

NetCat tutorial: Day1 [Archive] - Antionline Forums - Maximum Security for a Connected World. NetCat tutorial: Day1 [Archive] - Antionline Forums - Maximum Security for a Connected World. Ncat for Netcat Users. Contents: Introduction: With the release of Nmap 5.00, the new Ncat tool has been officially released.
Ncat is meant to be a modern implementation of Netcat using Nmap's mature networking libraries, combining the best features of the various Netcat derivatives into one new tool. While Ncat is an extremely versatile tool with many amazing new features, it is not quite 100% reverse-compatible with the original Netcat. I decided that it would be helpful to make some kind of chart or guide mapping how to do common Netcat tasks using Ncat, and this is the result. Some of the new features in Ncat compared to the original Netcat are: IPv6 supportSSL supportProxy support (both using a proxy and acting as one!) General Tips: As of Ncat 5.20, the "-p" option can now be used to specify the local port to listen on in listen mode, in order to be reverse-compatible with the original Netcat. Nmap Development: Re: Your favorite Ncat/nc/Netcat trick?
Nmap Development mailing list archives Re: Your favorite Ncat/nc/Netcat trick?
From: Ron <ron () skullsecurity net> Date: Mon, 02 Mar 2009 10:10:59 -0600 David Fifield wrote: Hello again, I'd like to have some more examples of fun, useful, or unusual things to do with Ncat. I have a few of them, based on my own limited experience, at What's your favorite Ncat trick? Here's one I thought about last night... This lets me, for example, monitor my router's traffic, and push it all back to my laptop where I can use wireshark to get a graphical view. Ron _______________________________________________ Sent through the nmap-dev mailing list Archived at By Date By Thread. Nmap Development: Re: Your favorite Ncat/nc/Netcat trick? Re: Your favorite Ncat/nc/Netcat trick? - ReadList.com. Datacom netcat 800 lan troubleshooter tester w/ remote. Cedar Rapids Free Classifieds and Ads > Industrial Equipment > Cedar Hills > Datacom netcat 800 lan troubleshooter tester w/ remote Datacom netcat 800 lan troubleshooter tester w/ remote Contact: ina.cleveland@cedar--rapids.com (Ina Cleveland) (actual email hidden) Contact ina.cleveland@cedar--rapids.com (Ina Cleveland) for more information.

Flag any violation to moderator. Netcat_cheat_sheet_v1.pdf. OpenBSD manual pages. Nc — arbitrary TCP and UDP connections and listens The nc (or netcat) utility is used for just about anything under the sun involving TCP, UDP, or UNIX-domain sockets.
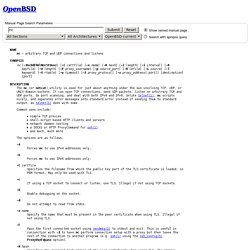
It can open TCP connections, send UDP packets, listen on arbitrary TCP and UDP ports, do port scanning, and deal with both IPv4 and IPv6. Unlike telnet(1), nc scripts nicely, and separates error messages onto standard error instead of sending them to standard output, as telnet(1) does with some. Common uses include: simple TCP proxies shell-script based HTTP clients and servers network daemon testing a SOCKS or HTTP ProxyCommand for ssh(1) and much, much more The options are as follows: Forces nc to use IPv4 addresses only. Forces nc to use IPv6 addresses only. -C certfile Specifies the filename from which the public key part of the TLS certificate is loaded, in PEM format.
-c If using a TCP socket to connect or listen, use TLS. Enable debugging on the socket. -d Do not attempt to read from stdin. Mutillidae: Bypass Authentication using SQL Injection. Web Application Pen-testing Tutorials With Mutillidae (Hacking Illustrated Series InfoSec Tutorial Videos) Web Application Pen-testing Tutorials With Mutillidae When I started the Mutillidae project it was with the intention of using it as a teaching tool and making easy to understand video demos.

Truth be told, I never did as much with it as I intended. However, after Jeremy Druin (@webpwnized) took over the development it really took off. I have since come to find out he has been doing A LOT of YouTube video tutorials with Mutillidae, which he said I could share here. I will be copying his descriptions with slight editing and embedding his videos below: Index: Determine Http Methods Using Netcat Using Mutillidae as a target, we look at discovering the HTTP methods offered by a web server during the discovering phase.
Click To Load Video. Mutillidae: Determine HTTP Methods using Netcat.