


GC1M2NP A Lesson in Ciphers # 1 (Unknown Cache) in Missouri, United States created by TripCyclone This cache series is designed to give you an introduction to the world of ciphers. It will not cover every type of cipher out there, instead focusing on a small variety of different ciphers. Hopefully, you will walk away from solving this series with a new set of puzzle solving skills. And maybe, just maybe, you'll be able to go to that puzzle that's always bothered you and begin to see it with a new pair of eyes. I have designed this series such that you will not be able to solve them all in one swipe. How you may ask? Cryptography is defined as the practice and study of hiding information. For your first lesson, we'll use a cipher that I am certain ALL OF YOU have used already. abeguguveglrvtugqrterrfsvsglsbhecbvaggjbbarguerr jrfgavarglsbheqrterrfguveglguerrcbvagmrebsviravar You are looking for a small lock 'n lock container.
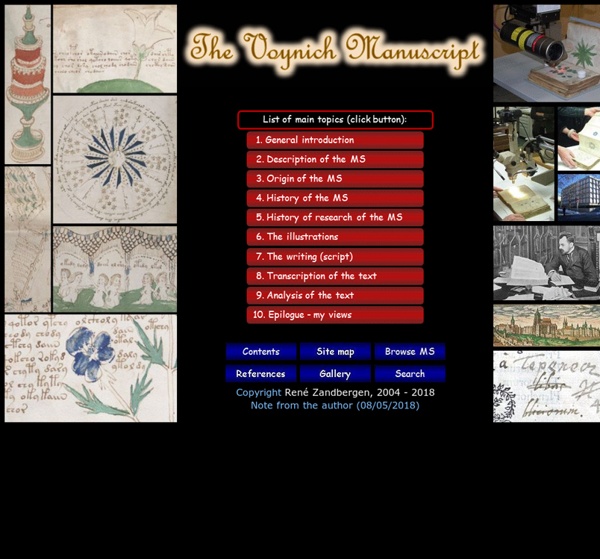
The Voynich Manuscript Decoded? I give examples to show that the code used in the Voynich Manuscript is probably a series of Italian word anagrams written in a fancy embellished script. This code, that has been confusing scholars for nearly a century, is therefore not as complicated as it first appears. All attempts over the past century to decode this mysterious manuscript have met with failure. Determine the language used in writing the manuscript Correlate the Voynich alphabet with the modern English alphabet Decipher the code If Leonardo da Vinci was the author of the VM, he would have used the language of Dante, i.e. medieval Italian, so I have assumed the VM language to be Italian. The Italian alphabet does not use the letter X. Povere leter rimon mist(e) ispero Which translates into English as follows: Plain letter reassemble mixed inspire This brief sentence indicated that the use of anagrams should be investigated.
MP3Stego When looking at the steganographic tools available on the Net, it occurred to me that nothing had been done to hide information in MP3 files, that is sound tracks compressed using the MPEG Audio Layer III format. There is a growing interest world-wide in MP3 or indeed WMA files because they offer near-CD quality at compression ratio of 11 to 1 (128 kilobits per second). This gives a very good opportunity for information hiding. Although WMA has better quality in general, I did not have access to code and only an implementation for MP3 is provided as a proof of concept. MP3Stego will hide information in MP3 files during the compression process. The hiding process takes place at the heart of the Layer III encoding process namely in the inner_loop. We have discussed earlier the power of parity for information hiding.
Le mystère du manuscrit de Voynich Le célèbre manuscrit de Voynich est un véritable casse-tête depuis près de cinq siècles : le texte n'a pas de titre, nous ignorons qui l’a écrit et sa langue nous est inconnue ! À ce jour, personne n’a percé la totalité des secrets de cet étrange document. Il s’agit de l’un des manuscrits les plus mystérieux de l’Histoire : son contenu demeure indéchiffrable et a fait l'objet de nombreuses recherches et hypothèses…infructueuses… Son origine est également sujette à de nombreuses interrogations. Est-ce un canular,un livre codé, un authentique travail scientifique du Moyen Age ? Son nom vient du collectionneur et bibliophile, Wilfrid Voynich, qui le (re) découvrit en 1912, parmi une collection de manuscrits anciens conservés dans la Villa Mondragone, à Frascati, près de Rome. Le manuscrit est conservé à la Bibliothèque Beinecke de l’université Yale. Découverte du manuscrit Une lettre troublante Athanasius Kircher (~ 1601 à 1680) était l'un des hommes les plus savants de son époque.
Cryptography When I wrote my first book, Fermat’s Last Theorem, I made a passing reference to the mathematics of cryptography. Although I did not know it at the time, this was the start of a major interest in the history and science of codes and code breaking, which has resulted in a 400-page book on the subject, an adaptation of the book for teenagers, a 5-part TV series, numerous talks and lectures, the purchase of an Enigma cipher machine and the development of an interactive crypto CD-ROM. In the Crypto Corner, you will find details about my book on cryptography (The Code Book), information about my TV series based on the book (The Science of Secrecy) and you can explore the Black Chamber, which is an interactive encryption and codebreaking section. You will also find a section about the Cipher Challenge, there are some cryptograms (coded messages) for you to try and crack, a free downloadable CD-ROM version of The Code Book, and a quick Q&A based on the questions I am most often asked.
Littérature - L'énigme séculaire du manuscrit de Voynich J’en perds mon latin! Après le disque de Phaistos, on continue sur notre lancée en abordant un autre grand mystère irrésolu: celui du manuscrit de Voynich, un livre mystérieux de 234 pages. En 1912, un amateur éclairé de littérature polonaise, Wilfrid M. Seule piste pour nous permettre de comprendre l’origine de ce mystérieux texte, une lettre en latin datée de 1666 accompagnant le manuscrit. Des pages apparemment consacrées à la botanique – Manuscrit de Voynich Roger Baco, Rodolphe II, les jésuites: voilà de nombreuses pistes pour commencer notre investigation! – Mince… On m’aurait menti? Quant aux tentatives de décryptage du texte, des centaines, voire des milliers d’experts en tout genre s’y sont essayés à travers les siècles… Aucun n’a réussi et le manuscrit reste encore et toujours une énigme! Certains experts s’accordent à dire que le manuscrit de Voynich n’est qu’une supercherie. L’astrologie sur le manuscrit de Voynich Un documentaire diffusé sur Arte sur le manuscrit de Voynich:
Sharky's Vigenere Cipher This page is for amusement only. Instructions are given below this form. instructions: Enter the string to encrypt or decrypt in the Input field (you may copy and paste it from another text editor). Enter the key in the Key field. On most computers: To copy: Highlight text, press Ctrl-C; To paste: Position cursor, press Ctrl-V. explanation: Vigenere coding is one of the most ancient forms of cryptography. Choose a key that is as long as the plaintext message. Unfortunately, these steps take all the fun out of the Vigenere cipher. Vigenere ciphers with moderate keys are appropriate for situations that do not require failproof security. We hope you enjoy this simple JavaScript-based implementation. Le manuscrit de Voynich Decrypté par un membre du Blog De l’Etrange ? | Le Blog De L'Etrange Petit Récapitulatif: Le manuscrit de Voynich est un livre illustré écrit entre 1408 et 1436 à l’aide d’un alphabet inconnu par un auteur inconnu. Le mystère demeure entier quant à la nature exacte de ce manuscrit puisque les thèses les plus diverses s’affrontent. Certains le jugent authentique, et émettent des théories pour expliquer son apparente inintelligibilité pour les chercheurs et soutenir l’hypothèse d’un contenu signifiant. D’après les travaux de Gordon Rugg, il pourrait aussi s’agir d’une supercherie. Le livre tire son nom d’un de ses anciens propriétaires, Wilfrid M. En 1962, Hans Kraus fait une description du manuscrit sur son catalogue de vente. L’intégralité du manuscrit a été publiée pour la première fois par un éditeur français en octobre 2005. Voici le Mail que j’ai Reçu. [toggle title="j'ai cassé le code du Manuscrit de Voynich!!!"
Keyed Caesar One variation to the standard Caesar cipher is when the alphabet is "keyed" by using a word. In the traditional variety, one could write the alphabet on two strips and just match up the strips after sliding the bottom strip to the left or right. To encode, you would find a letter in the top row and substitute it for the letter in the bottom row. For a keyed version, one would not use a standard alphabet, but would first write a word (omitting duplicated letters) and then write the remaining letters of the alphabet. This encoder will let you specify the key word that is used at the beginning of the alphabet and will also let you shift the keyed alphabet around, just like a normal Caesar cipher. This is your encoded or decoded text:
Le mystérieux manuscrit Voynich Le mystérieux manuscrit Voynich Le manuscrit Voynich apparaît le 19 août 1666, lorsque le recteur de l'Université de Prague, Joannes Marcus Marci, l'envoie au célèbre jésuite Athanase Kircher qui était entre autres choses spécialiste de cryptographie. Il se présente comme un octavo de 15 cm sur 27, la couverture manque et selon la pagination, vingt-huit pages sont perdues. " Le manuscrit de Voynich est un livre ancien écrit à l'aide d'un alphabet inconnu, et dont le sujet reste également un mystère. Le livre tire son nom d'un de ses anciens propriétaires, Wilfrid M. Le manuscrit est conservé à la Bibliothèque Beinecke de l’université Yale. L'intégralité du manuscrit a été publiée pour la première fois par un éditeur français, Jean-Claude Gawsewitch, en octobre 2005, afin que le grand public puisse enfin avoir accès tant au mystérieux texte qu'aux énigmatiques images
Home - www.simplesite.com/the_runes “For me the magic moment came on page 2 where the green picture could mean any of three things. I identified the picture almost at once but could not see in which of the three directions it might go. And I knew that I had to find out!” “This should come with a warning label on it. ...It's highly additive. “I took it to Rome with me and sought inspiration in the Forum.... ................. aaaagh, there's no escaping the clutches of the Runes!” “It took three pages before I was fully sold on this. “What I have enjoyed is the step-by-step developments of the first few pages leading into the greater challenges as you realise that there is more to each puzzle than you were first led to think - and the buzz of discovery when you realise how it actually works.” ”This is one of the most complex puzzles I have ever encountered. “I am proud to say that I have had my first Eureka moment when everything just slotted into place. “I’m totally intrigued with this puzzle.
Hypothese slave UK | England | Carvings riddle stumps villagers Puzzled residents across Yorkshire are turning detective after mysterious stone heads were left outside their properties in the dead of night. The sculptures feature the same carved symbol and come with a riddle attached. Despite CCTV film showing a man leaving three heads outside a post office, their origin remains unknown. So far, 12 have appeared in Goathland and Kilburn, North Yorkshire; four in Arthington, West Yorkshire and three in Braithwell in South Yorkshire. Each of the heads, which are up to a foot tall, looks different but all feature the same carving - which appears to spell out the word "paradox" - and a note bearing the riddle: "Twinkle twinkle like a star does love blaze less from afar?" The villages they have been found in are up to 50 miles from each other. Mike and Valerie Hoyes, who run a post office in Braithwell, found three heads outside their business on the morning of 23 August. Mrs Hoyes said: "It's very weird. Stonemasons quizzed
As far as the Voynich Manuscript, the vast majority of researchers focused on trying to decipher the code letter. Great respect for them. According to me , the text is intentionally used a hoax aimed to engage readers in a fruitless search for the code of the manuscript just as deliberately scattered like puzzle Centuries of Nostradamus. I am in my searches focused on the symbolic meaning of illustration. For someone who has only a scientific look at the issue of encryption, all suggest it may seem too unreliable, not falsifiable. Manuscript, namely the part of Herb is, according to me, a compendium of knowledge about the Evolution of Life on Earth - from its cosmological aspect, through Human Evolution (Theory Darwin ) to the Prehistory, History and Contemporary. In the following section, the author Herb encrypted all the important events of our common history with such precision that many a textbook of history might have envied accuracy. For more information: by grzegorzostrowski Feb 2