

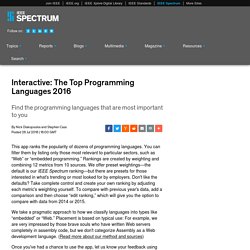
HTML Reference - A free guide to all HTML elements and attributes. Interactive: The Top Programming Languages 2016. This app ranks the popularity of dozens of programming languages.
What is .htaccess? - Apache .htaccess Guide, Tutorials & Examples. Tutorials for Computer Programming Languages. Berkeley Researchers Create Robo-Muscles 1,000 Times Stronger Than Ours. Learn to Build Android Apps with This Curated Collection of Courses. Learn Android App Development. Introduction Smartphones have revolutionised the way we create and consume information.

Today there are apps for everything, from learning programming to searching for recipes and playing games. In addition, an increasingly large number of people around the world are using smartphones as their first computing device, and as a gateway to healthcare and banking services which weren’t available to them otherwise. Android holds nearly an 85% market share of the smartphone market. Android has also made its way into various forms of hardware, from microwaves, washing machines, smart homes and even quad-copters. What will I learn This learning path is a collection of online resources that cover tools and principles for designing and building Android apps. You Can Already Code - You Just Don’t Know It Yet. With zero coding experience, artist building 180 webpages in 180 days. 117 days ago, having never done any programming in her life, Jennifer Dewalt built her first webpage.
JavaScript Modules: A Beginner’s Guide — Free Code Camp — Medium. If you’re a newcomer to JavaScript, jargon like “module bundlers vs. module loaders,” “Webpack vs.

Browserify” and “AMD vs. CommonJS” can quickly become overwhelming. Pencil Code. 10 Simple Coding Tips for Bloggers by @TeacherToolkit. Python. How to get the url parameters using angular js. Ascii code. Foundations of Statistical Natural Language Processing. This is the companion website for the following book.

Chris Manning and Hinrich Schütze, Foundations of Statistical Natural Language Processing, MIT Press. Sorting algorithms. Anybody can learn. CS Fundamentals Unplugged Lessons. Each of these activities can either be used alone or with other computer science lessons on related concepts. 2019-20 CS Fundamentals Curriculum 2019 Course A-F Curriculum Book Course A-F Supply List. Sorting algorithms. Pyp - Python Power at the Prompt. Ls | pyp "p.replace('maybe','yes') | pp.sort() | pp[1:3] |p , p , p.strip('abc') | whitespace | p[3], 'no' | p.upper() " Pyp is a linux command line text manipulation tool similar to awk or sed, but which uses standard python string and list methods as well as custom functions evolved to generate fast results in an intense production environment.

15 Secret Hiding Places That Will Fool Even the Smartest Burglar. Keeping your stuff safe from potential burglars is important.
Whether you have a security system installed in your home or not, there is nothing wrong with a bit of extra protection. Instead of heading out and buying the most expensive safe on the market, you can actually hide your things strategically around the house and burglars will never find them. If you have jewelry, cash or any other valuable that you want to keep extra safe, there are many DIY ways to hide those things from burglars. Incidentally, you can use some of these ideas to hide Christmas gifts from the kids as well. Anatomy of a file format problem – yet another code verification bypass in Android.
Four months ago, the Android platform was stirred, though fortunately not too badly shaken in the end, by a pair of code verification holes.

Simply put, you could add malware to a legitimate app - one from the Play Store, if you liked, complete with icons, branding and reputation - in such a way that Android's digital signature verification would consider it unaltered. From the helpless user's point of view, Google wouldn't just fail to warn about the app possibly being dodgy, it would actively assert that it was the a validated and unaltered item from the original, legitimate vendor. Google, developers, users: everyone lost out except the crooks. How the Kernel Manages Your Memory. What is Docker? A Practical Intro to Data Science — Zipfian Academy - Data Science Bootcamp. Visual Studio Code. Mapping memory between kernel and user space — Linux Kernel Newbies. GCC Command-Line Options. This section describes the options supported by gcc, the driver program of the GNU Compiler Collection, whose C compiler and assembler are used here.
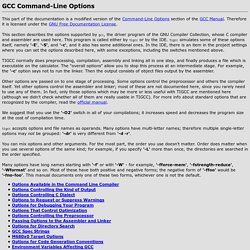
This program is called either by tigcc or by the IDE. tigcc simulates some of these options itself, namely '-E', '-S', and '-c', and it also has some additional ones. In the IDE, there is an item in the project settings where you can set the options described here, with some exceptions, including the switches mentioned above. TIGCC normally does preprocessing, compilation, assembly and linking all in one step, and finally produces a file which is executable on the calculator. The "overall options" allow you to stop this process at an intermediate stage. Synchronization (computer science) Shared Libraries. Shared libraries are libraries that are loaded by programs when they start.

When a shared library is installed properly, all programs that start afterwards automatically use the new shared library. It's actually much more flexible and sophisticated than this, because the approach used by Linux permits you to: update libraries and still support programs that want to use older, non-backward-compatible versions of those libraries;override specific libraries or even specific functions in a library when executing a particular program.do all this while programs are running using existing libraries.
Kernel - How do you empty the buffers and cache on a Linux system? The ulimit parameter. Linux itself has a Max Processes per user limit. System Call Handler. Interactive map of Linux kernel. Linux Technology Reference. LINUX KERNEL INTERNALS: Kernel Space and User Space. Understanding of Kernel space and User space in detail is very important if you wish to have a strong base of Linux Kernel.Here Kernel Space and User Space corresponds to their Virtual address space.Every process in linux utilizes its own separate virtual space.In a linux system based on 32 bit Architecture, user space address space corresponds to lower 3GB of virtual space and kernel space the upper 1GB.
System Call Implementation. System Call Implementation. What is a Device Driver? The HyperNews Linux KHG Discussion Pages. Device Driver Basics. The HyperNews Linux KHG Discussion Pages Device Driver Basics. Linux Device Drivers. The Linux Documentation Project: Guides. How the Kernel Manages Your Memory. The Best Linux Software. Advertisement. Process Descriptor and the Task Structure. Linux List The Open Ports And The Process That Owns Them. What's a good mid-scale cyber security project idea if I'm interested in rootkits, network security, and low level stuff (C/C++)? - Quora. Spoofing Attack: IP, DNS & ARP. Kernel modules. Linux Kernel Modules Wiki. Linux driver for Sentelic touchpad? Ubuntu: Activate multi-touch on Elantech touchpad - Evil Coding Monkey. 12.04 - How do I use a floppy drive in Ubuntu? Dynamic Kernel Module Support. Driver Backports Wiki. Modprobe. DeleteMe. What To Do Before Rooting Your Android.
GB64.COM - C64 Games, Database, Music, Emulation, Frontends, Reviews and Articles. Welcome to the Retrocomputing Archive.