Telecommunications data retention
In the field of telecommunications, data retention (or data preservation) generally refers to the storage of call detail records (CDRs) of telephony and internet traffic and transaction data (IPDRs) by governments and commercial organisations. In the case of government data retention, the data that is stored is usually of telephone calls made and received, emails sent and received and web sites visited. Location data is also collected.
LemonLDAP - Wiki - Main - WebHome
Introduction Lemonldap::NG provide SSO to Web based applications. The main program is an Apache Handler, acting like a reverse proxy for protected applications. LemonLDAP::NG is the new version of Lemonldap (founded by Eric German) which is no more maintened. The project leaderis Xavier Guimard. It comes from a french administration project, managed by the MINEFI and the Gendarmerie Nationale.
Authorization Roles in CRM Web Channel (SAP Library - SAP CRM: Business Scenario and Business Process Configuration)
Use You assign authorization roles to your users in CRM Web Channel to determine which applications they can enter and the tasks they can carry out in these applications. There are two types of authorization roles provided by SAP: ● For service users There is a service user role for each Web-based application to provide an anonymous stateless RFC connection between the Web-based application and the backend SAP CRM system. ● For Internet users
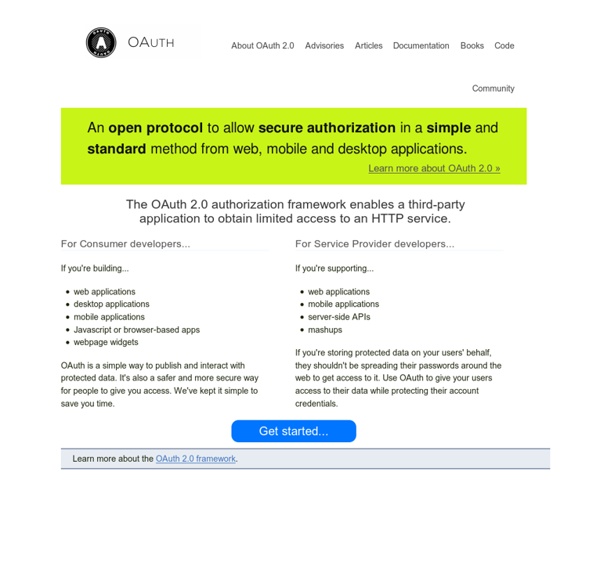
2.0 — OAuth
OAuth 2.0 is the industry-standard protocol for authorization. OAuth 2.0 supersedes the work done on the original OAuth protocol created in 2006. OAuth 2.0 focuses on client developer simplicity while providing specific authorization flows for web applications, desktop applications, mobile phones, and living room devices. This specification and its extensions are being developed within the IETF OAuth Working Group. Questions, suggestions and protocol changes should be discussed on the mailing list.
European Data Protection Authorities Publish Guidelines Clarifying Exemptions to Cookie Consent Requirement : Privacy Law Blog
Home > Data Privacy Laws > European Data Protection Authorities Publish Guidelines Clarifying Exemptions to Cookie Consent Requirement On June 7, 2012, the Article 29 Working Party, an independent advisory body composed of representatives from the national data protection authorities of the EU Member States, the European Data Protection Supervisor and the European Commission, issued Opinion 04/2012 regarding which types of cookies are exempted from the informed user-consent requirement under Directive 2002/58 of the European Parliament (the E-Privacy Directive). Article 5.3 of the E-Privacy Directive requires that websites must obtain informed consent from users prior to storing cookies on users’ equipment. With regard to the first exemption, the Opinion stresses its narrow scope: the words “sole purpose” mean that such cookies will be exempted only if they are strictly necessary for communication to take place over a network between two parties.
Bastion » A blog about J2EE Security, WebLogic, authentication, authorization, auditing, and PKI
According to the Java Servlet Specification, there are four standard methods of authentication in web applications: FORM, BASIC, DIGEST, and CLIENT-CERT. FORM is quite common, but BASIC and DIGEST are not. CLIENT-CERT is primarily used for client certificate authentication but it has more to offer than you might imagine from the name.
OAuth
For MediaWiki's (the software used by Wikipedia) OAuth support, see mw:Help:OAuth OAuth is an open standard for authorization, commonly used as a way for Internet users to log into third party websites using their Microsoft, Google, Facebook or Twitter accounts without exposing their password.[1] Generally, OAuth provides to clients a 'secure delegated access' to server resources on behalf of a resource owner. It specifies a process for resource owners to authorize third-party access to their server resources without sharing their credentials.
How Apple and Amazon Security Flaws Led to My Epic Hacking
In the space of one hour, my entire digital life was destroyed. First my Google account was taken over, then deleted. Next my Twitter account was compromised, and used as a platform to broadcast racist and homophobic messages. And worst of all, my AppleID account was broken into, and my hackers used it to remotely erase all of the data on my iPhone, iPad, and MacBook.
Authentication and Authorization
Authentication is any process by which you verify that someone is who they claim they are. Authorization is any process by which someone is allowed to be where they want to go, or to have information that they want to have. For general access control, see the Access Control How-To.
GitHub API
OAuth2 is a protocol that lets external applications request authorization to private details in a user's GitHub account without getting their password. This is preferred over Basic Authentication because tokens can be limited to specific types of data, and can be revoked by users at any time. All developers need to register their application before getting started. A registered OAuth application is assigned a unique Client ID and Client Secret. The Client Secret should not be shared.