

NSA's Top Brazilian Political and Financial Targets Revealed by New WikiLeaks Disclosure. Top secret data from the National Security Agency, shared with The Intercept by WikiLeaks, reveals that the U.S. spy agency targeted the cellphones and other communications devices of more than a dozen top Brazilian political and financial officials, including the country’s president Dilma Rousseff, whose presidential plane’s telephone was on the list.

President Rousseff just yesterday returned to Brazil after a trip to the U.S. that included a meeting with President Obama, a visit she had delayed for almost two years in anger over prior revelations of NSA spying on Brazil. That Rousseff’s personal cell phone was successfully targeted by NSA spying was previously reported in 2013 by Fantastico, a program on the Brazilian television network Globo Rede. But these new revelations extend far beyond the prior ones and are likely to reinvigorate tensions. Espionnage Élysée. (on 2015-06-29) English | French Today, 29 June 2015, WikiLeaks continued "Espionnage Élysée", our ongoing publication of a collection of TOP SECRET documents from United States surveillance operations against France.
Today's publication comprises seven top secret documents detailing how the US has had a decade- long policy of economic espionage against France, including the interception of all French corporate contracts and negotiations valued at more than $200 million. WikiLeaks Docs Show NSA Penetrated Highest Levels of French Government. How’s this for irony?

In 2010, the National Security Agency intercepted communications between two senior French officials complaining about the United States’ unwillingness to stop spying on France. That tidbit is among the latest revelations provided by WikiLeaks, which on Tuesday published a small selection of documents about American snooping on top-level French officials. The NSA is preparing to turn off mass surveillance programs. How the NSA Converts Spoken Words Into Searchable Text. First in a series.
Part 2 here. Part 3 here. Most people realize that emails and other digital communications they once considered private can now become part of their permanent record. But even as they increasingly use apps that understand what they say, most people don’t realize that the words they speak are not so private anymore, either. New Zealand Spied on WTO Director Candidates. New Zealand launched a covert surveillance operation targeting candidates vying to be director general of the World Trade Organization, a top-secret document reveals.

In the period leading up to the May 2013 appointment, the country’s electronic eavesdropping agency programmed an Internet spying system to intercept emails about a list of high-profile candidates from Brazil, Costa Rica, Ghana, Indonesia, Jordan, Kenya, Mexico and South Korea. New Zealand’s trade minister, Tim Groser, was one of nine candidates in contention for the position at the WTO, a powerful international organization based in Geneva, Switzerland that negotiates trade agreements between nations.
The surveillance operation, carried out by Government Communications Security Bureau, or GCSB, appears to have been part of a secret effort to help Groser win the job. NSA Braced for New Leaks. National Security Agency / AP BY: Bill Gertz The National Security Agency, still reeling from massive leaks caused by Edward Snowden, is preparing to be hit with another major loss of secrets, according to U.S. intelligence officials.
The leaks are expected to be published in the near future by a news outlet that was not further identified by the officials familiar with details of the compromise. Prying Eyes: Inside the NSA's War on Internet Security. When Christmas approaches, the spies of the Five Eyes intelligence services can look forward to a break from the arduous daily work of spying.
In addition to their usual job -- attempting to crack encryption all around the world -- they play a game called the "Kryptos Kristmas Kwiz," which involves solving challenging numerical and alphabetical puzzles. The proud winners of the competition are awarded "Kryptos" mugs. Encryption -- the use of mathematics to protect communications from spying -- is used for electronic transactions of all types, by governments, firms and private users alike.
But a look into the archive of whistleblower Edward Snowden shows that not all encryption technologies live up to what they promise. Operation AURORAGOLD: How the NSA Hacks Cellphone Networks Worldwide. In March 2011, two weeks before the Western intervention in Libya, a secret message was delivered to the National Security Agency.
An intelligence unit within the U.S. military’s Africa Command needed help to hack into Libya’s cellphone networks and monitor text messages. Core Secrets: NSA Saboteurs in China and Germany. The National Security Agency has had agents in China, Germany, and South Korea working on programs that use “physical subversion” to infiltrate and compromise networks and devices, according to documents obtained by The Intercept.
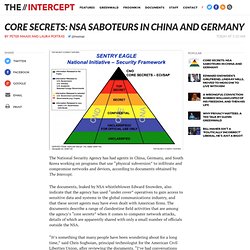
The documents, leaked by NSA whistleblower Edward Snowden, also indicate that the agency has used “under cover” operatives to gain access to sensitive data and systems in the global communications industry, and that these secret agents may have even dealt with American firms. The documents describe a range of clandestine field activities that are among the agency’s “core secrets” when it comes to computer network attacks, details of which are apparently shared with only a small number of officials outside the NSA. “It’s something that many people have been wondering about for a long time,” said Chris Soghoian, principal technologist for the American Civil Liberties Union, after reviewing the documents. Sentry Eagle “Under Cover” Agents Corporate Partners.
Israel’s N.S.A. Scandal - NYTimes.com. Photo WASHINGTON — IN Moscow this summer, while reporting a story for Wired magazine, I had the rare opportunity to hang out for three days with Edward J.

Snowden. Open Secret About Google’s Surveillance Case No Longer Secret - Digits. 20130813_letter_to_vp_reding_final_en.pdf. NSA report on the Tor encrypted network. The following document is a 2006 research paper produced for the NSA's "Cryptanalysis and Exploitation Services" office. It lays out the technical features of Tor and proposes a number of theoretical and practical attacks, some of which the NSA developed and used in subsequent years. Among other things, the paper describes an NSA-written adaptation of Tor, "indistinguishable from an original Tor client," which enables the NSA to gather intelligence inside the network. It also describes two kinds of "denial of service" attacks against Tor, code-named Coil and Flower, which are used to divert would-be anonymous communications into open channels.
By cracking cellphone code, NSA has capacity for decoding private conversations. U.S. law prohibits the NSA from collecting the content of conversations between Americans without a court order. But experts say that if the NSA has developed the capacity to easily decode encrypted cellphone conversations, then other nations likely can do the same through their own intelligence services, potentially to Americans’ calls, as well. Encryption experts have complained for years that the most commonly used technology, known as A5/1, is vulnerable and have urged providers to upgrade to newer systems that are much harder to crack.
Most companies worldwide have not done so, even as controversy has intensified in recent months over NSA collection of cellphone traffic, including of such world leaders as German Chancellor Angela Merkel. Nokia smartphone leaks information abroad. Details Parent Category: Finland Category: Domestic 24 Feb 2014 Two years ago, trust in the data security of Nokia smartphones was still strong. On Monday, 5 March 2012, a meeting was organised at the Nokia headquarters in which Nokia advertised the data security of its smartphones to authorities deciding on government IT procurements. Soon after the event, large amounts of Nokia’s Lumia phones were bought for the Finnish government: ministers, MPs and authorities. Nokia smartphone leaks information abroad.
A Close Look at the NSA's Most Powerful Internet Attack Tool. Photo: Trevor Paglen We already knew that the NSA has weaponized the internet, enabling it to “shoot” exploits at anyone it desires. A single web fetch, imitated by an identified target, is sufficient for the NSA to exploit its victim. But the Edward Snowden slides and story published yesterday at The Intercept convey a wealth of new detailed information about the NSA’s technology and its limitations. First, it’s clear that the NSA has settled on a system called QUANTUM as its preferred, if not near-universal, internet exploitation mechanism.
QUANTUM is vastly more effective than just sending spam. If NSA only used QUANTUM to attack wannabee terrorists attempting to read Inspire, hardly anyone would object. Nicholas Weaver is a researcher at the International Computer Science Institute and UC Berkeley (though this opinion is his own). GCHQ and NSA Targeted Private German Companies. The headquarters of Stellar, a company based in the town of Hürth near Cologne, are visible from a distance. Seventy-five white antennas dominate the landscape. The biggest are 16 meters (52 feet) tall and kept in place by steel anchors. It is an impressive sight and serves as a popular backdrop for scenes in TV shows, including the German action series "Cobra 11.
" Stellar operates a satellite ground station in Hürth, a so-called "teleport. " The NSA Uses Powerful Toolbox in Effort to Spy on Global Networks. In January 2010, numerous homeowners in San Antonio, Texas, stood baffled in front of their closed garage doors. N.S.A. Devises Radio Pathway Into Computers. NSA collects millions of text messages daily in 'untargeted' global sweep. The National Security Agency has collected almost 200 million text messages a day from across the globe, using them to extract data including location, contact networks and credit card details, according to top-secret documents. NSA 'engaged in industrial espionage' - Snowden. 26 January 2014Last updated at 18:16 ET. Bruce Schneier: 'NSA and GCHQ have betrayed the trust of the internet' The NSA's Secret Role in the U.S. Assassination Program. Credit: Kirsty Wigglesworth/Associated Press.
The National Security Agency is using complex analysis of electronic surveillance, rather than human intelligence, as the primary method to locate targets for lethal drone strikes – an unreliable tactic that results in the deaths of innocent or unidentified people. US and UK struck secret deal to allow NSA to 'unmask' Britons' personal data. The phone, internet and email records of UK citizens not suspected of any wrongdoing have been analysed and stored by America's National Security Agency under a secret deal that was approved by British intelligence officials, according to documents from the whistleblower Edward Snowden.
Blair 'opened our doors to US spies' Preventing The Next Snowden: NSA To 'Continuously Evaluate' Contractors As Potential Threats. According to the Federation of American Scientists’ Secrecy News blog, the House committee made its proposal in a Monday report on the FY 2014 intelligence authorization bill, arguing that constant background checks of NSA contractors would have prevented this summer’s leaks by Edward Snowden. The HPSCI would require all agencies such as the NSA, FBI and CIA to “continuously determine whether their employees and contractors are eligible for access to classified information” by scanning transactions, social media and other lawfully-obtained information. NSA tracking cellphone locations worldwide, Snowden documents show.
How the NSA is tracking people right now. Snowden files reveal Swedish-American surveillance of Russia - Uppdrag Granskning. Uppdrag granskning (Mission Investigation) and SVT is the first Swedish news outlet to get access to documents concerning Sweden leaked by whistleblower Edward Snowden, who left the American organization for surveillance, NSA (National Security Agency) in May this year. Snowden leaks: France summons US envoy over NSA surveillance claims. Tales from the Crypto Community. NSA surveillance: Germany to send intelligence officials to US. How the NSA's MUSCULAR program collects too much data from Yahoo and Google.
'Let Me Stress How Shocking These NSA Revelations Are': A View From Inside the Defense World - James Fallows. U.S. Is Losing Advantage in Spying, Report Says. Skype under investigation in Luxembourg over link to NSA. New York Times's Jill Abramson: 'The First Amendment is first for a reason' Documents reveal NSA’s extensive involvement in targeted killing program. A psychological history of the NSA. NSA Hacked Email Account of Mexican President. France in the NSA's crosshair : phone networks under surveillance. N.S.A. Gathers Data on Social Connections of U.S. Citizens. Documents on N.S.A. Efforts to Diagram Social Networks of U.S. Citizens - Document. NSA director admits to misleading public on terror plots. NSA Collected US Cellphone Locations In 2010 And 2011. In Test Project, N.S.A. Tracked Cellphone Locations. Tor anonymizer network among NSA’s targets, Snowden leaks reveal. NSA surveillance goes beyond Orwell's imagination – Alan Rusbridger. Oracle Announces It'll Use NSA Hand-Me-Down Tech.
How the NSA cheated cryptography. The NSA Doesn't Deny Having Collected Our Phone Location Data - Philip Bump. NSA surveillance: agency wants to collect all Americans' phone records – live. Shutting Down The US Government Likely Won’t Slow The NSA’s Surveillance Activities. NSA shares raw intelligence including Americans' data with Israel. NSA Allegedly Spies On International Credit Card Transactions. RSA Tells Its Developer Customers: Stop Using NSA-Linked Algorithm. How the NSA Spies on International Bank Transactions. Edward Snowden has started a global debate. So why the silence in Britain? Booting Up: New NSA Data Farm Takes Root In Utah : All Tech Considered.
Project Bullrun – classification guide to the NSA's decryption program. US and UK spy agencies defeat privacy and security on the internet. The NSA's Secret Campaign to Crack, Undermine Internet Encryption. Cyberspying: Government may ban Gmail for official communication. Obama administration had restrictions on NSA reversed in 2011. US should re-evaluate surveillance laws, ex-NSA chief acknowledges. NSA row: Merkel rival threatens to suspend EU-US trade talks. U.S. intelligence agencies spend millions to hunt for insider threats, document shows. The NSA Wants To Ban Sales Of This T-Shirt On Zazzle.
Microsoft pledges to move forward with NSA surveillance lawsuit. Top-secret U.S. intelligence files show new levels of distrust of Pakistan. Spy Kids - By Charles Stross. New Snowden Leak Reports 'Groundbreaking' NSA Crypto-Cracking. America’s secret intelligence budget, in 11 charts. Spy agencies have fewer than 2,000 people proficient in Middle Eastern languages.
NSA Spied on Al Jazeera Communications: Snowden Document. XKeyscore: NSA tool collects 'nearly everything a user does on the internet' German Intelligence Sends Massive Amounts of Data to the NSA. Snowden. In 4 Easy Steps - By Daveed Gartenstein-Ross and Kelsey D. Atherton. The FISA Court Knew the NSA Lied Repeatedly About Its Spying, Approved Its Searches Anyway. NSA and GCHQ: the flawed psychology of government mass surveillance. Why Nobody Cares About the Surveillance State - By David Rieff. ‘I’d tap that!’: NSA Pick Up Lines campaign creates Twitter storm. The Shadow Factory. Welcome to the National Security Agency - NSA/CSS.
U.S. National Security Agency News. The Criminal N.S.A. World news. L'augmentation des "contractors" dans le renseignement américain.