


7 Free Windows Password Recovery Tools (August 2016) Trinity Rescue Kit needs to be booted from a disc or USB stick to work. It includes many different tools, one of which is for password recovery. You can use Trinity Rescue Kit to clear a password entirely, making it blank, or to set a custom one. Some of you may find this program difficult to use because there isn't a graphical interface. However, even if you're not used to a command line interface, most of the required keystrokes are just numbers for choosing different options for resetting a password. Trinity Rescue Kit should work with Windows 10, 8, 7, Vista, and XP. Trinity Rescue Kit v3.4 Free Download Note: The password resetting tool in Trinity Rescue Kit, called winpass, is actually just an automated script for the chntpw tool, which is what Offline NT Password & Registry Editor, listed above, is based on.
Windows BitLocker Drive Encryption Step-by-Step Guide What is BitLocker Drive Encryption? BitLocker Drive Encryption is an integral new security feature in the Windows Vista operating system that provides considerable protection for the operating system on your computer and data stored on the operating system volume. BitLocker ensures that data stored on a computer running Windows Vista remains encrypted even if the computer is tampered with when the operating system is not running. BitLocker uses a Trusted Platform Module (TPM) to provide enhanced protection for your data and to assure early boot component integrity. BitLocker is designed to offer a seamless user experience. The TPM interacts with BitLocker to help provide seamless protection at system startup. Who should use BitLocker Drive Encryption? This guide is intended for the following audiences: IT planners and analysts who are evaluating the product Security architects In this guide Requirements for BitLocker Drive Encryption These steps are for testing only. Before you start
Hacking IPv6 III – IPv6 Spoofing in 6in4 tunnels « iniqua In this post we will show a real risk that happens today in Intenet related with IPv6 tunnels. We have detected that some of the main 6in4 tunnel providers don’t control correctly the IPv6 source filtering in the client access they provide to their clients. This situation leverages a risk that make easy the execution of some attacks that require source IP spoofing. To help the reader understand the risks that involves IP spoofing in the Internet, below are shown a brief list of attacks that take advantage of this risk: SYN flooding desde direcciones IP falseadas.Connection hijacking averiguando el número de secuencia TCPBypass firewallIDLE scanSmurf attackDNS Cache Poisoning … This assessment is only focused on one type of tunnel, the 6in4 type. In our oppinion, these tunnels may happen to be a headache form a security point of view in some points of Internet. Iniqua people have done a brief assessment of the three main IPv6 tunnel provider. Conlusion: Conlusión:
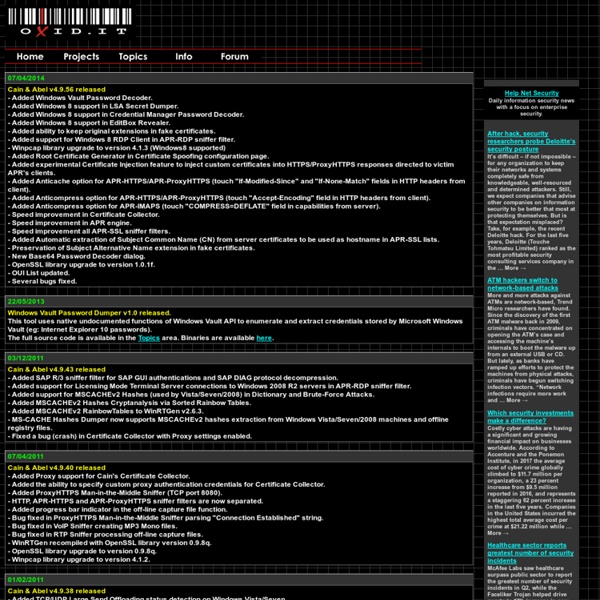
Exploiting Cisco Routers: Part 2 Access Granted -- Now What? Welcome back! The first article in this two-part series covered a few different methods of getting into the target router. Analyzing the Router Config As imagined, router config files can give the penetration tester a TON of useful information. Now that we have the router config, we can analyze it for weaknesses, and hopefully glean other useful information from it. Cracking the Enable Password The first thing we'll do is attempt to "crack" the enable password. This tool could be described as the Swiss Army Knife of cracking tools. Figure 1: Cain and Able Take note of all the other types of passwords Cain and Abel can crack. As displayed in the above image, Cain and Abel was successful in figuring out the enable password. Before we modify anything with the router though, we'll take a quick look at the entire router config. This router is logging at log level 4 to the syslog server 10.0.1.103. Figure 2: Raise the router's log level Summary
John the Ripper password cracker John the Ripper is free and Open Source software, distributed primarily in source code form. If you would rather use a commercial product tailored for your specific operating system, please consider John the Ripper Pro, which is distributed primarily in the form of "native" packages for the target operating systems and in general is meant to be easier to install and use while delivering optimal performance. This version integrates lots of contributed patches adding GPU support (OpenCL and CUDA), support for a hundred of additional hash and cipher types (including popular ones such as NTLM, raw MD5, etc., and even things such as encrypted OpenSSH private keys, ZIP and RAR archives, PDF files, etc.), as well as some optimizations and features. Unfortunately, its overall quality is lower than the official version's. To verify authenticity and integrity of your John the Ripper downloads, please use our PGP public key. There's a wiki section with John the Ripper user community resources.
Create a Shiny Earth with Photoshop 3D Layers In this tutorial I'll show you how to create a shiny planet icon using the 3D features of Photoshop CS4 Extended. This will cover basic information about 3D layers and texture maps. Let's get started! Video Tutorial Our video editor Gavin Steele has created this video tutorial to compliment this text + image tutorial. Step 1 Create a new document which is 1000 pixels wide and 500 pixels high at a resolution of 300 pixels/inch, with a name of "Home." Step 2 We'll be using some texture for our planet. Step 3 Now go to 3D > New Shape From Layer > Sphere. Step 4 The "Earth" layer is now a 3D layer and a cube icon is displayed in the Layers Palette. Step 5 Grab the 3D Rotation Tool, click on the canvas, hold and drag to rotate the sphere and adjust it as you wish. Step 6 The edges of the sphere look aliased at the moment. Step 7 Now click on the Global Ambient Color box and set the color to R:100, G:100, B:100 and hit OK. Step 8 We'll now add a bump map to our planet. Step 9 Step 10 Step 11 Step 12 Step 13
FBI acknowledges more SCADA attacks, increases cyber budget At a recent security conference Michael Welch, the deputy assistant director of the FBI's Cyber Division, gave a speech where he discussed the issue of SCADA security. Information Age magazine reported on his speech and quoted Welch as saying: "We just had a circumstance where we had three cities, one of them a major city within the US, where you had several hackers that had made their way into SCADA systems within the city," We don't know which cities Welch is referring to, but this does bring more light to a subject that has been mired in confusion of late. Many argued that the security of SCADA systems was being exaggerated after it became public that the water treatment attack in Springfield, IL was a false alarm . That of course ignores the attack by pr0f on the City of South Houston's systems and these other three referred to by Welch. Sound too good to be true? The majority of the funding increase will be used to expand their operation from 8 hours/5 days to 24 hours/7 days.
Exploiting Cisco Routers: Part 1 Introduction This two-part article will focus on identifying and exploiting vulnerabilities and poor configurations in Cisco routers. We will then discuss the analysis of the router configuration file and will attempt to leverage this access into other systems. Additionally, we will cover the possibilities of what one may do once access to the device has been achieved. Don't Forget the Router... Pen testers may often go after the more glamorous or fun systems to hack, such as the vulnerable Solaris 8 system, or the Microsoft 2000 server vulnerable to the slew of recent RPC DCOM holes, leaving the core network infrastructure devices alone. As important as these network devices are to the overall security, reliability, and availability of the network, it is pertinent that the pen tester takes a good, hard look at them before blessing them as being secure. Identifying a Router The "User Access Verification" line is a trademark Cisco telnet banner. Identifying Vulnerabilities
Ophcrack Realistic Smoke Effect Photoshop Tutorials Adobe Photoshop, as we all know is rightfully regarded as the Swiss knife of designers all around the world. With Photoshop, you can literally create all kinds of illustrations that you previously only dream about! With this fantastic tool, you can virtually create any effect you want. It’s like an infinite canvas of your dreams. If you have the imagination, sky is the limit. Pin it Smoking is damaging to health they say, indeed, but with Photoshop who needs real smoke? Below the promised showcase of awesome smoke effect Photoshop tutorials. Create Smoke TextMixing type and a smoke image to create a really nice abstract wallpaper. Smoke EffectHow to create smoke effect in 30 seconds. Manipulate Smoke to Create Hyper-Real ImagesLearn to apply the Warp Tool effectively and a few other tricks to make smoke look like a skull. Creating Smoke Like EffectsHow to create subtle smoke-like effect. Smoke Fading EffectSmoking hot girl with smoke fading effect. Photoshop Smoke Tutorial Creating Smoke
Patch Tuesday December 2011 Microsoft finishes out this year of patching with a heavy release that's all over place. While techs were notified of an anticipated 14 bulletins, 13 were released for the month of December. Headline grabbing events and code are addressed in one of them, and while fewer are labelled "Critical", are they any less important? Many speculative bits have been spilled on the group behind Stuxnet and its precursor Duqu, with our own researchers posting at least a half dozen Securelist writeups on Duqu findings alone. The targeted functionality provides TrueType font parsing capabilities for the OS, and the group abused these components by delivering exploits in the form of Word Documents attached to emails interesting to their individual victims, a technique known as spear-phishing. The other headline grabbing event and code that was anticipated to be released is known as the SSL BEAST vulnerability.
Web Server Survey Archives In the April 2014 survey we received responses from 958,919,789 sites — 39 million more than last month. Microsoft made the largest gain this month, with nearly 31 million additional sites boosting its market share by 1.9 percentage points. IIS is now used by a third of the world's websites. Although this is not Microsoft's largest ever market share (it reached 37% in October 2007), this is the closest it has ever been to Apache's leading market share, leaving Apache only 4.7 points ahead. Although Apache gained 6.9 million sites, this was not enough to prevent its market share falling by 0.87 to 37.7%. nginx, which gained 3.1 million sites, also lost some of its market share. More than 70% of this month's new IIS-powered websites are hosted in the US, followed by 22% in China. Many of the new IIS sites hosted by Nobis Technology Group feature similar content and form part of a Chinese link farm. The latest version of Apache (2.4.9) was released on March 17. Active sites Other (more...)
GooBing Detroit A garage in northeast Detroit deteriorates. Lady waving to the street view car in the first image, c. 2009. Nearby the Heidelberg Project, and in the style, though not sure if a Tyree or not. Why Don’t We Own This? This block is incredible. The New York Times visited this block during the Motor City Mapping survey: "Blight, as Karl Baker, one Detroit resident, has seen, tends to spread. Most of the houses nearby are standing but abandoned, and visitors have clearly passed through — empty liquor bottles lie along debris-covered floors near broken windows and doors, every memory of a metal appliance or gutter seems to be gone from some of the homes, and two old couches that were dumped along a lawn are now blanketed by a thick layer of snow. The last neighbor left six months ago, he said, and the single streetlight overhead has not worked for months. That’s a lotta washing machines… Just east of Osborn, in “Burbank”… if anyone actually calls it that. Source: Why Don’t We Own This?
REVERSING RORPIAN – DHCP Hijacking Malware | InfoSec Institute – IT Training and Information Security Resources We have seen our fair share of malware codes from time to time. With the help of disassemblers and debuggers, we have a shot of understanding them. But malware are not that simple to understand, one has to know assembly language. But even knowing the language is not enough by itself, most of the latest malware, if not all, are either packed, encrypted or anything in between. This paper will be the first of many; in helping us understand deciphering codes that malware has to offer. Rorpian worm is the first in line. Rorpian initially allocated a virtual memory space to copy itself. The malware started decrypting codes at the very end of the file in memory. It started slowly. Figure 1 Let’s now take a closer look at the decryption algorithm. The value from DWORD PTR SS:[EBP+10], contains the COUNTER or the number of iterations this block of code will be executed. After executing the first 3 instructions of this decryptor, The following codes below looks complicated but they are not.