

Creativecommons. 100 Websites You Should Know and Use (updated!) Entertainment Meet David Peterson, who developed Dothraki for Game of Thrones There are seven different words in Dothraki for striking another person with a sword.

Among them: “hlizifikh,” a wild but powerful strike; “hrakkarikh,”a quick and accurate strike; and “gezrikh,” a fake-out or decoy strike. But you won’t find these words in George R. How to stop the NSA spying on your data - tech - 13 June 2013. Revelations about government snooping show just how much they know about us.

But there are ways to opt out Editorial "Big brother needs a data privacy policy" BIG BROTHER really is watching you. A series of revelations over the past week has revealed the extent of the US government's snooping. But there are ways that the average citizen can avoid the prying eyes of the state. Last week, whistleblower Edward Snowden – a former contractor with the National Security Agency (NSA) – told UK newspaper The Guardian that the NSA not only has details of phone calls made by millions of Verizon customers, it also has some form of access to its citizens' internet activity as part of a programme named Prism. The details of exactly how the NSA accesses personal data held by US internet companies are still unclear (see "Split the difference").
Phone calls alone can provide plentiful information. But for citizens who want to guard their privacy, there are a number of options. WiFi públicas: cómo defender tu privacidad. Las redes WiFi públicas tienen un lado oscuro: cualquiera que comparta la conexión contigo y use aplicaciones de escucha puede ver qué contraseñas usas y qué mensajes envías, además de poder echarte de la red sin mediar palabra.

Descubre quién accede a tu WiFi con WiFi Guard. La mayoría de nosotros accedemos a Internet a través de WiFi.

La conexión WiFi es rápida y cómoda, ya que te permite estar en cualquier habitación o rincón de tu casa sin necesidad de cables con tu ordenador, teléfono, tableta o videoconsola. Precisamente esa facilidad de acceso hace al WiFi tan frágil. Comandos en Linux: Aprovechando la Consola. En la actualidad, Linux funciona con entornos gráficos, como GNOME o KDE, donde cualquier elemento o acción están representados por iconos.

Cómo descubrir si un intruso ha usado tu ordenador. Cuando alguien entra en el sistema sin tu permiso y abre tus archivos, las consecuencias pueden ser catastróficas para tu privacidad.

Y es que tu ordenador contiene casi toda tu vida: documentos, fotos, contraseñas... Tanto si sospechas que un intruso ha entrado en tu ordenador como si ya lo sabes y deseas saber qué ha visto, borrado o modificado, tranquilízate: hay muchas maneras gratuitas de averiguar qué ha pasado. Voy a enseñarte los métodos de investigación forense más sencillos y fiables para recabar información que te permita establecer si alguien entró en tu máquina y qué hizo con tus archivos. ¿Cómo puede alguien entrar en tu ordenador sin permiso? Debes imaginar tu PC o Mac como una casa con muchas puertas. Byzantium, a bootable Linux with "Ad-hoc wireless mesh networking for the zombie apocalypse" 10 plataformas innovadoras para aprender programación. Si no aprendemos a programar, nos arriesgamos a ser programados...

Programa o sé programado. -- Douglas Rushkoff Creo que a todos aquí nos queda claro que la educación formal, incluso la universitaria, está desfasada si no es que rebasada en su totalidad por Internet. Con esto me refiero a que la educación formal no aprovecha -y a veces ni siquiera (re)conoce- para su beneficio las herramientas técnicas y metodológicas que Internet no está legando. Hablo de herramientas que facilitan y potencian el aprendizaje en términos colaborativos, masivos, autónomos, innovadores, críticos, ágiles, evolutivos y usables. 10 trucos para parecer un maestro hacker del PC. ¿No consigues que tus amigos se queden asombrados con tus conocimientos informáticos y te alaben como el Rey del PC?

Mozilla Webmaker. WiFi Pineapple Mark IV. Command the WiFi landscape and direct attacks from a live recon dashboard, passively monitoring all devices in the vicinity. Limit the audit to specified clients and access points within the scope of engagement and ensure zero collateral damage. Acquire clients with a comprehensive suite of WiFi man-in-the-middle tools specializing in targeted asset collection.
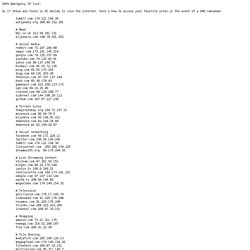
Record and analyze logs, generate emailed reports at set intervals, and identify vulnerable devices in your organization. Cryptocat. Convertir en texto (TXT) los archivos contenidos en una carpeta. The web performance & security company. VPN providers list. List of Pirate Bay proxies. #3038363. SOPA Emergency IP list: So if these ass-fucks in DC decide to ruin the internet, here’s how to access your favorite sites in the event of a DNS takedown tumblr.com 174.121.194.34 wikipedia.org 208.80.152.201 # News bbc.co.uk 212.58.241.131 aljazeera.com 198.78.201.252.
Anonymous E-mail - How to Stay Anonymous Online. Safe Surfing First, make sure your browser isn't storing too much about you.

In the settings menu, turn off the ability for the browser to store the passwords you use to access websites and services. That can be a pain, as you should have a different password on every service you use, so an alternative is to use a password manager, like PCMag's five-star Editors' Choice, LastPass. Online Privacy Test - Check Your Internet Anonymity and Privacy. How to secure your computer and surf fully Anonymous BLACK-HAT STYLE. Project Gutenberg - free ebooks. Internet gratis Android Telcel. Free Open-Source On-The-Fly Disk Encryption Software for Windows 7/Vista/XP, Mac OS X and Linux - Downloads. Alpha: Computational Knowledge Engine. VPN Service - Surf anonymous. Free Proxies: Freeproxies.org hosts the best cgi proxy servers on the web, for free.
10 alternativas para The Pirate Bay. La verdad es que estoy bastante decepcionado por la venta de The Pirate Bay a Global Gaming Factory X. ¿Por qué? Porque considero que esta nueva empresa, que cotiza en la bolsa, no podrá continuar con lo que hacían los administradores del tracker porque su fin es ganar dinero. Proxy 4 Free - Free Proxy Servers - Protect Your Online Privacy with Our Proxy List. 7 huellas que dejas en el PC sin saberlo. La privacidad es un asunto que nunca se toma lo bastante en serio. Computer Science 101. UPDATE: we're doing a live, updated MOOC of this course at stanford-online July-2014 (not this Coursera version). See here: CS101 teaches the essential ideas of Computer Science for a zero-prior-experience audience. Computers can appear very complicated, but in reality, computers work within just a few, simple patterns. CS101 demystifies and brings those patterns to life, which is useful for anyone using computers today.
Online Etymology Dictionary. Michael Sheldon's Stuff » Free (as in GPL2) translation dictionaries for the Kindle. Virtual-Browser™ - Browse and surf safely & anonymously. Anonymous File Upload on AnonFiles.com. 10 aplicaciones Open Source para edición de multimedia. Una de las muchas ventajas del software libre es que surge para suplir necesidades compartidas entre usuarios de todo el planeta, y qué uso más común que el de la edición de multimedia.
Para todos los gustos y sistemas operativos pues todos funcionan en Windows, GNU/Linux y Mac -otro punto a favor posibilitado por el tratamiento ilimitado del código fuente-, están aquí algunas de las alternativas más llamativas: PDF to Flash page flip book – Submit to free convert PDF to magazine. What kind of PDFs that I can upload? You can upload any PDF with unlimited pages for free, your PDF file size is up to 10MB, or 100 MB for paid users. To save your wait time and our drive space, small PDF file is always recommended. Please make sure all pages are in the same page size, otherwise some pages might be unexpected trimmed or be stretched. Edición Especial. Fake Name Generator - StumbleUpon. Graphing Calculator. Ngram Viewer. More Info About You. Start 2012 by Taking 2 Minutes to Clean Your Apps Permissions.
HOWTO: GMask para principiantes. Bueno, este hilo va orientado a la gente que desconoce por completo GMask, vayamos por partes como dijo Jack el destripador... Que es GMask? Es un programa que permite aplicar una serie de filtros para ocultar una foto (o un trozo de una foto). Se utiliza básicamente para 3 fines: 1) Censurar imágenes2) Ocultar porno o CP a newfags3) Pura diversión, como es el caso de éste thread Que diferencia hay en usar GMask o usar el Paint? Text-to-Speech Voices.
Mobile Anonymity and Censorship Circumvention: How to Browse the Web Anonymously On Your Phone. Posted by MelissaLoudon on Oct 13, 2011 Abstract: If you don’t want someone to know that you were accessing a particular web site (or that you were accessing it at a particular time, such as when inflammatory content was posted), you need to anonymize your mobile browsing. Online Hearing Test - Free, Quick, No Sign Up Required. The 60 second online hearing test. It's free, simple and no sign up required. How high can you hear? Códigos HTML - Tabla de caracteres y símbolos. EyeQuant Attention Analytics. PAGINA-PRINCIPAL-DEL-CURSO-RECONOCIMIENTO-AUTOMATICO-DEL-HABLA. Versión en inglés 6.345 Automatic Speech Recognition, Spring 2003. Free Online Course Materials. Udacity - Educating the 21st Century.
Launches online learning initiative. MIT today announced the launch of an online learning initiative internally called “MITx.” MITx will offer a portfolio of MIT courses through an online interactive learning platform that will: