

William Rush, Jr
Retired U.S. Navy Pursuing B.A.S in Computer Systems Networking and Telecommunication.
WinWithWindows. Capstone. Capstone 2015. Wire Shark. Security. Security. Amazon Web Services. Enterprise Systems Intergration. Coding. Gaming. Problem Solving & Decision-Making Thinking Skills. 10 Handy WiFi Troubleshooting Tools. Carrier Sense Multiple Access (CSMA) Carrier Sensed Multiple Access (CSMA) : CSMA is a network access method used on shared network topologies such as Ethernet to control access to the network.
Devices attached to the network cable listen (carrier sense) before transmitting. If the channel is in use, devices wait before transmitting. MA (Multiple Access) indicates that many devices can connect to and share the same network. All devices have equal access to use the network when it is clear. CSMACD Algorithm svg. HP MSM-802.11n Dual Radio Access Point Series (QuickSpecs/c04111561.pdf) Welcome to Forbes. WIRED. The Hottest IT Skills And Salaries. Keeping IT skills current is an ongoing challenge, but training and certification pay off in higher salaries.

Find out which roles, skills, certifications, and industries are hot now. 1 of 8 IT professionals don't have it easy, but the march of technology is making them more important than ever. And those who master skills in high demand can reap respectable salaries, according to the latest annual survey from Global Knowledge.
It comes as little surprise the IT skills most prized by hiring managers today were in information security. Open Wireless Movement. FREE Computer Training - Computer Repair Classes - Laptop Repair Instruction - Data Recovery Lessons - Web Design Seminars - Computer Security Counseling. MCSA: The foundation for your career in IT. IP subnetting made easy. What Is a Packet Sniffer? (with pictures) A packet sniffer is a device or program that allows the user to eavesdrop on traffic traveling between networked computers.

The program will capture data that is addressed to other machines, saving it for later analysis. All information that travels across a network is sent in "packets. " For example, when an email is sent from one computer to another, it is first broken up into smaller segments. Each segment has the destination address attached, the source address, and other information such as the number of packets and reassembly order. Common ports. CompTIA A Plus Training Kit Exam 220 801 and Exam 220 802. Cloud Storage and Backup News, Reviews and Promos - Cloud Storage Buzz. Comcast is first U.S. ISP to offer IPv6 to home gateway users. DENVER - Comcast has moved into the next phase of its IPv6 roll-out, becoming the first U.S. broadband ISP to enable next-gen Internet services for residential customers that use home gateways.

Comcast plans to announce its IPv6 service for home gateway users later this month, but company officials released a few details about this service at the North American IPv6 Summit held here this week. John Brzozowski, chief architect for IPv6 and distinguished engineer with Comcast, said IPv6 service was already available to home gateway users in two U.S. cities. The service is available for residential customers that use one of six home gateways, which are specific IPv6-enabled models from D-Link, Linksys and Netgear that are listed at this Web site. "When we launch this service in an area, we are instantly seeing IPv6 traffic among home networking users that have IPv6 turned on by default," Brzozowski said.
Stick to limited IPv6 deployments, businesses warned. Companies should only deploy IPv6 for services they provide over the internet, as the protocol is still riddled with security flaws, an expert has urged.

The German researcher Marc Heuse, who has been analysing IPv6 security for almost a decade, said on Wednesday that there is no business case for deploying IPv6 on internal systems. The Reason Enterprises Aren't Deploying IPv6. I was doing some reading here, and it got me to thinking.

IPv6 has been around for a while, so why isn’t IPv6 widely deployed? Why don’t I see blog articles from the trenches about experiences learned during IPv6 deployments? Why aren’t carriers beating down my door to sell me IPv6 connectivity (goodness knows they have my number)? The reason is simple: the vast majority of us have no need to deploy IPv6. Therefore, we aren’t. Networking Academy. Hacking for Beginners. One of the best things about computers is how dynamic they are.
There is so much information about computers and it changes constantly. As a hacker, you are at the leading edge of changes to technology. This makes it a very exciting and interesting field of study and can even lead to some awesome job opportunities as a computer security expert. Secure content-sharing that users and IT love and adopt. Group Policy. Hyper-V. Hyper-V, codenamed Viridian[1] and formerly known as Windows Server Virtualization, is a native hypervisor; it can create virtual machines on x86-64 systems.[2] Starting with Windows 8, Hyper-V supersedes Windows Virtual PC as the hardware virtualization component of the client editions of Windows NT.
A server computer running Hyper-V can be configured to expose individual virtual machines to one or more networks. Hyper-V was first released along Windows Server 2008 and became a staple of the Windows Server family ever since. History[edit] A beta version of Hyper-V was shipped with certain x86-64 editions of Windows Server 2008. The finalized version was released on June 26, 2008 and was delivered through Windows Update.[3] Hyper-V has since been released with every version of Windows Server.[4][5][6] Microsoft provides Hyper-V through two channels:
Bluesnarfing. Bluesnarfing is the unauthorized access of information from a wireless device through a Bluetooth connection, often between phones, desktops, laptops, and PDAs (personal digital assistant.).

This allows access to a calendar, contact list, emails and text messages, and on some phones, users can copy pictures and private videos. Both Bluesnarfing and Bluejacking exploit others' Bluetooth connections without their knowledge. While Bluejacking is essentially harmless as it only transmits data to the target device, Bluesnarfing is the theft of information from the target device. Current mobile software generally must allow a connection using a temporary state initiated by the user in order to be 'paired' with another device to copy content. Bluejacking. This Siemens M75 is Bluejacking the Sony Ericsson K600i pictured below This Sony Ericsson K600i is getting Bluejacked by the Siemens M75 pictured above.
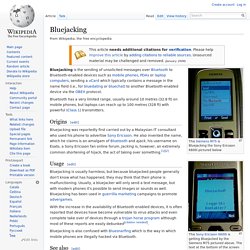
The text at the bottom of the screen reads "Add to contacts? " in Norwegian. Bluejacking is the sending of unsolicited messages over Bluetooth to Bluetooth-enabled devices such as mobile phones, PDAs or laptop computers, sending a vCard which typically contains a message in the name field (i.e., for bluedating or bluechat) to another Bluetooth-enabled device via the OBEX protocol. Bluetooth has a very limited range, usually around 10 metres (32.8 ft) on mobile phones, but laptops can reach up to 100 metres (328 ft) with powerful (Class 1) transmitters.
Origins[edit] VOIP Basics. NAT and PAT - What's the Difference? NAT and PAT - What's the Difference? Posted by Kelson Lawrence on Tue, Feb 08, 2011 @ 10:22 AM By Brian Scheibe Network Address Translation (NAT) and Port Address Translation (PAT) both map IP addresses on an internal network to IP addresses on an external network. Which method of address translation you use depends on the types of networks that you are translating and the number of available IP addresses that you have.
If you are connecting a site in the 10.10.10.0 network to a site in the 10.10.20.0 network, you could use NAT to translate 10.10.10.0 IP addresses to available 10.10.20.0 IP addresses so that hosts on the 10.10.10.0 network can access data and use network resources on the 10.10.20.0 network. PAT attempts to use the original source port number of the internal host to form a unique, registered IP address and port number combination.
Cheat Sheets. Download All (.zip) Wall Posters (36" x 24") Interior Gateway Protocols v1.0 (1 page) Protocols. List of commercial open-source applications and services. How To Install and Configure OpenVPN On Your DD-WRT Router. Cisco IOS Switching Services Configuration Guide, Release 12.2 - Routing Between VLANs Overview [Cisco IOS Software Releases 12.2 Mainline] Routing Between VLANs Overview This chapter provides an overview of VLANs. Submarine Cable Map 2014. Convert your existing Windows XP system into a virtual machine. Run your Windows XP system in Windows 8 with VMware In a recent series of articles culminating with Make USB devices accessible to a Windows XP virtual machine, I showed you how to create a Windows XP virtual machine in Windows 8 using the built-in Client Hyper-V tool.
I've received quite a few emails about that series and several people have asked about the possibility of converting their existing Windows XP installation into a virtual machine. 10 best practices for successful project management. The right mix of planning, monitoring, and controlling can make the difference in completing a project on time, on budget, and with high quality results. These guidelines will help you plan the work and work the plan. The right mix of planning, monitoring, and controlling can make the difference in completing a project on time, on budget, and with high quality results. Three methods for transferring files to and from your Android tablet. If your Android tablet doesn't have a USB port, you can still easily transfer your files to and from a PC. Jack Wallen explains three ways this can be done. Transferring files to and from your tablet can sometimes be difficult, especially if it doesn't include a standard USB port.
Five free and reliable cloning tools. Image your drives for free with the help of one of these reliable tools. Packet Tracer. PDF Eraser - Erase and Delete PDF Text, Images or Forms - Download. Computer hardware chart. Create apps with the best app builder for iPhone and... Miro Video Converter FREE - Convert any video to MP4, WebM (vp8), iPhone, Android, iPod, iPad, and more. 100 Useful Tips and Tools to Research the Deep Web. Preparing for the Windows 10 Upgrade: What Your PC Needs. Any version of Windows just performs better on newer equipment. A Guide to the Windows 10 Start Menu. Since the release of Windows 95, the Start Menu has been the primary way for users to access their files and applications.
Microsoft attempted to move away from this setup with Windows 8, creating a serious backlash. Upgrade from Windows 7 to Windows 10, on the same hardware? How to Configure Windows 10 to Protect Your Privacy. How To: Import Internet Favorites into Windows 10's Microsoft Edge from Other Browsers. Restore your computer from a system image backup. CloneApp Backs Up All Your Windows Program Settings. The Best Free Software for 2015. Five free apps for dealing with hardware problems.