

Inside the Hidden World of Elevator Phone Phreaking. The True “Aboutness” of Blockchain and Why We Are All Crypto Sherpas. Using Phenomenology to explain, not just describe what blockchain really is Most Blockchain explanations are actually descriptions and they are confusing As a Medium reader you will find endless posts explaining Blockchain.
Yuval Noah Harari on Why Technology Favors Tyranny. Editor’s Note: This article is part of a series that attempts to answer the question: Is democracy dying? I. The Growing Fear of Irrelevance There is nothing inevitable about democracy. For all the success that democracies have had over the past century or more, they are blips in history. Monarchies, oligarchies, and other forms of authoritarian rule have been far more common modes of human governance.
The emergence of liberal democracies is associated with ideals of liberty and equality that may seem self-evident and irreversible. In the second decade of the 21st century, liberalism has begun to lose credibility. Information technology is continuing to leap forward; biotechnology is beginning to provide a window into our inner lives—our emotions, thoughts, and choices. The Artificial Intelligence Revolution: Part 2 - Wait But Why. The Artificial Intelligence Revolution: Part 1 - Wait But Why. PDF: We made a fancy PDF of this post for printing and offline viewing.
Buy it here. (Or see a preview.) Note: The reason this post took three weeks to finish is that as I dug into research on Artificial Intelligence, I could not believe what I was reading. It hit me pretty quickly that what’s happening in the world of AI is not just an important topic, but by far THE most important topic for our future. At Scale, Rare Events aren’t Rare – Perspectives. I’m a connoisseur of failure.

I love reading about engineering failures of all forms and, unsurprisingly, I’m particularly interested in data center faults. Linux nslookup command help and examples. Updated: 04/26/2017 by Computer Hope About nslookup The nslookup command is used to query internet name servers interactively for information.

Overview nslookup, which stands for "name server lookup", is a useful tool for finding out information about a named domain. By default, nslookup will translate a domain name to an IP address (or vice versa). Nslookup microsoft.com. IOS Switching Services Configuration Guide, Release 12.2 - Routing Between VLANs Overview [Cisco IOS Software Releases 12.2 Mainline] Routing Between VLANs Overview This chapter provides an overview of VLANs.
![IOS Switching Services Configuration Guide, Release 12.2 - Routing Between VLANs Overview [Cisco IOS Software Releases 12.2 Mainline]](http://cdn.pearltrees.com/s/pic/th/switching-configuration-93730929)
It describes the encapsulation protocols used for routing between VLANs and provides some basic information about designing VLANs. This chapter describes VLANs. It contains the following sections: 12 Extremely Useful Hacks for JavaScript – Hacker Noon. In this post I will share 12 extremely useful hacks for JavaScript. These hacks reduce the code and will help you to run optimized code. So let’s start hacking! And in case you want to be sure your JavaScript works in most browsers and mobile devices, you should probably use Endtest. How to encrypt your entire life in less than an hour. “Only the paranoid survive.” — Andy Grove Andy Grove was a Hungarian refugee who escaped communism, studied engineering, and ultimately led the personal computer revolution as the CEO of Intel.
He died earlier this year in Silicon Valley after a long fight with Parkinson’s disease. When one of the most powerful people in the world encourages us to be paranoid, maybe we should listen. And Grove isn’t the only powerful person urging caution. Even the director of the FBI — the same official who recently paid hackers a million dollars to unlock a shooter’s iPhone — is encouraging everyone to cover their webcams. But you obey the law. Well, law-abiding citizens do have reason to fear. Detailed VPN Comparison Chart. Green = “Generally good”, Yellow = “Something of concern”, Red = “Something major of concern”, Blank = Undefined or for reader’s knowledge only.
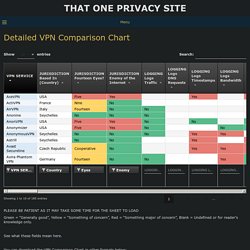
See what these fields mean here. You can download the VPN Comparison Chart in other formats below: Excel – xlsx | LibreOffice – ods | CSV – csv Color blind? How to set up a VPN in 10 minutes for free (and why you urgently need one) Moxie Marlinspike, Next Generation Threats 2014. Oustic cryptanalysis. Summary Many computers emit a high-pitched noise during operation, due to vibration in some of their electronic components.
These acoustic emanations are more than a nuisance: they can convey information about the software running on the computer and, in particular, leak sensitive information about security-related computations. In a preliminary presentation, we have shown that different RSA keys induce different sound patterns, but it was not clear how to extract individual key bits. The main problem was the very low bandwidth of the acoustic side channel (under 20 kHz using common microphones, and a few hundred kHz using ultrasound microphones), many orders of magnitude below the GHz-scale clock rates of the attacked computers. Here, we describe a new acoustic cryptanalysis key extraction attack, applicable to GnuPG's current implementation of RSA. Paper A detailed account of the results and their context is given in the full version of our paper (8MB PDF). Context. All you need is code.