

Linux. An A-Z Index of the Bash command line for Linux. Commands marked • are bash built-ins Many commands particularly the Core Utils are also available under alternate shells (C shell, Korn shell etc). More bash commands: Linux Command Directory from O'Reilly, GNU CoreUtils.SS64 bash discussion forumLinks to other Sites, books etc. Linux Administration Made Easy. Welcome to LWN.net [LWN.net]
Linux Software. Welcome to Linux From Scratch! DistroWatch.com: Put the fun back into computing. Use Linux, BSD. Jacksonville Linux Users Group. Introduction to Linux. The Linux Documentation Project. Red Hat Enterprise Linux. Linux cmd cht sht. Linux cheat sheet. Fwunixref. LinuxCommand.org: Resources. Linux.org.
Oracle VM VirtualBox. Join In. Geek Out. Entry Level Credential: Linux Essentials. Linux adoption continues to rise world-wide as individual users, government entities and industries ranging from automotive to space exploration embrace open source technologies.

This expansion of open source in enterprise is redefining traditional Information and Communication Technology (ICT) job roles to require more Linux skills. Whether you’re starting your career in Open Source, or looking for advancement, independently verifying your skill set can help you stand out to hiring managers or your management team. The Linux Essentials Professional Development Certificate (PDC) is a great way to show employers that you have the foundational skills required for your next job or promotion.
It also serves as an ideal stepping-stone to the more advanced LPIC Professional Certification track for Linux Systems Administrators. The Linux Essentials Professional Development Certificate validates a demonstrated understanding of: Scp(1): secure copy. Name scp - secure copy (remote file copy program) Synopsis scp [-1246BCpqrv] [-c cipher] [-F ssh_config] [-i identity_file] [-l limit] [-ossh_option] [-P port] [-S program] [ [user@]host1:]file1 ... [ [user@]host2:]file2 Description scp copies files between hosts on a network.
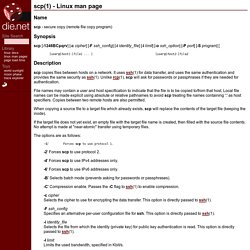
File names may contain a user and host specification to indicate that the file is to be copied to/from that host. When copying a source file to a target file which already exists, scp will replace the contents of the target file (keeping the inode). If the target file does not yet exist, an empty file with the target file name is created, then filled with the source file contents.
The options are as follows: The Original Magazine of the Linux Community. Raspberry Pi. Adafruit Industries, Unique & fun DIY electronics and kits. Log Files and Linux. Log Files and Linux. by Isaac Ok.

Adrian asked me to write up a quick synopsis of the "lecture" I gave at the first meeting. This is pretty basic stuff. So if you already know how Linux log files work, don't expect to learn anything new or enlightening here. Most versions of Linux, as far as I'm aware, use syslogd as their logging utility. syslogd is a fairly easy tool to learn and use. The GNU Awk User’s Guide. This file documents awk, a program that you can use to select particular records in a file and perform operations upon them.
Copyright © 1989, 1991, 1992, 1993, 1996–2005, 2007, 2009–2014 Free Software Foundation, Inc. This is Edition 4.1 of GAWK: Effective AWK Programming: A User’s Guide for GNU Awk, for the 4.1.1 (or later) version of the GNU implementation of AWK. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.3 or any later version published by the Free Software Foundation; with the Invariant Sections being “GNU General Public License”, the Front-Cover texts being (a) (see below), and with the Back-Cover Texts being (b) (see below). A copy of the license is included in the section entitled “GNU Free Documentation License”. “A GNU Manual” “You have the freedom to copy and modify this GNU manual.
Short Table of Contents Table of Contents Foreword Arnold Robbins and I are good friends. Preface. Grep () NOTE: click here if you get an empty page. grep, egrep, fgrep - print lines matching a pattern grep [options] PATTERN [FILE...] grep [options] [-e PATTERN | -f FILE] [FILE...]
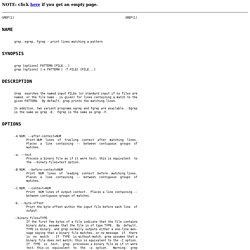
Grep searches the named input FILEs (or standard input if no files are named, or the file name - is given) for lines containing a match to the given PATTERN. By default, grep prints the matching lines. In addition, two variant programs egrep and fgrep are available.