

How to find Wi-Fi password of all Connected Networks using CMD. How To Find Wi-Fi Password Using CMD Of All Connected Networks In this day and age of Internet, the Wi-Fi router and data connection have become a fundamental amenity for every user.

One of the first thing that a user does after waking up is switching on his/her Wi-Fi router while there are some users who never switch off their routers. The Internet plays such an important role that people use it for completing their day to day chores as well as for relaxation. Considering that Wi-Fi has become a central part of our life, it is quite easy to forget the Wifi password. So, here is a simple solution to find the connected Wi-Fi network passwords through command prompt.
Vírus no celular: aprenda como escanear apps de Android em formato APK. Kaspersky Cyberthreat real-time map. Top 30 Best Android Hacking Apps And Tools Of 2017. Best Android hacking apps — one of the most searched queries in Google.

Nowadays every geek wants to turn their Android smartphone into a hacking device. But most of them don’t know where to start, what to install. So today we are going to list some great hacking tools, to make hacking possible in Android. Password Guessing Framework. DroidDucky - Can an Android quack like a duck? Intro In this article, I’m going to present a way to perform Keystroke Injection attacks from a plain Android device.
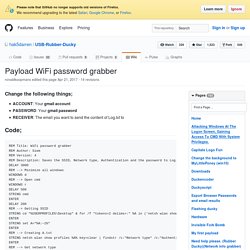
A keyboard is the main way of communicating between the user and the computer. Because of this special connection, computers always trust keyboards. Wibrplus-1.0.33.33. Complex Recon Script · Insecurities/RubberDucky Wiki. This script does a lot, but has some huge key features which are worth going over.
It displays the current WiFi Connections credentials by exploiting the * character in Command Prompt, which acts as "everything". So in this script we are using the * in netsh wlan show profile name=* key=clear Thus, regardless of the access points name, so long as its wifi it will display the key(password) Another thing we are "exploiting" is the ability to copy command prompts output, and sending it via SMTP through Powershell. The Notepad file which will copy all of command Prompts output is located in the windows temp folder (C:\Windows\Temp\XInfo.txt) which is a relatively common location, but also not often looked through.
Another thing this script does is display open ports on the computer. DesignativeDave/androrat: Remote Administration Tool for Android devices. [APP][BETA]USB Cleaver - USB Password Recove… Hi there!
![[APP][BETA]USB Cleaver - USB Password Recove…](http://cdn.pearltrees.com/s/pic/th/cleaver-password-development-153049818)
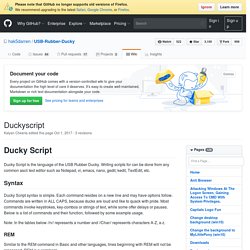
Those of you who are familiar with USB Haksaw or USB Switchblade then you probably know what this app is all about. For those who a not familiar GOTO Description just like the USB Switchblade you can select the payload you want to use to shorten the hack time. This program is very beta! Code Archive - Long-term storage for Google Code Project Hosting. Droid Pentest. Penetrate pro v2.11.1 android - Download - 4shared - Leonardo machado. Download dSploit.apk. Hackode. Fing - Network Tools. zANTI - Mobile Security Risk Assessment. Payload WiFi password grabber · hak5darren/USB-Rubber-Ducky Wiki. Change the following things; ACCOUNT: Your gmail accountPASSWORD: Your gmail passwordRECEIVER: The email you want to send the content of Log.txt to Code; REM Title: WiFi password grabber REM Author: Siem REM Version: 4 REM Description: Saves the SSID, Network type, Authentication and the password to Log.txt and emails the contents of Log.txt from a gmail account.
Change log; OriginalBug fixes and narrowed commandsSend contents of Log.txt instead the file itselfRemoved the space as delimiterAdded the STRING set A="%A:~1%" to be able to use SSID's with spaces as well Suggestions; If you have any suggestions, write them down here. For me i needed to add a DELAY 50 betwin the powershell exit and the cmd exit.. The cmd prompt must be elevated to get any passwords. Countercept/doublepulsar-detection-script: A python2 script for sweeping a network to find windows systems compromised with the DOUBLEPULSAR implant. Downloads · hak5darren/USB-Rubber-Ducky Wiki. Duckyscript · hak5darren/USB-Rubber-Ducky Wiki. Ducky Script Ducky Script is the language of the USB Rubber Ducky.
Writing scripts for can be done from any common ascii text editor such as Notepad, vi, emacs, nano, gedit, kedit, TextEdit, etc. Syntax Ducky Script syntax is simple. Each command resides on a new line and may have options follow. Note: In the tables below //n// represents a number and //Char// represents characters A-Z, a-z. Similar to the REM command in Basic and other languages, lines beginning with REM will not be processed. REM The next three lines execute a command prompt in Windows GUI r STRING cmd ENTER DEFAULT_DELAY or DEFAULTDELAY. Index. 2.
Act normal If you are a high-risk source, avoid saying anything or doing anything after submitting which might promote suspicion. In particular, you should try to stick to your normal routine and behaviour. 94% of Microsoft vulnerabilities can be easily mitigated. If you want to shut out the overwhelming majority of vulnerabilities in Microsoft products, turn off admin rights on the PC.

That's the conclusion from global endpoint security firm Avecto, which has issued its annual Microsoft Vulnerabilities report. It found that there were 530 Microsoft vulnerabilities reported in 2016, and of these critical vulnerabilities, 94% were found to be mitigated by removing admin rights, up from 85% reported last year. This is especially true with the browser, for those who still use Microsoft's browsers. 100% of vulnerabilities impacting both Internet Explorer and Edge could be mitigated by removing admin rights, Avecto reported. Criminal Record, Background Check, Trace email, Phone Number lookup, People search, cell phone number search, License Plate Search.
How over 30 Jeeps were Hacked into and Driven Away. It took these high-tech hackers just 6 minutes to steal Dodge and Jeeps cars Last year a report revealed how hackers managed to hack into a jeep and take full control of the vehicle.

The shocking report detailed several incidents within Houston area in which hackers used their laptops, mobile phones and stolen software to hack into stationary Jeep Cherokees. The hackers then managed to get the cars into motion and drive them away. Telegram App Hacked Again; Millions of Contacts Revealed. Beware; Hackers targeting Pokemon Go Users with Smishing Scam. New Trojan Turns Linux Devices into Botnet. New Linux Trojan turns infected Linux Devices and websites into P2P botnets and threatens users with DDoS and ransom!
— This Trojan is one of its kind! Linux is considered as one of the most secure operating systems but things seem to be changing as cyber criminals are equipping themselves with the latest tools. A TINY BIT about Cryptography. INFOWAR. NSA classifies Linux Journal readers, Tor and Tails Linux users as "extremists" Are you a Linux Journal reader or use software such as Tor and Tails Linux? If so, you've probably been flagged as an "extremist" by the NSA. Leaked documents related to the XKeyscore snooping program reveal that the agency is targeting anyone who is interested in online privacy, specifically those who use the aforementioned software and visit the Linux user community website. XKeyscore is a collection and analysis software that was among a number of surveillance programs revealed by Edward Snowden last year.
Its source code (basically a rule file), which has been obtained and analyzed by members of the Tor project and security specialists for German broadcasters NDR and WDR, identifies two German Tor Directory Authority servers as being under surveillance by the NSA. Antivirus Software Download. GitHub - BastilleResearch/keysniffer: KeySniffer device discovery tools and public advisories. 'No More Ransom' Anti-Ransomware Portal; Recovers Encrypted Data for Free. No More Ransom is a project to help and protect victims of ransomware attacks — Thanks to Intel, Kaspersky, Europol and Dutch Police for the initiative!
IT security giants Intel and Kaspersky with the assistance of Europol and Dutch Police have developed an anti-ransomware portal called ‘No More Ransom’ to help users against the growing threat of ransomware and recover their data for free in order to discourage the trend of paying ransom for decryption of their encrypted data. Fundamentals of Information Security. A TINY BIT about Cryptography. CISSP/CEH/CISA/Hacker and Penetration Testing Specialist. Equation Group: Meet the NSA 'gods of cyber espionage' Over the last couple of years we have been hearing about ever more sophisticated pieces of malware. From Stuxnet and Flame to Gauss and most recently Regin, all have shown increasing levels of technical prowess and all have been linked in some way with the US government.
These were thought to be the pinnacle of a huge investment in offensive cyber capabilities by the world's wealthiest country. That was, until we learned about Equation. Jornalista desafia hackers a destruir sua vida e se arrepende [vídeo] Tor. The Best Hacking Tutorial Sites - Learn Legal Hacking - StumbleUpon. A TINY BIT about Cryptography. Timeline of NSA Domestic Spying. Free and Open Source Cyber Security Learning. The Real Science Behind Cracking Passwords. Top 10 Password Crackers. Top 15 Open Source/Free Security/Hacking Tools.
How To Become A Hacker. Computer emergency response team. International Computer Security Association. ICSA Labs (International Computer Security Association) began as NCSA (National Computer Security Association). Its mission was to increase awareness of the need for computer security and to provide education about various security products and technologies. ICSA Labs. Hack Attack: Turn your $60 router into a $600 router. How do I remove a computer virus? Everything You Wanted to Know about TOR & the Deep Web. Hacking, Security Papers. Crack/Keygen Sites That Are Safe To Use. Google hacking master list.