


https://www.mozilla.org/en-US/lightbeam/
Related: Online Privacy5 ways to easily increase your internet security - Seattle Political Buzz In this age of technology nothing is private. In fact, NSA whistleblower William Binney recently stated that literally every email sent in the US is recorded by the FBI. For those living in reality, it has been know that since the 90's under President Clinton, programs such as Echelon monitored nearly every phone call, fax, and email in the United States. Sites like Facebook have been known to record users web history even when they are logged out.
12 Video Sites That Are Better Than YouTube There’s little doubt that YouTube is the go-to video site for many people. In fact, it’s one of the most popular websites in the world. But what if YouTube happens to be inaccessible? Protect Our Privacy Privacy Policy Last modified: November 11, 2011 This Privacy Policy is continually under review to ensure your privacy and security. This website, (the “Site”) is operated by Access (“We” or “Us”). Mozilla Foundation The Mozilla Foundation is a non-profit organization that exists to support and collectively lead the open source Mozilla project. Founded in July 2003, the organization sets the policies that govern development, operates key infrastructure and controls Mozilla trademarks and copyrights. It owns a taxable subsidiary: the Mozilla Corporation, which employs many Mozilla developers and coordinates releases of the Mozilla Firefox web browser and Mozilla Thunderbird email client. The subsidiary is 100% owned by the parent, and therefore follows the same non-profit principles. The Mozilla Foundation was founded by the Netscape-affiliated Mozilla Organization.
Facebook privacy and kids: Don’t post photos of your kids online Photo by Hemera/Thinkstock I vividly remember the Facebook post. It was my friend’s 5-year-old daughter “Kate,” (a pseudonym) standing outside of her house in a bright yellow bikini, the street address clearly visible behind her on the front door. A caption read “Leaving for our annual Labor Day weekend at the beach,” and beneath it were more than 50 likes and comments from friends—including many “friends” that Kate’s mom barely knew. The picture had been uploaded to a Facebook album, and there were 114 shots just of Kate: freshly cleaned and swaddled on the day of her birth … giving her Labradoodle a kiss … playing on a swing set. But there were also photos of her in a bathtub and an awkward moment posing in her mother’s lacy pink bra.
Social Marketing Blog / @flowtown This post was written by Jenny Urbano, our Social Media Manager. Here at Demandforce, we love seeing and celebrating your ideas! And more than that, we love to hear from YOU. We want to bridge the gap between us and you, so that’s why we’re offering a once in a lifetime opportunity to win a trip to San Francisco, sightsee in this amazing city, visit Demandforce headquarters and share your ideas with us! 6 winners, and a guest of their choice will be flown out to San Francisco, California on March 12-14th, 2014, where they will stay in Union Square, spend a day at Demandforce, have dinner with the team, and explore the lovely City by the Bay!
The convergence of biometrics, location and surveillance Applying biometric matching to location-based surveillance technologies produces both fascinating possibilities and scary scenarios. I recently spoke with Tactical Information Systems CTO Alex Kilpatrick and Mary Haskett, co-founder and president, about the state of biometrics and what we need to be concerned about as surveillance becomes more prevalent in our society. They’ll expand on many of these ideas during a session at the upcoming Where 2.0 Conference. Our interview follows. Mozilla Mozilla is a free software community best known for producing the Firefox web browser. The Mozilla community uses, develops, spreads and supports Mozilla products, thereby promoting exclusively free software and open standards, with only minor exceptions.[1] The community is supported institutionally by the Mozilla Foundation and its tax-paying subsidiary, the Mozilla Corporation.[2] In addition to the Firefox browser, Mozilla also produces Thunderbird, Firefox Mobile, the Firefox OS mobile operating system, the bug tracking system Bugzilla and a number of other projects. History[edit] In a report released in November 2012, Mozilla reported that their total revenue for 2011 was $163 million, which was up 33% from $123 million in 2010. Mozilla noted that roughly 85% of their revenue comes from their contract with Google.[14]
How to foil NSA sabotage: use a dead man's switch The more we learn about the breadth and depth of the NSA and GCHQ's programmes of spying on the general public, the more alarming it all becomes. The most recent stories about the deliberate sabotage of security technology are the full stop at the end of a sentence that started on 8 August, when the founder of Lavabit (the privacy oriented email provider used by whistleblower Edward Snowden) abruptly shut down, with its founder, Ladar Levison, obliquely implying that he'd been ordered to secretly subvert his own system to compromise his users' privacy. It doesn't really matter if you trust the "good" spies of America and the UK not to abuse their powers (though even the NSA now admits to routine abuse), you should still be wary of deliberately weakened security. It is laughable to suppose that the back doors that the NSA has secretly inserted into common technologies will only be exploited by the NSA. One important check against the NSA's war on security is transparency.
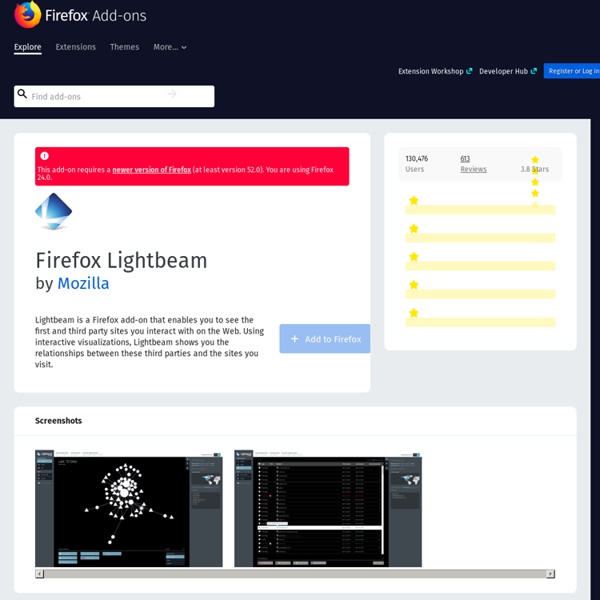
33 Firefox Addons Made Popular by Users You know Firefox is the most popular browser of all time and there are a lot reasons for this kind of popularity.I think one of the most important thing is the Firefox Addons.We can find hundreds of addons for our needs and of course it is impossible to use all of them.Once a week i check Firefox Addon web site and i look for interesting and useful addons for myself to use. Today i wanna share 33 Firefox Addons which you know most of them but it may be good to try some of them. 1.Aviary Screen Capture & Quick Launch
Scott Adams Blog: Noprivacyville 03/15/2011 I heard a report on NPR about an auto insurance company giving drivers the options of putting GPS tracking devices on their vehicles to lower insurance rates by as much as 30%. The idea is that, for example, the device could confirm to the insurance company that the car wasn't being used in high risk situations, such as commute traffic. Safe driving situations would be rewarded with lower rates.