

Why We Hack: The Benefits of Disobedience - Lifehacker. How to gain access to system account the most powerful account in Windows. « Alien Eyes. There is an account in Microsoft Windows that is more powerful than the Administrator account in Windows Operating Systems.

That account is called System account it is similar to the root OR super user in the Linux/Unix world . I will show you how to access this system account in this article. You can use this facility for removing programs that are causing problems to your system, malware etc. Introduction If you look at the task manager (which can be launched by pressing [CTRL]+[ALT]+[DEL]) you will see some processes that are running with System level privileges. System is the highest account in Windows (like root),You can be a super power user by accessing the system account (even while you are logged in as a restricted user) Note: Accessing system account may cause serious problems.
Local system differs from an administrator account in that it has full control of the operating system, similar to root on a Unix machine. Check the name of the account you’ve logged into (Click start. Footholds - Google Hacking Database. Painfully Computer Pranks ~ Computer Hacking.
Computer pranks to freak out your friends and make them crying for mummy I've been posting many articles about computer pranks on this blog (Deadly Virus Prank, The Ultimate Virus, How to Create a Fake and Harmless Virus and Facebook Virus Prank).

Today , I will show you 5 great computer pranks that will frustrate your victims very much. These pranks could be very painfully, so please use them at your own risk ;) 1. Crash a Computer System With Nothing But a URL! I stumbled across this URL while surfing the internet. 2. Know the Trade – Your IT Security Information Portal CISSP/CEH/CISA/Hacker and Penetration Testing Specialist. Google Hacking allintitle:Brains, Corp. camera allintitle:"index of/admin" allintitle:"index of/root" allintitle:restricted filetype:doc site:gov allintitle:restricted filetype :mail allintitle:sensitive filetype:doc allinurl:/bash_history allinurl:winnt/system32/ (get cmd.exe) ext:ini eudora.ini ext:pwd inurl:(service|authors|administrators |users) "# -FrontPage-"

Index of /content/downloads/pdf. PSN Down a Day after Hackers Promise Revenge on Sony. If you were having issues connecting to PlayStation Network or any of Sony’s websites, here’s the reason.

Hacktivist group Anonymous, or a group claiming to them, went through with their earlier promise of exacting revenge on Sony for their treatment of the jailbreak scenario, and their “fellow hackers” GeoHot and Graf_Chokolo. Were they, weren't they? Sony websites were down for a while, as was PSN, but Sony said PSN was down due to undergoing “sporadic maintenance”. It’s funny, because Sony has nearly always informed users about upcoming outages and when they would occur, but strangely did not this time round. Hmm I really can’t, for the life of me, figure out why. Anyway, posted below is the original warning sent out by the hacker group, which can only be called revolutionary pretense.
Hackers' Retribution Tags: Anons, Anonymous, Hackers, Hacking, Jailbreak, PlayStation 3, PlayStation Network, PSN, PSN Down, Sony. Www.hsc.fr/ressources/articles/hakin9_googlehacking/CA-Hakin9-06-2008-googlehacking.pdf. How To Become A Hacker. Copyright © 2001 Eric S.
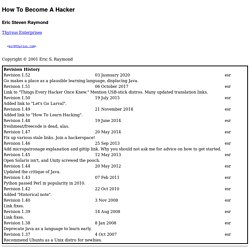
Raymond As editor of the Jargon File and author of a few other well-known documents of similar nature, I often get email requests from enthusiastic network newbies asking (in effect) "how can I learn to be a wizardly hacker? ". Back in 1996 I noticed that there didn't seem to be any other FAQs or web documents that addressed this vital question, so I started this one. A lot of hackers now consider it definitive, and I suppose that means it is. Still, I don't claim to be the exclusive authority on this topic; if you don't like what you read here, write your own. If you are reading a snapshot of this document offline, the current version lives at Note: there is a list of Frequently Asked Questions at the end of this document. Numerous translations of this document are available: ArabicBelorussianBulgarianChinese, Czech. The five-dots-in-nine-squares diagram that decorates this document is called a glider.
If you want to be a hacker, keep reading. 1. 2. 3. 5. 2. 3.