

Www.realtimerendering.com/resources/GraphicsGems/gemsiv/clahe.c. Winhelp2002.mvps.org/hosts.txt. Blocking Unwanted Connections with a Hosts File. What it does ...

You can use a modified HOSTS file to block ads, banners, 3rd party Cookies, 3rd party page counters, web bugs, and even most hijackers and possibly unwanted programs. This is accomplished by blocking the connection(s) that supplies these little gems. The Hosts file is loaded into memory (cache) at startup, so there is no need to turn on, adjust or change any settings with the exception of the DNS Client service (see below). Kyle Scarmardo - Motivation Matters. Kyle Scarmardo talks with Dave Rael about being deliberate with your time, the importance of self-awareness, coaching and mentoring, and taking action Kyle spent sixteen years in the Information Technology space for a large financial company, the 20th largest private company in America, where he worked his way up from the bottom to become an executive in 13 years at the age of 35.
The latter part of his career heavily involved helping others with self-improvement, career growth, improving executive function, applying new strategies to better communicate and influence, and assist with culture change. In this work Kyle tapped into a passion that ultimately would pull him away from a full time focus on technology. Kyle now spends more time assisting others looking to accelerate their careers, become more effective leaders, and take self-improvement to a deeper introspective level.
Agile. SE-Radio Episode 307: Harsh Sinha on Product Management Bryan Reinero talks with Harsh Sinha, VP of Engineering at TransferWise, about Product Management.
Product Management deals with the planning, delivery and marketing of a software product. The discussion covers how those functions are achieved, and how product management interfaces with engineering; how product requirements are derived from customer needs; how teams build product based […] Continue Reading » Your Personal PLC Tutor Site - RS232 Communications/software. Learn quickly with our PLC Training DVD Series: on sale $599.00 $379 Click here now for details!
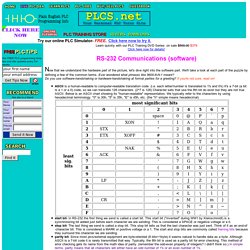
RS-232 Communications (software) Audit and document Security User Rights Assignment using C# For more information on the Windows Server documentation abilities of XIA Configuration please see the following We've recently been asked about the auditing of User Rights Assignment as seen in the Local Group Policy Editor.
Having looked into this issue it is apparent that this cannot be done with any high level API such as WMI and requires the use of P/Invoke and the Win32 method LsaEnumerateAccountsWithUserRight. I've seen many posts on the Internet on the topic but I haven't seen a simplified example of this in use so have writen a quick C# sample application to enumerate the various rights and privileges and display the users assigned to that right in a grouped listview as per the screenshot below. This can be downloaded from our web site in Visual Studio 2010 The sample supports the following. C# - Best Practices of fault toleration and reliability for scheduled tasks or services. Building Scalable, Highly Concurrent & Fault Tolerant Systems - Less… Fault Tolerance Made Easy. Unity 3 – April 2013. Patterns & practices Developer Center April 2013 Unity is a lightweight, extensible dependency injection container with support for instance and type interception.
Overview Unity is a lightweight, extensible dependency injection container with support for constructor, property, and method call injection. It facilitates building loosely coupled applications and provides developers with the following advantages: Simplified object creation, especially for hierarchical object structures and dependencies. Unity is a general-purpose container for use in any type of Microsoft.NET Framework-based application. In addition, Unity is extensible. This release adds support for Windows Store apps as well as the registration by convention feature to ease the task of configuring Unity. Audience Requirements These reusable components and guidance are intended primarily for software developers and software architects. Contents of This Release Microsoft Unity 3 contains the following: Binaries. Design Goals. Ten Common Database Design Mistakes.
No list of mistakes is ever going to be exhaustive.
People (myself included) do a lot of really stupid things, at times, in the name of “getting it done.” This list simply reflects the database design mistakes that are currently on my mind, or in some cases, constantly on my mind. Five simple database design tips. A flawed database can affect all areas of your application, so getting the design right is of paramount importance.

Check out Builder's five simple design tips, and share some of your own. If an enterprise’s data is its lifeblood, then the database design can be the most important part of an application. Volumes have been written on this topic, and entire college degrees have been built around it. However, as has been said time and time again here on Builder.com, there’s no teacher like experience. I’ll get the show started by listing my five favorite tips and giving a brief explanation of the rationale behind each one. Visual C# : The Coders Lexicon. Martyr2's Mega Project Ideas List! - Share Your Project. Learn. Codecademy Labs.
Shaping up with Angular.js - Shaping up with Angular.js. AngularJS — Superheroic JavaScript MVW Framework. Bootstrap.