

Strong Random Password Generator. Welcome to AgileBits. Deseat.me. How to easily delete your online accounts. Spring Financial is a finance company based in Canada.

The company was founded in 2014. Spring Financial is a subsidiary of Canada Drives, which is a leading auto financing company in Canada. The Chief Executive Officer is Michael Galpin. The Director is Cody Green. The Customer Relations Manager is Laura Marchand. Upon loan approval, the funds will go into a secure trust account. Canceling your loan is simple. A directory of direct links to delete your account from web services. Can't find what you're looking for? Help make justdelete.me better. easy. View Exif online, remove Exif online. Remove exif - Exif Remover Software. EXIF REMOVER SECTION!
This tool will help you to remove EXIF data from your photos. File size limit is now 1 MB. Exchangeable image file format (Exif) is a specification for the image file format used by digital cameras. The specification uses the existing JPEG, TIFF Rev. 6.0, and RIFF WAV file formats, with the addition of specific metadata tags. It is not supported in JPEG 2000, PNG, or GIF. The metadata tags defined in the Exif standard cover a broad spectrum: Date and time information. EXIF Remove : Protect your privacy with this free online jpg cleaner. Jeffrey's Exif viewer. ExifTool by Phil Harvey. Read, Write and Edit Meta Information!
Also available --> Utility to fix Nikon NEF images corrupted by Nikon software ExifTool is a platform-independent Perl library plus a command-line application for reading, writing and editing meta information in a wide variety of files. ExifTool supports many different metadata formats including EXIF, GPS, IPTC, XMP, JFIF, GeoTIFF, ICC Profile, Photoshop IRB, FlashPix, AFCP and ID3, as well as the maker notes of many digital cameras by Canon, Casio, DJI, FLIR, FujiFilm, GE, GoPro, HP, JVC/Victor, Kodak, Leaf, Minolta/Konica-Minolta, Motorola, Nikon, Nintendo, Olympus/Epson, Panasonic/Leica, Pentax/Asahi, Phase One, Reconyx, Ricoh, Samsung, Sanyo, Sigma/Foveon and Sony. ExifTool is also available as a stand-alone Windows executable and a MacOS package: (Note that these versions contain the executable only, and do not include the HTML documentation or other files of the full distribution above.)
The stand-alone Windows executable does not require Perl. Tools for Reading and Editing Exif Data of Photographs. Most digital camera record and save EXIF data with every photograph.
Learn about tools that can help you view and edit Exif tags of your photographs. When you capture a photograph with your digital camera, the camera will not only store the current date and time into the image file but even the camera settings. The information that is recorded by the camera into the photograph may include details about the camera model itself, the lens that was used, shutter speed, aperture, focal length and so on. Some modern digital cameras and camera phones are GPS enabled and they can therefore save even the location co-ordinates (latitude and longitude) with the photographs.
Internet Security and Privacy. Clean Your System and Free Disk Space. Mailinator. YOPmail - Disposable Email Address. 10 Minute Mail. ✉ Guerrilla Mail - Disposable Temporary E-Mail Address. Sofort-mail.de - Die kostenlose Wegwerf-eMail-Adresse. Wegwerf-Email von TRASH-MAIL - dem Fake-Email Provider. Create your temporary spambox!
Create a new mailexpire alias - avoid spam... Access Any Website Or Forum Without Registering. Visit any forum or website to find something useful and they will ask you to register.

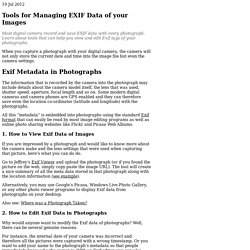
Every time a forum asks me to register, I simply close the site. You would probably do the same. But this time, lets face it. Before I begin, you should know how things work. All websites and forums will block unregistered users, but they won’t block Google Bot. First grab the add-on for Firefox called ‘user agent’ here and install it. Select User Agent from the left sidebar and click Add. Temporary URL - Get your own Expiring URL. Legal Help. Removing Content From Google This page will help you get to the right place to report content that you would like removed from Google's services under applicable laws.
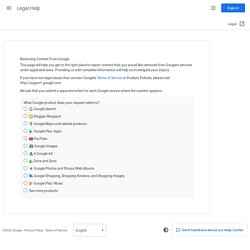
Providing us with complete information will help us investigate your inquiry. If you have non-legal issues that concern Google's Terms of Service or Product Policies, please visit We ask that you submit a separate notice for each Google service where the content appears. What Google product does your request relate to? Hastebin. How to Setup A Hastebin Server. Hastebin is a beautiful simple pastebin used for sharing little pieces of code or information between friends/coworkers.
A friend introduced me to it about a month ago when we were trying to collaborate on a piece of batch script we were working through. After utilizing it for a couple of weeks and realizing its usability, I had the epiphany of hosting my own Hastebin! And a plus is, all collaboration is stored on one of my own machines and not out there in the wild somewhere (it helps me sleep better at night). Enjoy! Steps for installing a Hastebin Server Install all necessary packages Install Node Version Manager to install and maintain Node JS Close Terminal and reopen Install Node JS 0.10.17 (this is the latest version as of this writing double check github.com/creationix/nvm for latest version) and Hasteserver That is it to get you up and running.
Privnote - Send notes that will self-destruct after being read. Pastebin.com - #1 paste tool since 2002! ZeroBin. Pastee. QuickForget.com. Pidgin - secure instant messaging. You may use one of three methods of identification to authenticate your Pidgin buddy; you could use any one of the following options:
Off-the-Record Messaging. OnionShare. Open Whisper Systems >> Home. How to Install & Use a Secure IRC Client with OTR. Welcome back, my amateur hackers!

As many of you know, Null Byte will soon be re-establishing its IRC channel. In preparation of that event, I want to show how to set up a secure IRC client with OTR, or Off the Record. Secure email: ProtonMail is free encrypted email. Tutanota. Yandex.Mail — a free email service. SCRYPTmail.com. 10 Million users Work Online with Zoho. Sourcesûre. SecureDrop. GlobaLeaks. Google Webmaster Tools. Offliberty - evidence of offline life.
Startpage Search Engine. DuckDuckGo. Sandboxie - Sandbox software for application isolation and secure Web browsing. Adblock Plus - Surf the web without annoying ads! The Official EasyList Website. Anonymous-MacPackage-Privacy. Qubes OS Project. Privacy for anyone anywhere.
JonDo Live-CD / DVD. Minds. Diaspora* Why you should stay away from Unseen.is - joepie91's Ramblings. It took a bit longer than I expected before I had the time to make this post, but here it finally is.

Not too long ago, I ran across some Anonymous-related Twitter accounts promoting Unseen.is. Unseen is, in their own words, a "private and secure messaging, calling and e-mail application" - which seems great, but really isn't. As it turns out, there are plenty of reasons why you shouldn't ever use them. The mortal sin of cryptography. Unseen - Unseen.is secure chat, calling, and email. The Freenet Project - /index. A Curated Guide to I2P. A 3 minute read.

Photo By Daniel Rehn Lately, several articles have been published about I2P largely due to the Silk Road moving from Tor. Some of these articles have done a good job in covering I2P, others not so much. It seems that one of the hurdles that authors are having trouble with is understanding the idea that there is more to I2P than simply a drug market. Thus, here’s a list of various I2P services that aren’t drug markets, that may still be of interest. Each link is a b32 address, meaning that you shouldn’t need an address book lookup, and should be able to go directly to the site. I2P Anonymous Network. Tor Browser Portable. 0.1.2. Ipredia.org - Home of IprediaOS. ProxMate - Proxy on steroids! Internet Security and Privacy made simple - ZenMate. Overview and download of the free anonymizer.
FoxyProxy. Total Delivery Solution for the Censored Internet. Tor Project: Anonymity Online. Vtunnel.com is here to help you beat internet filtering! Socks 24. Sorted by anonymity type #1. Free Proxy List - Public Proxy Servers (IP PORT) - Hide My Ass! Anonymous Surfing, Offshore Email, Offshore Hosting, Offshore Dedicated Servers, anonymous vpn. IPredator - VPN. Anonymous Private VPN - High Speed, Unlimited Acccess.
Relakks - Surf anonymously with VPN and proxy. Free VPN Software - Hotspot Shield VPN. The Best VPN Service Provider with Fast, Secure VPN Access. Spotflux Free VPN. Hola - Free VPN - Secure Browsing - Unrestricted Access. Les Réseaux Privés Virtuels - Vpn. 1 – Introduction au réseau privé virtuel VPN Les applications et les systèmes distribués font de plus en plus partie intégrante du paysage d’un grand nombre d’entreprises. Ces technologies ont pu se développer grâce aux performances toujours plus importantes des réseaux locaux. Mais le succès de ces applications a fait aussi apparaître un de leur écueil. En effet si les applications distribuées deviennent le principal outil du système d’information de l’entreprise, comment assurer leur accès sécurisé au sein de structures parfois réparties sur de grandes distances géographiques ?
Concrètement comment une succursale d’une entreprise peut-elle accéder aux données situées sur un serveur de la maison mère distant de plusieurs milliers de kilomètres ? 2 – Principe de fonctionnement du VPN 2.1 – Principe général Un réseau VPN repose sur un protocole appelé « protocole de tunneling ». Les données à transmettre peuvent être prises en charge par un protocole différent d’IP. 2.2.1 – Le VPN d’accès. Le blog du VPN. Onion Pi Pack w/Large Antenna - Make a Raspberry Pi Tor Proxy ID: 1406 - $94.95. Want something more compact? We suggest our compact Onion Pi model, it still has great range, but will take up less space! Feel like someone is snooping on you? Browse anonymously anywhere you go with the Onion Pi Tor proxy. Cyborg Unplug. Safari - Cookies Databases keep coming back aft...
Hi dominic23, Below is the report you have requested. EtreCheck version: 3.1.5 (343) - Boing Boing. (see story here) "The Internet interprets censorship as damage and routes around it. " -- John Gilmore If your employer or corrupt, undemocratic, dictator-based government uses a filtering service such as Secure Computing's SmartFilter to block access to BoingBoing.net -- or anything else online -- you can try the following workarounds: Distributed BoingBoing mirrors everything on BoingBoing.net at random IP addresses to foil filters. Read "Technical Ways to Get Around Censorship," a helpful primer from Reporters Without Borders: Link. Google can act as a lightweight, proxy-like tool for accessing forbidden sites -- but don't rely on this method for anonymity. Or... If you're accessing BoingBoing from work, you may be able to ask your system administrator to whitelist BoingBoing.net.
If you know of any good ways to defeat censorware, please send us your suggestion. Find Out If Your Computer Is Secretly Connecting to the Web. Computrace - Le mouchard universel présent sur les PC, Mac et appareils Android. Et si je vous disais qu'il y a dans votre ordinateur un mouchard que vous ne pouvez pas enlever, qui a été mis en place par le constructeur, qui est sur les listes blanches de la plupart des antivirus et dont vous n'avez jamais entendu parler ?
La société Kaspersky, spécialisée dans la détection et l'élimination de malware a débusqué il y a quelques mois un logiciel installé sur plus de 2 millions d'ordinateurs de par le monde qui est commercialisé par la société Absolute et qui permet OFFICIELLEMENT : Privacy International. Information Security Stack Exchange. EPIC Online Guide to Practical Privacy Tools. Opt out of global data surveillance programs like PRISM, XKeyscore, and Tempora - PRISM Break - PRISM Break.