comme d'habitude. Tutoriel source.
Типографская раскладка Ильи Бирмана Скачать для Виндоуса В архиве два инсталлятора: для русской и для английской раскладки. Что нового в версии 3.4 Исправлена ошибка: Альт+Шифт+дефис не писал короткое тире в английской раскладке. Установка, обновление, удаление Выполните оба файла setup.exe из дистрибутива по очереди. Что-то не так? При обновлении нужно сначала удалить старую раскладку. Раскладка удаляется в «Установке и удалении программ» после отключения в «Параметрах клавиатуры». Скачать для Мака Раскладка начинает работать в программах после их перезапуска. Что нового в версии 3.4.1 Исправлена ошибка при установке на «Эль-капитане». Search Tools with Open Source Code Free Search Engine Comparison by Yiling Chen, revised April 2006, compares Alkaline, Fluid Dynamics, Juggernautsearch, mnoGoSearch, Perlfect, SWISH-E, Webinator, and Webglimpse, concentrating on indexing, query processing, retrieval, and relevance.
How to build the best free PC security suite Editor's note: This article was updated in full in January 2016. If you have a PC, you’re a target. You need security software. That's as true today as it was a decade ago, despite significant security improvements to Windows over the years. But you have a choice—you can either continue paying the security software vendor of your choice an annual fee for protection or you can take matters into your own hands and build your own suite of security tools using free products. The pros and cons of free Going free can save you some cash, but it isn’t a panacea. Free products also often include browser toolbars or other add-ons that you might not necessarily want. If you can put up with those caveats, going the freebie route might be for you—just think of all the money you’re saving. Grab some antivirus software Antivirus software is the key component of any security suite, and for good reason—it’s going to be your primary defense against malware. Have a secondary antivirus app Use a firewall
7-Zip The Truth Behind Rodan + Fields (And Its Takeover of Your Facebook Feed) | Allure She's the friendliest neighbor on the block, the chicest mom at school, the Spin-class regular with glowing skin. The Rodan + Fields consultant has something she wants to sell you—and it's not just a face cream. You can't miss the row of matching white Lexus sedans and SUVs parked in the soft shadows outside the Terrace, a banquet hall in Paramus, New Jersey. The sun is setting behind the dozen or so vehicles, which have been arranged side by side, facing out, gleaming and glamorous in the twilight. In front of them, about the same number of women—many blonde, most in short dresses—pose with their arms around each other. Except that in this version, there's no man at the center. A Rodan + Fields consultant is the highly educated, digitally savvy update of the cosmetics saleslady who used to ring your mom's doorbell bearing frosted lip gloss and soap-on-a-rope. But the Rodan + Fields consultant's goal isn't only to hook you up with products. Then fate intervened.
The Best Data Recovery Software | MiniTool Power Data Recovery Sell Textbooks Online | We Buyback Your College Books for Cash Purge your bookshelf of old textbooks you're not reading and score more cash. Selling your textbooks online is a fast, easy, and smart way to make money, but selling your textbooks online with ValoreBooks is even smarter. With us you get: Highest textbook sellback prices. Our marketplace model connects you to hundreds of buyers who are looking to acquire your textbooks, meaning you get top dollar for your old textbooks-guaranteed. Better yet, if you find a better price somewhere else, let us know and we'll match it. Free shipping and easy order tracking. Biggest variety of textbook titles. Fast and flexible payment.
TorFlow – Visualisez en temps réel le trafic du réseau TOR TorFlow est un ensemble de script Python dont le but est de vous permettre d’analyser et de visualiser en temps réel le trafic du réseau Tor, à l’aide d’une magnifique carte interactive. Vous pourrez ainsi obtenir diverses informations concernant le routage, les nœuds performants ou engorgés et tout un tas d’autres choses intéressantes. Ce projet a (si j’ai bien compris) pour but ultime de construire un système de réputation automatisé, permettant de mettre à disposition des clients une sorte d’annuaire, afin que ces derniers puissent prendre les bonnes décisions de routage. Outre l’aspect technique et comme l’a fait remarquer Jose dans son billet, vu la popularité de Tor nous aurions pu nous attendre à voir des connexions dans le monde entier. Quoi qu’il en soit je ne connaissais pas encore ce projet qui a l’air vraiment, mais vraiment, très sympa… Les cartes roxent du poney. Si vous voulez voir ce que ça donne vous pouvez mater la carte en utilisant ce service web. Amusez-vous bien.
FAQs » US Dog Registry Below you will find some of the most frequently-asked questions about service dogs, emotional support dogs, therapy dogs, and our store policies. Service Dog Questions Is there any application to fill out? There are no applications to fill out and you do not need a doctor’s note. Can I have a service dog? If you have a disability (a physical or mental impairment that substantially limits one or more major life activities of such individual) then you are entitled to a service dog to do work or perform tasks for you. What breed of dog can be considered a service dog? Under ADA law any breed of dog can be considered a service dog. Do I have to pay any extra fees? No. Is PTSD covered? Yes, PTSD (Post-Traumatic Stress Disorder) is covered under ADA Laws and as long as your service dog is able to calm you during an anxiety attack then he/she is considered a service dog. Can I take my service dog anywhere? What if someone has a fear or allergy of dogs, will my service dog be allowed? Yes. No.
Effacez vos traces avec BleachBit Publié le 7 décembre, 2015 par Ahmed Des traces, vous n’en laissez pas seulement dans votre navigateur mais vous en laissez aussi dans la plupart des logiciels et système d’exploitation. Vous l’ignorez peut-être, mais toutes vos activités numériques sont enregistrées sur votre PC. Afin de protéger au mieux votre vie privée (et pas seulement effacer le cache de chrome !) BleachBit est un logiciel sous licence libre (GPL v3). De surcroît, il s’occupera de vider la corbeille et le presse-papiers, éliminer la liste des fichiers consultés récemment et supprimer tous les fichiers temporaires. Avant d’utiliser BleachBit, je vous conseille de noter quelque part vos identifiants et mot de passe… Télécharger BleachBit