How to Hack Someones IP Address 2014 - Come to Hack
Most of you may be curious to know how to find the IP address of your friend’s computer or to find the IP address of the person with whom you are chatting in Yahoo messenger or Gtalk. Finding out someone's IP address is like finding their phone number, an IP address can be used to find the general location where that person lives. Now while most of the tutorials on the net teach you how to steal an ip address via MSN, or any other chat software, in this post I’ll show you how to find IP address of someones computer using script. Using this method for hacking someones ip adress is very easy and effectively, so just follow the steps bellow. NOTE: This tutorial is for educational purposes only, I am NOT responsible in any way for how this information is used, use it at your own risk. How to Hack Someones IP Address? Alright, I'm gonna give you this script, that you write in the index.php. Here is the sript: 1. 2. 3. 4. Hope you'll find this tutorial useful. Introduction1. 4. Time to start.
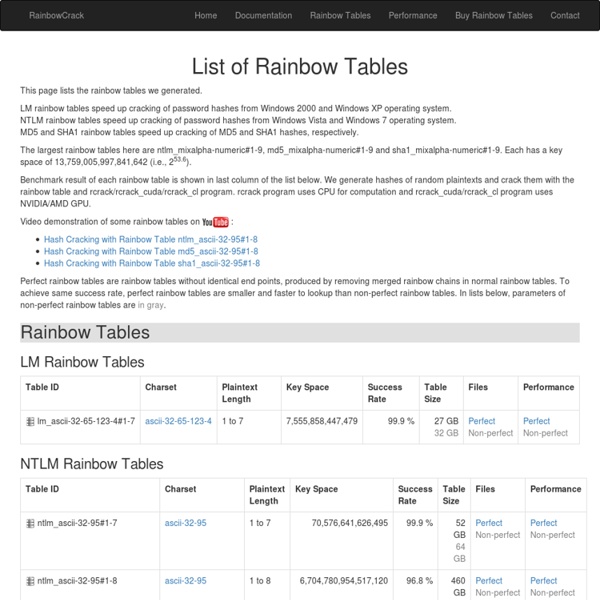
Free Rainbow Tables » Distributed Rainbow Table Generation » LM, NTLM, MD5, SHA1, HALFLMCHALL, MSCACHE
The ABCs of Web Development
Web development can often be an utterly perplexing affair. Today, aimed at beginners, I'd like to introduce you to twenty six concepts or technologies, each mapping to a letter of the alphabet. Sounds wonky? It probably is! Let's get started after the jump. Republished Tutorial Every few weeks, we revisit some of our reader's favorite posts from throughout the history of the site. AJAX stands for Asynchronous JavaScript And XML and is the main driving force behind all these super smooth web applications you've been using over the past few years. AJAX, as a technology, has been pretty much all pervasive. At the center of everything is the XMLHttpRequest which allows calls to be sent and received, after a page has been fully rendered without touching the rest of the page. Related reading B -- Browser A browser is the understated structure on which you frame your magnificent masterpieces, be it websites or applications. CSS is one prong of the front end development trident. E -- Events
Storing Passwords - done right!
Written by: Christoph Wille Translated by: Bernhard Spuida First published: 1/5/2004 Viewed 257725 times. 1766 ratings, avg. grade 4.76 In very many - not to say almost all - Web applications user data is administered, from Web forum to Web shop. These user data encompass login information of the users which contain the password besides the user name - and this in plain text. A security leak par excellence. Why is storing the user name and password in plain text a security leak? How can this security risk be eliminated? What is a Salted Hash? A hash is a numerical value of fixed length which unequivocally identifies files of arbitrary legth. The reason for this is that usually so called 'Dictionary Attacks' are run against hashed passwords - a good example being the MD5 hashed passwords of NT4. The intention behind a Salted Hash is to have this type of attack fail by attaching a random value - the so called salt - to each password and only then compute the hash over password and salt.
Coding An HTML 5 Layout From Scratch
InfoSec Handlers Diary Blog - Hashing Passwords
After talking about SQL Injection, this is the second part of the mini series to help you protect yourself from simple persistent attacks as we have seen them in the last couple months. A common MO employed in these attacks is to steal passwords from a database via sql injection. Later, the attacker will try to use these passwords to break into other sites for which users may choose the same password. Of course, part of the problem is password reuse. But for now, we will focus on the hashing of passwords to make it harder for an attacker to retrieve a users plain text password. First of all: What is hashing? Storing a password as a hash will make it difficult to figure out the actual password a user used. A hash isn't fool proof. Probably the most important defense against rainbow tables is the idea of introducing a "salt". In order to use a "salt", the salt value and the users password are first concatenated, then the string is hashed. - concatenate the two hashes, and hash them again.
30 Useful Responsive Web Design Tutorials
So we’ve reached the end of our “Responsive Web Design week”, tonight’s post will be the last of the series. We are going all out to help you hone your skills in manipulating those codes to respond at will when displayed on different devices. And to do this, we are featuring 30 Responsive Web Design Tutorials found online. This list is not meant to be an exhaustive one but it will get you started on understanding the basics of designing an adaptive website that will cater to all sorts of screen sizes. We’ll start off with introductory tutorials in ‘Breaking the Ice’, something like an RWD: 101 class you should attend to get the hang of the concept before we move on to ‘Start Building’ exercises. Lastly we’ll end with a ‘Do More’ section in which we’ll feature tutorials that play with horizontal layouts, ‘elastic’ videos, drop-down menus and slide-to-top accordion navigations, thumbnails and the sticky issue with tables. But first… Responsive website Navigation Responsive Resume Fluid Grids
HTG Explains: The Difference Between WEP, WPA, and WPA2 Wireless Encryption (and Why It Matters)
Even if you know you need to secure your Wi-Fi network (and have already done so), you probably find all the encryption acronyms a little bit puzzling. Read on as we highlight the differences between encryption standards like WEP, WPA, and WPA2–and why it matters which acronym you slap on your home Wi-Fi network. What Does It Matter? You did what you were told to do, you logged into your router after you purchased it and plugged it in for the first time, and set a password. WEP, WPA, and WPA2: Wi-Fi Security Through the Ages Since the late 1990s, Wi-Fi security algorithms have undergone multiple upgrades with outright depreciation of older algorithms and significant revision to newer algorithms. Wired Equivalent Privacy (WEP) Wired Equivalent Privacy (WEP) is the most widely used Wi-Fi security algorithm in the world. WEP was ratified as a Wi-Fi security standard in September of 1999. Wi-Fi Protected Access (WPA) Wi-Fi Protected Access II (WPA2) Wi-Fi Security History Acquired; Now What?
Welcome [Savannah]
untitled
CyberCIEGE Educational Video Game
an innovative video game and tool to teach computer and network security concepts CyberCIEGE enhances information assurance and cyber security education and training through the use of computer gaming techniques such as those employed in SimCity™. In the CyberCIEGE virtual world, users spend virtual money to operate and defend their networks, and can watch the consequences of their choices, while under attack. Cyber Security Simulation In its interactive environment, CyberCIEGE covers significant aspects of computer and network security and defense. Players of this video game purchase and configure workstations, servers, operating systems, applications, and network devices. CyberCIEGE includes configurable firewalls, VPNs, link encryptors and access control mechanisms. Active Learning with CyberCIEGE This paper describes the game for educators and trainers who may want to incorporate the game into their courses. Questions? Site Map
Difference between WEP, WPA and WPA2 (Which is Secure)
BESbswyBESbswy AddThis What's Next Recommended for you www.guidingtech.com AddThis Hide Show