

Tutorial: Spring MVC + Security + Hibernate + MySQL. Spring has a lot of different modules.
All of them are useful for the concrete purposes. Today I’m going to talk about Spring Security. This module provides flexible approach to manage permitions for access to different parts of web-application. In the post I’ll examine integration of Spring MVC, Hibernate, MySQL with Spring Security. A regular case for any web-application is separation of functionality between some user groups. The goal As an example I will use sample Spring MVC application with Hibernate. Preparation In order to make Spring Security available in a project, just add following dependencies in a pom.xml file: I have to create three tables in the database and insert several records there. And here is a code for the roles and users: INSERT INTO hibnatedb.roles (role) VALUES ('admin'), ('moderator'); INSERT INTO hibnatedb.users (login, password) VALUES ('moder', '111111'), ('adm', '222222'); INSERT INTO hibnatedb.user_roles (user_id, role_id) VALUES (1, 2), (2, 1); Main part And.
Spring Security,Mysql and Hibernate Annotations with Custom UserDetails Service. Customizing Messages with Custom AbstractUserDetailsAuthenticationProvider. Package com.vajjala.testng.adtf.hbm;
Behind the Spring Security Namespace. With the introduction of the security schema in Spring Security 2, it became much easier to get a simple secured application up and running.

In older versions, users had to declare and wire-up all the implementation beans individually, resulting in large and complicated Spring application context files which were difficult to understand and maintain. There was a pretty steep learning curve and I can still remember that it took me some time to get my head round it all when I started working on the project (then Acegi Security), back in 2004. On the positive side, this exposure to the basic building blocks of the framework meant that once you had managed to put together a working configuration, it was almost impossible not to have gained at least some awareness of the important classes and how they work together. This knowledge in turn put you in a good position to take advantage of the opportunities for customization that are one of the biggest benefits of using Spring Security.
Spring Security form login using database. In this tutorial, we will show you how to perform database authentication (using both XML and Annotations) in Spring Security.

Technologies used : Spring Security form login example. By default, if no login form is specified, Spring Security will create a default login form automatically.
Please refer to this – Spring Security hello world example. In this tutorial, we will show you how to create a custom login form for Spring Security (XML example). Technologies used : 2. Session Management. HTTP session related functonality is handled by a combination of the SessionManagementFilter and the SessionAuthenticationStrategy interface, which the filter delegates to.
Typical usage includes session-fixation protection attack prevention, detection of session timeouts and restrictions on how many sessions an authenticated user may have open concurrently. 12.1 SessionManagementFilter The SessionManagementFilter checks the contents of the SecurityContextRepository against the current contents of the SecurityContextHolder to determine whether a user has been authenticated during the current request, typically by a non-interactive authentication mechanism, such as pre-authentication or remember-me [].
If the repository contains a security context, the filter does nothing. If it doesn't, and the thread-local SecurityContext contains a (non-anonymous) Authentication object, the filter assumes they have been authenticated by a previous filter in the stack. 3. Security Namespace Configuration. Namespace configuration has been available since version 2.0 of the Spring framework.
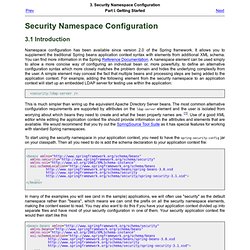
It allows you to supplement the traditional Spring beans application context syntax with elements from additional XML schema. You can find more information in the Spring Reference Documentation. A namespace element can be used simply to allow a more concise way of configuring an individual bean or, more powerfully, to define an alternative configuration syntax which more closely matches the problem domain and hides the underlying complexity from the user. A simple element may conceal the fact that multiple beans and processing steps are being added to the application context. For example, adding the following element from the security namespace to an application context will start up an embedded LDAP server for testing use within the application: This is much simpler than wiring up the equivalent Apache Directory Server beans. <beans xmlns=" xmlns:security=" xmlns:xsi=" xsi:schemaLocation=" ...