


Most popular VMWare Virtual Appliances for IT Administrators Updated on September 23, 2009: Please review the updated list of virtual appliances. You may also be interested in reviewing virtual appliances for Security. The original post has been retained as a historical reference. The download links for most of the appliances in the following table no longer work since VMware has revamped the Appliance Marketplace. Thanks Carpe Noctem - Seize the NightCarpe Noctem – Seize the Night LSD was invented in Switzerland by Albert Hofmann, a researcher for Sandoz pharmaceuticals. The CIA was on to acid long before the flower children. It did not spontaneously appear among the youth of the Western world as a gift from the God of Getting’ High.
IT Career Paths - A Guide to Credentials and Certifications If you love technology, then the IT field can offer a number of opportunities and areas to specialize in. As you hone in on your skills, you can validate your knowledge by advancing up the certification ladder to achieve new career heights. Whatever path you choose, we'll help you figure out the right steps to take. The certification guides listed below illustrate the different certification paths from tech companies and organizations in core technical areas including storage, networking and security as well as project management, big data, mobility, and a lot more. From entry-level to architect credentials, each certification guide will walk you through the offerings from the sponsoring organization, whether it's a company, like Microsoft, or a vendor-neutral organization, like CompTIA. We also include information on certification requirements, training options, and advice on which credentials go well with others.
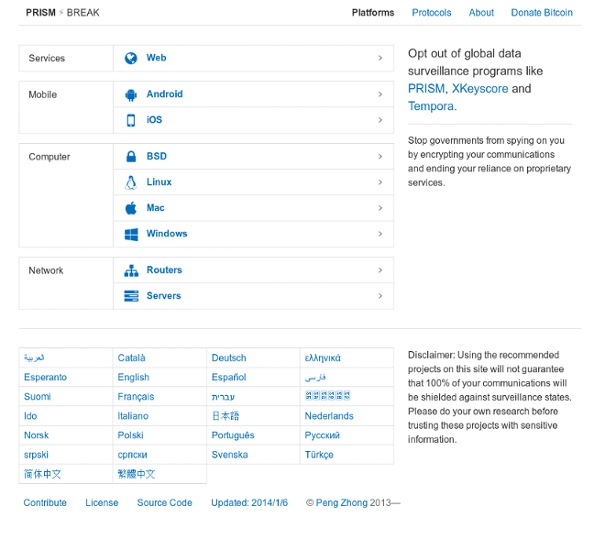
How the NSA's Domestic Spying Program Works The NSA’s domestic spying program, known in official government documents as the “President’s Surveillance Program,” ("The Program") was implemented by President George W. Bush shortly after the attacks on September 11, 2001. The US Government still considers the Program officially classified, but a tremendous amount of information has been exposed by various whistleblowers, admitted to by government officials during Congressional hearings and with public statements, and reported on in investigations by major newspaper across the country. Our NSA Domestic Spying Timeline has a full list of important dates, events, and reports, but we also want to explain—to the extent we understand it—the full scope of the Program and how the government has implemented it.
Best Information Security Certifications for 2016 - Certs - Tom's IT Pro InfoSec professionals who want to set themselves apart as leaders in IT security should seriously consider one of these top five information security certifications for 2016. When it comes to information security, you need only read the headlines to observe that those with malicious intent constantly find new and scary ways to access and misuse privileged information for criminal, unscrupulous or questionable purposes. As a result, IT professionals skilled in information security remain in very high demand and should do so for the foreseeable future. When evaluating prospective InfoSec candidates, employers frequently look to certification as one measure of excellence and commitment to quality. In this article, we take a look at five InfoSec certifications we consider to be leaders in the field of information security today.
Millions of Americans installing 'perfect spying device' in their own living rooms: Amazon Fire TV monitors and records your conversations - NaturalNews.com Tuesday, July 15, 2014by Mike Adams, the Health RangerTags: Amazon Fire TV, audio surveillance, perfect spying device (NaturalNews) Amazon.com is building the CIA's new $600 million data center, reports the Financial Times. (1) At the same time Amazon.com is building this massive cloud computing infrastructure for the CIA, the company is also shipping millions of Fire TV set-top devices to customers who are placing them in their private homes. I have one myself, and it's a terrific piece of hardware for delivering Prime video content. In fact, in terms of its usability and specs, it's far superior to Roku or Netflix-capable devices. Fire TV is, hands down, the best set-top video delivery device on the market today.
EC-Council Certification Guide: Overview and Career Paths - Tom's IT Pro EC-Council offers some of the best-known ethical hacking and penetration testing certifications. This guide will help you get started with EC-Council's popular CEH and LPT credentials as well as other information security certs and career paths. The International Council of Electronic Commerce Consultants (EC-Council) is a professional organization headquartered in Albuquerque, New Mexico.
MIT Updates Wi-Fi Tech That Can Track You Through Walls Kevin SamsonActivist Post One of the hallmarks of technology is dual-use capability. It is for this reason that we are softened up with all of the benefits, before being introduced to the darker side. Technology has always been a double-edged sword, but we are witnessing a closure in the gap between good and bad as technology is now advancing at a much higher rate of speed in tandem with a growing global police state. A few months ago, I remember seeing a story about how a new microwave device could see through rubble to detect the beating heart of people trapped under a collapsed building. I immediately thought, wow that's a good thing ... ohhhh, wait a minute.
Creepy, the Geolocation Information Aggregator What is Creepy ? So what is Creepy actually and how does it come into the “Geolocation” picture ? Creepy is a geolocation information aggregation tool. It allows users to gather already published and made publicly available geolocation information from a number of social networking platforms and image hosting services. In its current, beta form, it caters to harvesting geolocation information from twitter in the form of geotagged tweets, foursquare check-in’s, geotagged photos posted on twitter via image hosting services such as yfrog, twitpic, img.ly, plixi and others, and Flickr. The geolocation information that Creepy retrieves is presented to the user in the form of points on a navigable embedded map along with a list of locations (geographic latitude and longitude accompanied with the date and time).
U.S. Postal Service Logging All Mail for Law Enforcement Photo WASHINGTON — Leslie James Pickering noticed something odd in his mail last September: a handwritten card, apparently delivered by mistake, with instructions for postal workers to pay special attention to the letters and packages sent to his home. “Show all mail to supv” — supervisor — “for copying prior to going out on the street,” read the card.
Adversary Resistant Computing Platform: SubgraphOS Subgraph OS is an adversary resistant computing platform. The main purpose of Subgraph OS is to empower people to communicate, share, and collaborate without fear of surveillance and interference. What this means in practical terms is that users of Subgraph OS can safely perform their day-to-day tasks securely and privately. In some ways, Subgraph OS is like other operating systems — it is derived from Debian GNU/Linux and uses the GNOME desktop environment as its graphical user interface. Many applications found in other Linux distributions are also available in Subgraph OS. Therefore, users who are already familiar to Linux and particularly the GNOME desktop environment will find Subgraph OS easy to use.
FBI Can Turn On Your Webcam Without You Knowing It The FBI apparently has the ability to take over your computer’s webcam and your smartphone’s camera and use them to spy on you, according to recent reports. To make matters worse, you probably wouldn’t realize that you are under surveillance via your own devices, because the agency also can watch without your webcam light even turning on. The FBI has had the ability to take over webcams, microphones and camera phones for several years, The Washington Post discovered. The Post’s reporters stumbled upon the bureau’s capabilities when they were working on a story about the bureau’s search for a man in Iran who was making threats against Americans.
Rogue Wi-Fi Access Point: 3vilTwinAttacker CyberPunk » Information Gathering This tool create an rogue Wi-Fi access point , purporting to provide wireless Internet services, but snooping on the traffic 3vilTwinAttacker is security tool that provide the Rogue access point to Man-In-The-Middle and network attacks. purporting to provide wireless Internet services, but snooping on the traffic. can be used to capture of credentials of unsuspecting users by either snooping the communication by phishing. Dependencies: