

Storing Passwords - done right! Written by: Christoph Wille Translated by: Bernhard Spuida First published: 1/5/2004 Viewed 257725 times. 1766 ratings, avg. grade 4.76 In very many - not to say almost all - Web applications user data is administered, from Web forum to Web shop.
These user data encompass login information of the users which contain the password besides the user name - and this in plain text. A security leak par excellence. Why is storing the user name and password in plain text a security leak? Well, imagine a cracker gaining system access through eventual OS or server software errors, and being able to read the user database. How can this security risk be eliminated? Open Source Password Manager & File Storage. How Secure is Your Password? One-Time-Passwords. Strong Two Factor Authentication Enhances Your Security Process and Protects Against Unauthorized Access DynaPass is a one-time password solution that is easy to use, easy to implement, and easy to manage.

How to Devise Passwords That Drive Hackers Away. Within weeks, I set up unique, complex passwords for every Web site, enabled two-step authentication for my e-mail accounts, and even covered up my computer’s Web camera with a piece of masking tape — a precaution that invited ridicule from friends and co-workers who suggested it was time to get my head checked.

But recent episodes offered vindication. I removed the webcam tape — after a friend convinced me that it was a little much — only to see its light turn green a few days later, suggesting someone was in my computer and watching. More recently, I received a text message from Google with the two-step verification code for my Gmail account. That’s the string of numbers Google sends after you correctly enter the password to your Gmail account, and it serves as a second password.
(Do sign up for it.) It is absurdly easy to get hacked. Chances are, most people will get hacked at some point in their lifetime. OR JUST JAM ON YOUR KEYBOARD For sensitive accounts, Mr. Passphrases That You Can Memorize — But That Even the NSA Can't Guess. It’s getting easier to secure your digital privacy. iPhones now encrypt a great deal of personal information; hard drives on Mac and Windows 8.1 computers are now automatically locked down; even Facebook, which made a fortune on open sharing, is providing end-to-end encryption in the chat tool WhatsApp.

But none of this technology offers as much protection as you may think if you don’t know how to come up with a good passphrase. A passphrase is like a password, but longer and more secure. In essence, it’s an encryption key that you memorize. Once you start caring more deeply about your privacy and improving your computer security habits, one of the first roadblocks you’ll run into is having to create a passphrase. The Tragic Password Mistake Hackers Are Hoping You'll Make. Photo Credit: Zsolt Biczo/Shutterstock You’re smart.

You don’t use passwords like the perennial 123456 and qwerty. Or even slightly better ones, like Cassie86 or Cubs1908. Because you put some thought into them, your passwords are better than those, right? Shop ▾ How Your Passwords Are Stored on the Internet (and When Your Password Strength Doesn't Matter) One Simple Thing You Should Do Right Now to Keep Hackers From Destroying Your Digital Life. I got a couple emails about setting this up with your iphone email client, which is a little tricky.

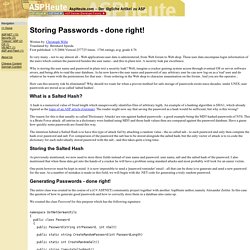
But here's how. (Also works with desktop mail clients, and if you want your gchat to work through a third-party chat client.) After setting up 2-step authentication go to your account page and do this: List of Rainbow Tables. This page lists the rainbow tables we generated.
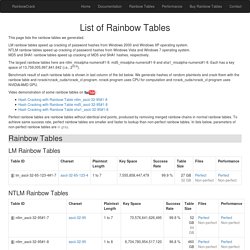
LM rainbow tables speed up cracking of password hashes from Windows 2000 and Windows XP operating system. NTLM rainbow tables speed up cracking of password hashes from Windows Vista and Windows 7 operating system. MD5 and SHA1 rainbow tables speed up cracking of MD5 and SHA1 hashes, respectively. RANDOM.ORG - Password Generator. <p style="background-color:#ffff90;padding: 0em .5em 0em .5em;font-size:.9em"><strong>Warning:</strong> Your browser does not support JavaScript – RANDOM.ORG may not work as expected</p> Do you own an iOS or Android device?
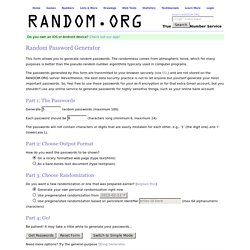
Check out our app! This form allows you to generate random passwords. The randomness comes from atmospheric noise, which for many purposes is better than the pseudo-random number algorithms typically used in computer programs. The passwords generated by this form are transmitted to your browser securely (via SSL) and are not stored on the RANDOM.ORG server. How I Cracked your Windows Password (Part 1) AdvertisementGFI LanGuard your virtual security consultant.

Scan your LAN for any vulnerability and automate patch management for Windows, Mac OS & Linux. Massive collection of password wordlists to recover your lost password. LastPass.