

You are committing a crime right now. Are you reading this blog?
Reporters threatened with CFAA, labeled hackers for finding security hole. Scripps News reporters discovered 170,000 Lifeline phone customer records online that contained everything needed for identity theft.

After requesting an interview with the COO of TerraCom and YourTel, the reaction was kill-the-messenger style; the reporters were called "Scripps Hackers" and threatened with violating the Computer Fraud and Abuse Act. Scripps News was looking into Lifeline , a government program offering affordable phone service for low-income citizens. Comcast Punishes BitTorrent Pirates With Browser Hijack. Comcast revealed today how it will deal with customers who receive multiple warnings under the newly launched "six-strikes" anti-piracy system.
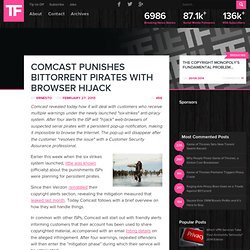
Government Removal Requests – Google Transparency Report. Like other technology and communications companies, Google regularly receives requests from government agencies and courts around the world to remove content from our services or to review such content to determine if it should be removed for inconsistency with a product's community policies.
In this report, we disclose the number of requests we receive from each government in six-month periods with certain limitations. Governments ask companies to remove or review content for many different reasons. For example, some content removals are requested due to allegations of defamation, while others are due to allegations that the content violates local laws prohibiting hate speech or adult content. Laws surrounding these issues vary by country, and the requests reflect the legal context of a given jurisdiction. We hope this tool will be helpful in discussions about the appropriate scope and authority of government requests. By Reporting Period All Requests Court Orders Executive, Police, etc. Syria – Traffic Graph – Google Transparency Report. People have been unable to access certain Google products and services at some point in more than 30 countries.

Causes for these disruptions vary, and include network outages and government-mandated blocks. Review current disruptions below or browse all documented disruptions. Open internet.
CISPA / TPP / ACTA / SOPA / PIPA / COICA. ‘The Pirate Bay Dancing’ Add-On Killls DNS and IP Blockades. Efforts to censor the Internet are increasing in the Western world.
In the US lawmakers are currently discussing legislation (SOPA/PIPA) that could take out The Pirate Bay, or disable access to it. Internet bill could help hackers, experts warn. White Paper Warns Against DNS Filtering Requirements in PROTECT IP Act. Steve Crocker, David Dagon, Dan Kaminsky, Danny McPherson, and Paul Vixie have authored a white paper warning that the DNS filtering requirements of the PROTECT IP Act would be ineffective in reducing piracy, but would harm the security of the internet. “DNS filtering will be evaded through trivial and often automated changes through easily accessible and installed software plugins” such as MafiaaFire.
The likely circumvention techniques “will expose users to new potential security threats. These security risks will not be limited to individuals. Banks, credit card issuers, health care providers, and others who have particular interests in security protections for data also will be affected. At the same time, a migration away from U.S. Security and Other Technical Concerns Raised by the DNS Filtering Requirements in the PROTECT IP Bill The authors of this paper take no issue with strong enforcement of intellectual property rights generally. 10 things to look for in a circumvention tool. As more countries crack down on Internet use, people around the world are turning to anti-censorship software that lets them reach blocked websites.

Many types of software, also known as circumvention tools, have been created to answer the threat to freedom online. These tools provide different features and levels of security, and it's important for users to understand the tradeoffs. This article lays out ten features you should consider when evaluating a circumvention tool. The goal isn't to advocate for any specific tool, but to point out what kind of tools are useful for different situations. I've chosen the order of features based on ease of presentation; so you shouldn't conclude the first feature is the most critical. Internet-based circumvention software consists of two components: a relaying component and a discovery component. Some tools have a simple relaying component.
Net neutrality. Busting Egypt's web blackout. An Egyptian protester flashes Egypt's flag as anti-riot policemen use water canon against protesters in Cairo on Jan. 28, 2011.
Such resilience on the part of protesters has enabled them to find creative ways to circumvent the internet blackout the government imposed Friday. ((Lefteris Pitarakis/Associated Press)) The Egyptian government ordered a digital crackdown Friday in an effort to quell protesters, shutting down internet access and cellphone services, but some Egyptians are still finding ways to connect with others. "This is certainly not unprecedented in type, but it is unique in scope and size," said Ron Deibert, director of the Canada Centre for Global Security Studies and the Citizen Lab at the University of Toronto. Many countries monitor and filter their citizens' communications and online activities. Group plans to beam free Internet across the globe from space. By Eric W.

DolanThursday, February 10, 2011 14:32 EDT The charity group A Human Right said it was planning to purchase a satellite that would provide free basic Internet access to developing countries around the world.