


http://www.port7alliance.com/txt/hackbg.html
Related: hackingThe glider: an Appropriate Hacker Emblem The Linux folks have their penguin and the BSDers their daemon. Perl's got a camel, FSF fans have their gnu and OSI's got an open-source logo. What we haven't had, historically, is an emblem that represents the entire hacker community of which all these groups are parts. This is a proposal that we adopt one — the glider pattern from the Game of Life. About half the hackers this idea was alpha-tested on instantaneously said "Wow! How To Become A Hacker Copyright © 2001 Eric S. Raymond As editor of the Jargon File and author of a few other well-known documents of similar nature, I often get email requests from enthusiastic network newbies asking (in effect) "how can I learn to be a wizardly hacker?". Back in 1996 I noticed that there didn't seem to be any other FAQs or web documents that addressed this vital question, so I started this one. A lot of hackers now consider it definitive, and I suppose that means it is. Still, I don't claim to be the exclusive authority on this topic; if you don't like what you read here, write your own.
20 brilliant things to make in a jar Via: mycakies.blogspot.com Start saving your old jam jars! From cakes to herb gardens, pies to photo frames, and even entire meals … here are 20 fantastic things you never knew you could make with a jar. (Above: red velvet cupcakes in a jar. Get the recipe here). Via: fatgirltrappedinaskinnybody.blogspot.com Cracking Wep Keys With BackTrack Article at HellBound Hackers This is my first tutorial.... I hope this helps all of you that just don\'t know where to start or don\'t know how to crack wep... What you will need * 1 copy of BackTrack 3 *newest release* (GOOGLE IT) * 1 wireless router * Laptop with wireless capabilities/wireless card -- There are a few cards that can\'t do the injection!!! * A secure place to work (so you don\'t disturb other AP\'s) In order to crack a WEP key you must have a large number of encrypted packets to work with.
The 10 Most Ridiculously Awesome Geeky Computer Pranks Everybody loves a good prank… unless you are the one on the receiving end of the fun. It’s time to hone your pranking skills, not just to make sure you are the best, but so you can avoid being pranked by others. Yeah, sure, we could go with the old standards, like a blue screen of death screensaver or something like that, but it’s time to use our geek skills and come up with something better. We’ll cover some of the old favorites too, but maybe with a twist. Note: Many of these pranks require being able to access somebody’s computer physically, and many others require them to leave their PC logged in and unattended. You’ll have to plan accordingly.
How to Hack Someones IP Address 2014 - Come to Hack Most of you may be curious to know how to find the IP address of your friend’s computer or to find the IP address of the person with whom you are chatting in Yahoo messenger or Gtalk. Finding out someone's IP address is like finding their phone number, an IP address can be used to find the general location where that person lives. Now while most of the tutorials on the net teach you how to steal an ip address via MSN, or any other chat software, in this post I’ll show you how to find IP address of someones computer using script. Using this method for hacking someones ip adress is very easy and effectively, so just follow the steps bellow. NOTE: This tutorial is for educational purposes only, I am NOT responsible in any way for how this information is used, use it at your own risk. How to Hack Someones IP Address?
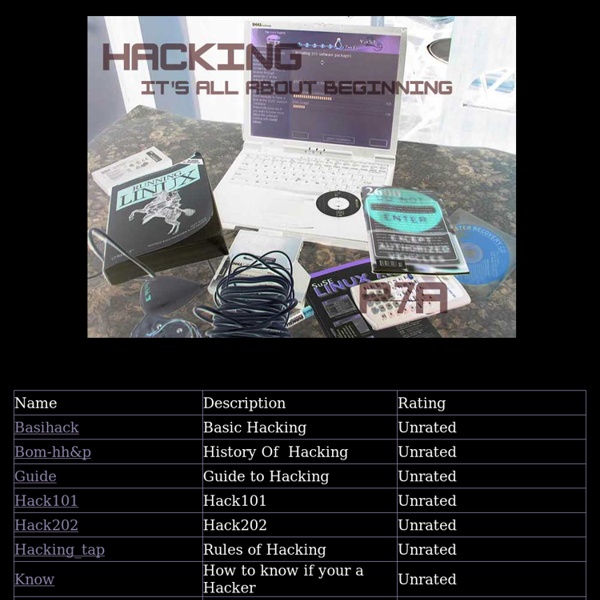
80+ Best Free Hacking Tutorials Learning to become hacker is not as easy as learning to become a software developer. I realized this when I started looking for learning resources for simple hacking people do. Even to start doing the simplest hack on own, a hacker requires to have in depth knowledge of multiple topics. Perfect Summer Bangle Here's a fun tutorial on how to make a message bangle that's one-of-a-kind, done in the sun, waterproof and weatherproof. Even after several trips to the beach, it won't fade or wash off! Essentially, it's the Perfect Summer Bangle. Used in this tutorial: Inkodye Red
aircrack-ng Description Aircrack-ng is an 802.11 WEP and WPA/WPA2-PSK key cracking program. Aircrack-ng can recover the WEP key once enough encrypted packets have been captured with airodump-ng. This part of the aircrack-ng suite determines the WEP key using two fundamental methods. 100 Extensive University Libraries from Around the World that Anyone Can Access Universities house an enormous amount of information and their libraries are often the center of it all. You don't have to be affiliated with any university to take advantage of some of what they have to offer. From digital archives, to religious studies, to national libraries, these university libraries from around the world have plenty of information for you. Digital Libraries Capturing images of manuscripts, art, and artifacts, digital libraries are an excellent way of both preserving the past and sharing it with everyone.