


How Apple and Amazon Security Flaws Led to My Epic Hacking In the space of one hour, my entire digital life was destroyed. First my Google account was taken over, then deleted. Next my Twitter account was compromised, and used as a platform to broadcast racist and homophobic messages. And worst of all, my AppleID account was broken into, and my hackers used it to remotely erase all of the data on my iPhone, iPad, and MacBook. In many ways, this was all my fault.
Why passwords have never been weaker—and crackers have never been stronger In late 2010, Sean Brooks received three e-mails over a span of 30 hours warning that his accounts on LinkedIn, Battle.net, and other popular websites were at risk. He was tempted to dismiss them as hoaxes—until he noticed they included specifics that weren't typical of mass-produced phishing scams. The e-mails said that his login credentials for various Gawker websites had been exposed by hackers who rooted the sites' servers, then bragged about it online; if Brooks used the same e-mail and password for other accounts, they would be compromised too. Everything You Need to Know About “Click and Drag” If you’re a regular reader of the brilliant xkcd, then you probably got lost in today’s comic, “Click and Drag.” It features three short panels sitting above a seemingly larger, finite panel. However, when you perform the comic’s titular action, click and drag, the larger, bottom panels seems to sprawl on forever in various directions, revealing amusing quips, sad stories, and what is essentially an entire world. There are many impressive facets about “Click and Drag,” such as the panel measuring in at 1.3 terapixels, as well as small community of coders creating applets to help readers better navigate the behemoth. Head on past the break for some stellar info, and maybe set aside some time later today to explore the enormous comic. Comic Size
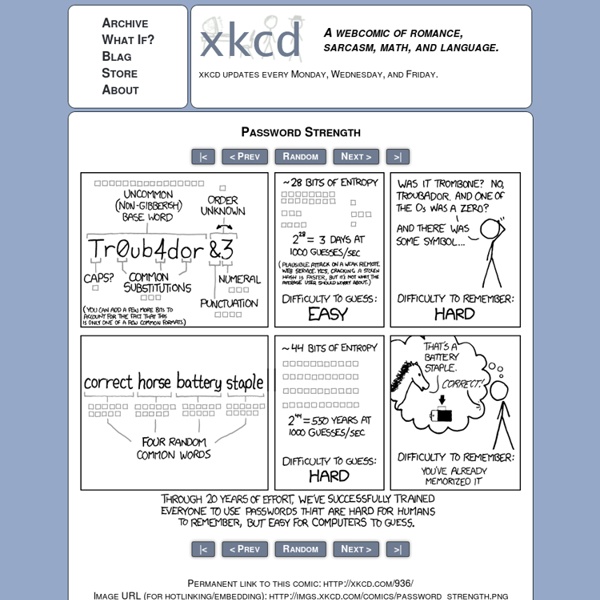
How to stay safe when holiday shopping online It's that time of the year again, when savvy shoppers like yourself head to your favorite online retailers to avoid the ridiculous shenanigans and flesh-pressing of Black Friday. But just because you know enough to buy online doesn't mean that there aren't some good tips worth paying attention to. Here are a few worth repeating for habitual online shoppers. Change your passwords now because chances are, you haven't in a long time. Change your e-mail account password, change your banking password, and change the passwords for online shopping accounts like at Amazon. 25 Worst Passwords of 2011 Pro tip: choosing "password" as your online password is not a good idea. In fact, unless you're hoping to be an easy target for hackers, it's the worst password you can possibly choose. "Password" ranks first on password management application provider SplashData's annual list of worst internet passwords, which are ordered by how common they are.
10,000 Top Passwords Back when I wrote Perfect Passwords, I generated a list of the top 500 worst (aka most common) passwords which seems to have propagated quite a bit across the internet, including being mentioned on Gizomodo, Boing Boing, Symantec, Laughing Squid and many other sites. Since then I have collected a large number of new passwords bringing my current list to about 6,000,000 unique username/password combos, including many of those that have been recently made public*. At some point I will make this full data set publicly available but in the meantime, I have decided to release the following list of the top 10,000 most common passwords. This list is ranked by counting how many different usernames appear on my list with the same password. Relativistic Baseball What would happen if you tried to hit a baseball pitched at 90% the speed of light? - Ellen McManis Let’s set aside the question of how we got the baseball moving that fast.
6 Techniques to Use an Off Camera Flash Despite what you may have been told, you don’t need an extensive lighting setup to do professional quality studio work. In the seminar below, speedlight master, Bob Harrington, explains to users how to get started using minimal equipment. Throughout the nearly two-hour long presentation, Harrington gives a live demonstration on six different ways to use only a single speedlight. What he is able to do with one light and limited space is oddly inspiring. Take a look for yourself: “The joke in my house is that my wife gets Golf Digest and I get Vanity Fair.
A brief Sony password analysis So the Sony saga continues. As if the whole thing about 77 million breached PlayStation Network accounts wasn’t bad enough, numerous other security breaches in other Sony services have followed in the ensuing weeks, most recently with SonyPictures.com. As bad guys often like to do, the culprits quickly stood up and put their handiwork on show. This time around it was a group going by the name of LulzSec. Here’s the interesting bit:
What's My Pass? » The Top 500 Worst Passwords of All Time From the moment people started using passwords, it didn’t take long to realize how many people picked the very same passwords over and over. Even the way people misspell words is consistent. In fact, people are so predictable that most hackers make use of lists of common passwords just like these. To give you some insight into how predictable humans are, the following is a list of the 500 most common passwords. If you see your password on this list, please change it immediately. Keep in mind that every password listed here has been used by at least hundreds if not thousands of other people.
Arobas Music Guitar Pro Description The Guitar Pro application allows all guitarists to enjoy the display, playback, as well as an easy tablatures writing tool, right from their device. This mobile version of the famous Guitar Pro tab-editing program is the ideal companion for you to practice your favorite songs and share them at any time, anywhere!