


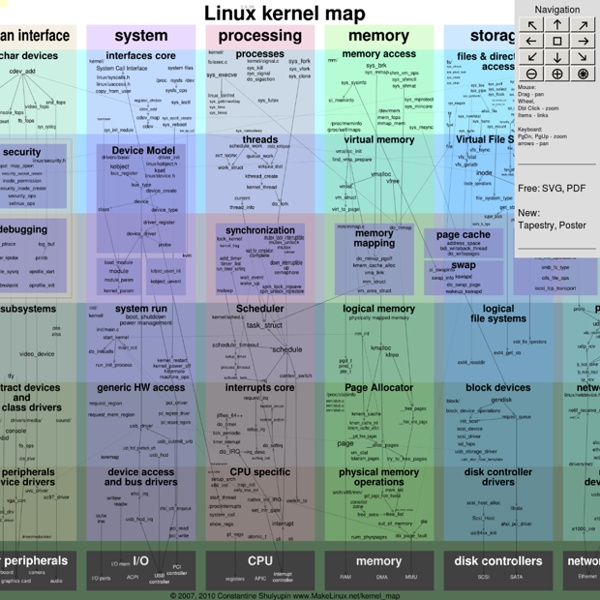
http://www.makelinux.net/kernel_map/
Related: kernelLinux Directory Structure (File System Structure) Explained with Examples by Ramesh Natarajan on September 8, 2010 Have you wondered why certain programs are located under /bin, or /sbin, or /usr/bin, or /usr/sbin? For example, less command is located under /usr/bin directory. Why not /bin, or /sbin, or /usr/sbin? Stupid Windows 7 trick: unlock the secret God Mode folder So, what exactly is God Mode in Windows 7? Well, for starters, it's not really a mode. And it's nothing you need to be a deity to pull off, either. Rather, it's a folder packed with shortcuts to just about every settings change and administrative function in Windows 7. Everything you'll find in the Action Center, Backup and Restore, Autorun, Desktop Gadgets, Devices and Printers -- it's all there.
Writing Your Own Toy OS (Part I) "Linux Gazette...making Linux just a little more fun!" By Krishnakumar R. This article is a hands-on tutorial for building a small boot sector. Why Linux is better PDFBEAR is founded by the team behind WhyLinuxIsBetter.net, which brings tons of experience in user conversion tools. We have decided to change our focus to helping and improving how our users convert files on all platforms including Linux. About WhyLinuxIsBetter.net Steps for contributing to the Linux Kernel One of the biggest—and the fastest moving—open source projects, the Linux kernel, is composed of about 53,600 files and nearly 20-million lines of code. With more than 15,600 programmers contributing to the project worldwide, the Linux kernel follows a maintainer model for collaboration. In this article, I'll provide a quick checklist of steps involved with making your first kernel contribution, and look at what you should know before submitting a patch. For a more in-depth look at the submission process for contributing your first patch, read the KernelNewbies First Kernel Patch tutorial. Contributing to the kernel
Compare Features PREMIUM Service If you want more, you can get more - including the ability to sync Tasks, Contacts and multiple Google Calendars. Upgrade your account today and get advanced synchronization at the touch of a button. Sign Up Linux Directory Structure (File System Structure) Explained with Examples by Ramesh Natarajan on September 8, 2010 Have you wondered why certain programs are located under /bin, or /sbin, or /usr/bin, or /usr/sbin? For example, less command is located under /usr/bin directory. Why not /bin, or /sbin, or /usr/sbin? 4 Ways to Increase Your Traffic With StumbleUpon StumbleUpon is one of the best traffic generators among the top seven social media sites, referring more than other social bookmarking and voting sites such as Digg and Reddit according to Statcounter. Why? Because when a user likes, or stumbles, a particular page, it is put into the StumbleUpon lineup. As other StumbleUpon users are randomly searching for new content on a specific topic using the Stumble button on their toolbar, any pages in the lineup for that topic will be displayed to them. So how can you capitalize on this great network and start getting traffic? Great Content
Anatomy of the Linux kernel – IBM Developer Given that the goal of this article is to introduce you to the Linux kernel and explore its architecture and major components, let’s start with a short tour of Linux kernel history, then look at the Linux kernel architecture from 30,000 feet, and, finally, examine its major subsystems. The Linux kernel is over six million lines of code, so this introduction is not exhaustive. Use the pointers to more content to dig in further. A short tour of Linux history Linux or GNU/Linux? Making TUGZip Shell Extensions Work In Vista x86_64 For those of you that don’t know what TUGZip is, it’s a free archiving utility (think WinZip) developed by Christian Kindahl which is also the developer of my favorite burning software InfraRecorder . And honestly, the only reason why I found out about TUGZip is because of it’s link in the InfraRecorder website. If it wasn’t there I would have never, ever…found out about TUGZip. I’d be stuck using 7-Zip forever, never knowing that a aesthetically pleasing application like TUGZip existed. I mean 7-Zip works fine for me, it’s just that it doesn’t really look 2.0′ish to me if you get my drift. Now, people that use TUGZip in a x86_64 system specifically Vista know that TUGZip’s 32-bit shell extensions do not work in x86_64 versions of Vista, meaning that when you right-click in Windows Explorer, nothing shows up.
Understanding Middleware with Apache ActiveMQ Even though “middleware” might seem like a close cousin of Tolkien’s Middle Earth, it’s a fairly modern term in computer software and services, and has nothing to do with hobbits, wizards or adventures involving a ring. Middleware is nothing but software that literally sits “in the middle”, like a bridge, between other software. Read on as I shed light on one specific example of middleware, Apache ActiveMQ. Before we explore Apache’s middleware offering, it’s important to know the various types of middleware out there. How a 3 Month Old Website Received 958,373 Visits from Google 254 Comments 6 minutes I receive a lot of emails from people who ask whether, with all of the competition online, it’s still possible to enter a niche right now and make money. I won’t deny that it’s getting much, much harder in the affiliate marketing space (how I make money) but persistence, determination and creativity can take you anywhere. Did you know that 20-25% of Google searches every single day are brand new?
Form Design with Sliding Labels « CSSKarma A few weeks ago I was reading an article on form UI by Luke Wroblewski of Yahoo!. For those who aren’t familiar with Luke, he (quite literally) wrote the book on good form design. In the article, one certain section about placing labels inside of form fields stood out to me: Because labels within fields need to go away when people are entering their answer into an input field, the context for the answer is gone.