


reality interaction Over the past two decades, HCI researchers have developed a broad range of new interfaces that diverge from the "window, icon, menu, pointing device" (WIMP) or Direct Manipulation interaction style. Development of this new generation of post-WIMP interfaces has been fueled by advances in computer technology and improved understanding of human psychology. Some examples of these post-WIMP interaction styles are: virtual, mixed and augmented reality, tangible interaction, ubiquitous and pervasive computing, context-aware computing, handheld, or mobile interaction, perceptual and affective computing as well as lightweight, tacit or passive interaction. beachbodycoach Team Beachbody CANADA Guest Sign In javax.portlet.title.56S Teambeachbody.com - United States
Social Media Timeline Last week, Dr. Sean Carton, the Chief Creative Officer of our web division (idfive), posted the following Social Media Timeline graphic at the idfive blog - attentionscan.com. Sean created the graphic as part of his preparation for speaking at the 2009 eduWEB conference in Chicago. Sean wrote: "It's definitely NOT to scale and I'm sure that plenty of people could quibble with what I chose to include as examples of "social media," (I define "social media" as "technologies that facilitate conversations") but I think it provides a pretty interesting overview of where this stuff came from and how long it's been around."
Worksheet Generators Addition (Basic) Generator Create basic addition drill-and-practice pages with 25 or 50 problems on a page. This generator creates worksheets with single-digit problems. (example: 7 + 8) Addition (Advanced) Generator 7 Indigenous Voices You Need to Know About on this Indigenous Peoples Day Today across Turtle Island (also known as the United States), millions are celebrating the resiliency within themselves and within their communities. They are celebrating and honoring those that came before them and those that will come after them. They are celebrating perseverance and determination. logiciel d'immixtion (multi-Etats) Map showing the number and geographical location of Flame infections detected by Kaspersky Lab on customer machines. Courtesy of Kaspersky A massive, highly sophisticated piece of malware has been newly found infecting systems in Iran and elsewhere and is believed to be part of a well-coordinated, ongoing, state-run cyberespionage operation. The malware, discovered by Russia-based antivirus firm Kaspersky Lab, is an espionage toolkit that has been infecting targeted systems in Iran, Lebanon, Syria, Sudan, the Israeli Occupied Territories and other countries in the Middle East and North Africa for at least two years. Dubbed “Flame” by Kaspersky, the malicious code dwarfs Stuxnet in size — the groundbreaking infrastructure-sabotaging malware that is believed to have wreaked havoc on Iran’s nuclear program in 2009 and 2010. Kaspersky Lab is calling it “one of the most complex threats ever discovered.”
How to Remove Trovi / Conduit / Search Protect Browser Hijack Malware If your computer has been hijacked with an obnoxious malware that won’t let you change your home page, there’s a strong chance you’ve been infected with the Trovi Search Protect malware, which used to be known as Conduit. Here’s how to remove it. How do you know this is malware? Instead of installing like it should, as a Google Chrome Extension, you’ll probably see that your extensions list doesn’t mention Trovi or Conduit at all.
China–France relations China–France relations, also known as Sino-French relations or Franco-Chinese relations, refers to the interstate relations between China and France (Kingdom or later). Note that the meaning of both "China" and "France" as entities has changed throughout history; this article will discuss what was commonly considered 'France' and 'China' at the time of the relationships in question. There have been many political, cultural and economic relationships between the two countries.
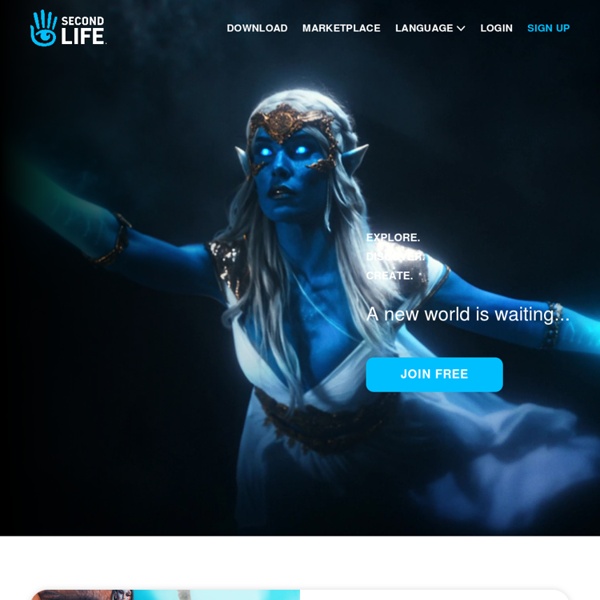
A free virtual 3D world which where you can participate in both social and professional discussions with those with similar interests by raviii May 13