


How to use blocked proxies and torrent sites « KickassTorrents Homepage – latest updates and reviews After several file sharing websites have been made unavailable by ISPs in the UK, loads of proxies emerged to make sure that individuals could still get access. ISPs reacted to demands by blocking those proxy websites also. This has lead us to a fresh service that makes torrent pages reachable and furthermore, it makes possible to use the blocked proxies. This unique service is Immunicity. Though it has always been the US fighting against online piracy and developing copyright laws, UK has recently stood out to censor the web.
20 Best Websites To Download Free EBooks We understand that reading is the simplest way for human to derive and constructing meaning in order to gain a particular knowledge from a source. This tendency has been digitized when books evolve into digital media equivalent – E-Books. It would be nice if we’re able to download free e-book and take it with us. That’s why we’ve again crawled deep into the Internet to compile this list of 20 places to download free e-books for your use. Great Websites to Download Ebooks FreeBookSpot 5 Ways To Download Torrents Anonymously With anti-piracy outfits and dubious law-firms policing BitTorrent swarms at an increasing rate, many Bittorrent users are looking for ways to hide their identities from the outside world. To accommodate this demand we'll give an overview of 5 widely used privacy services. With an increasing number of BitTorrent users seeking solutions to hide their identities from the outside world, privacy services have seen a spike in customers recently. Below we’ve listed some of the most-used services that allow BitTorrent users to hide their IP-addresses from the public.
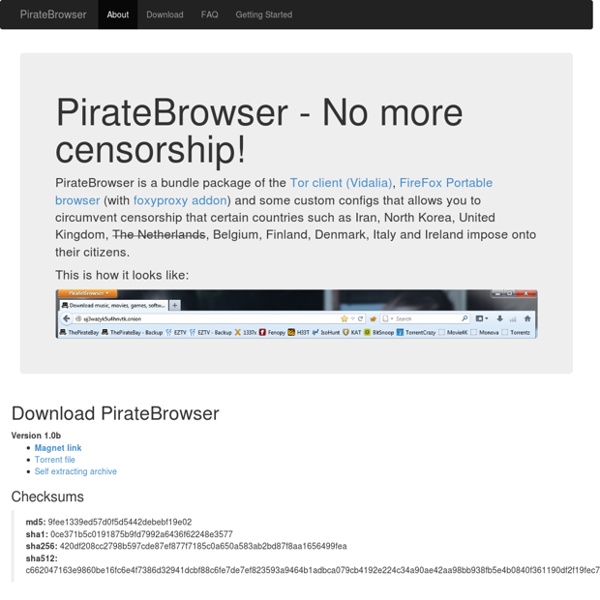
www.tubeoffline.com/download-RedTube-videos.php#.VJBQ1iuG-Sr Download videos from RedTube to your computer Make sure it is in this format: Important: Please make sure you have Java enabled and updated for this download to work. Most computers already have Java by default. How The Pirate Bay Plans to Beat Censorship For Good The Pirate Bay's PirateBrowser just hit 2.5 million downloads but the notorious torrent site has much bigger plans in store for the new year. The team behind the site is developing a new tool that doesn't rely on domain names or server farms. Instead, users will serve as the P2P hosts of the sites, with the system running its own alternative DNS. Today, the Pirate Bay team shares some more details on the technology. Over the past few years The Pirate Bay has had to deal with its fair share of censorship, mostly through court-ordered blockades.
G2A.COM Marketplace How does it work in practice Copy your Unique Token Contact our Support Verify your token live The refund process will be completed within 72 hours. That time is needed for a detailed verification. Download Tor Want Tor to really work? You need to change some of your habits, as some things won't work exactly as you are used to. Please read the full list of warnings for details.
How to torrent anonymously with the Six Strikes law - Seedbox Guide Five top US internet service providers are, as of the 25th of February, now monitoring your internet traffic for torrent activity. As part of the six strikes law, they will send you six warnings. After those, your internet connection will be crippled.