Facebook Top Eleven Manager Guide, Formations and Tactics Guide To Counter Any Opponent Formations. - Nightly
Facebook Top Eleven Manager Guide, Formations and Tactics Guide To Counter Any Opponent Formations by Crizz Gonzalez. This will answer most of your questions if not all about improving your managerial skills. Please also bear in mind that the game engine has been tweaked since this invaluable information was given. This is an attempt at compiling a semi-complete guide that’ll help new players better understand this awesomely addictive game. I hope it answers many of the common questions about formations, tactics, players, improvement and so forth.
Chromium Notes: The story of Iron
Update from 2013: this post was written in 2009. While the statements it made about Chrome were true then, Chrome today is a much different project. Iron claims to be a "privacy-oriented" fork of Chrome, which removes a bunch of pieces that the Iron author claims are privacy invasive. In the abstract this is a thing I'd support -- nothing like some publicity to put pressure on the project to be more careful about user privacy -- but when you look at the details it kinda falls down.
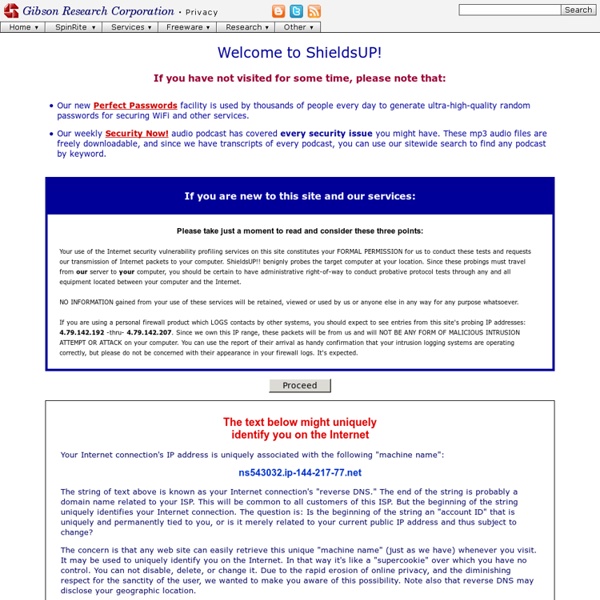
Officially Unofficial ShieldsUP! FAQ
_______________________________________________________________ ShieldsUp! Newsgroup Frequently Asked Questions Written and Compiled by Chris Baker Version 1.14 - 16 April 2000 Please note: If you wish to contact me with errors, omissions, or suggestions regarding this FAQ, feel free to e-mail me at faq-admin@home.com, and I will try to get back to you within 72 hours. However, if you have general questions or technical support issues regarding ShieldsUp!, or anything else for that matter, I regret that I have neither the time nor the resources to assist you directly.
Password Haystacks: How Well Hidden is Your Needle?
... and how well hidden is YOUR needle? Every password you use can be thought of as a needle hiding in a haystack. After all searches of common passwords and dictionaries have failed, an attacker must resort to a “brute force” search – ultimately trying every possible combination of letters, numbers and then symbols until the combination you chose, is discovered.
Raids - Book Of Heroes Wiki - Nightly
About Edit To participate in raids, you need to have enough Might. Squire's Valor raids Gobblin' Goblins in Glenfort Village (required might: 0), aka GG/Gobs
worthless information about your worthless mouse
Your mouse's polling rate determines how often it sends data to your operating system. All mouse movements (counts) and button presses must wait in the mouse until windows polls for them. By default, windows will poll a usb mouse every 8 milliseconds (125hz). You can increase the frequency of polling with a number of programs/drivers/registry fixes. All this does is reduce the delay of sending the mouse data to the operating system.
Technology
Your Security Is Our Priority Availability You need to always have access to your data, we've accomplished this in multiple ways, first we have 2 data-centers in production service, second we store your encrypted data on your local PC when you login, so that if LastPass.com can't be reached, you can still login to the add-on and get to your accounts. The website is usable without the add-on installed (the Encryption and Decryption happens in JavaScript which you can see happen on some forms), but we take advantage of faster encryption available in the add-ons if they're available. We also have a mobile site m.lastpass.com if you're on your phone.
Firewall Leakage Tester
Introducing LeakTest This site has been most well-known for its FREE ShieldsUP! Internet security test.
Live Webcams - Free, public web cams found online
These webcams have been found automatically on the net. For one reason or another these streams are publicly accessible, even when that seems surprising. We do not hack people's passwords. We simply locate cams hiding away in search engines, grab a snapshot, and present them to you here. The snapshots update every few hours.
Android Rice /g/uide
So, if Android is so modular, why do we need to run a special version of it? The answer lies in just how open Android really is. Android allows OEMs (Phone manufacturers like HTC and Samsung) to personalize it to their own taste, and in most situations, these OEMs lock down the experience to what they want it to be like. Because of this, many community developers band together and create special ROMs (usually referring to an entire picture of an operating system that gets saved to a special area called Read-Only Memory, where they get their name from), which are basically custom versions of Google's AOSP code.
Reviews
<div style='text-align:center'>JavaScript is required to use LastPass.<br />Our local encryption/decryption to keep your sensitive data out of our hands depends on it.<br />We do not recommend you attempt to login without Javascript enabled</div> Here is the cream of the crop, the 100 best of 2009...automatically fills in saved log-ins and forms with the click of a button. This handy Web freebie and browser plug-in also syncs your data to any computer that you use regularly.
List of Common TCP/IP port numbers
User Rating: Details Written by Mell Rosandich Email