

WiGLE: Wireless Network Mapping. Mimikatz. ArXiv.org e-Print archive. Analyze and identify fake reviews and counterfeits. I2P Anonymous Network. Freenet.
Logiciels libres. Turning a Regular USB Flash Drive into a USB Rubber Ducky – HackMag. Identity Security for the Digital Enterprise. Sign Up. CyFI-Lab-Public/RetroScope: Public release of the RetroScope Android memory forensics framework. OUCH! Suspicious Domains. Background A suggested use of these lists is as input file for Guy's domain sinkhole project.
Thank you to handler Jason Lam for developing this project! This page is still experimental and evolving. We will be adding more data sources over time. If you have any suggestions, please let us know. Lists By Level The lists below categorizes domains as a guide to Low, Medium and High Levels.For our recommended IP block list, please visit The high sensitivity list has fewer false positives down to the low sensitivty list with more false positives.
Domain Allowlist The form below allows you to submit a known-good domain to the suspicious domains allowlist. Search the Lists. Fail2ban. XOXO. Electronics Design & Engineering Courses. First World War 100. Medieval Soldier. Pipe Roll Society. Cyberpunk Now Film Festival — Cyberpunk Now Film Festival. Authentic8 Silo - Overview. The Cisco Umbrella 1 Million top domains - Cisco Umbrella. Here at Cisco Umbrella, we have a culture and passion for giving back to the technical community.
This has included projects such as: our free consumer OpenDNS service, Phishtank, DNSStream, BGPStream, DNSCrypt, and several other data sources. With that, we are very excited to announce the Cisco Umbrella 1 Million — a free list of the top 1 million most popular domains. Top sites. OSINT Feeds from Bambenek Consulting. Master FeedsUse of these feeds governed by this license.NOTE: The license for this data has changed.
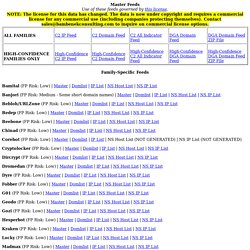
The data is now under copyright and requires a commercial license for any commercial use (including companies protecting themselves). Contact sales@bambenekconsulting.com to inquire on commercial license options. DGA - Netlab OpenData Project. Secure email: ProtonMail is free encrypted email. - advanced password recovery. Download Nessus Vulnerability Assessment. With Advanced Support for Nessus Professional, your teams will have access to phone, Community, and chat support 24 hours a day, 365 days a year.

This advanced level of technical support helps to ensure faster response times and resolution to your questions and issues. Advanced Support Plan Features Phone Support Phone support 24 hours a day, 365 days a year, available for up to ten (10) named support contacts. Chat Support Chat support available to names support contacts, accessible via the Tenable Community is available 24 hours a day, 365 days a year. OpenVAS - OpenVAS - Open Vulnerability Assessment Scanner. Welcome to whateversauce.com. Hack The Box: Hacking Training For The Best.
Welcome to SecurityTube.net. Alobbs/macchanger. Scapy. FIGlet - hosted by PLiG. WiGLE: Wireless Network Mapping. Matrix Video Communications Corp. GalliumOS – A fast and lightweight Linux distro for ChromeOS devices. 2021. CircleCityCon 8.0 – Happy Little Conference. Nolacon. Converge Conference. THOTCON - Chicago's Hacking Conference. RVAsec - The Omni Richmond: November 4-5, 2021. Easterhegg. 2020. LibrePlanet is the annual conference hosted by the Free Software Foundation.

LibrePlanet provides an opportunity for community activists, domain experts, and people seeking solutions for themselves to come together in order to discuss current issues in technology and ethics. Newcomers are always welcome, and LibrePlanet 2020 will feature programming for all ages and experience levels. The theme for LibrePlanet 2020 is "Free the Future". LibrePlanet attendees and speakers will be discussing the hot button issues we've all been reading about every day, and their connection to the free software movement.
How do you fight Facebook? The free software community has continuously demanded that users and developers be permitted to understand, study, and alter the software they use, offering hope and solutions for a free technological future. For each new technological convenience we gain, it seems that we lose even more in the process. ShmooCon – Less Moose Than Ever. 10 Best Packet Sniffers - Comparison and Tips - DNSstuff. It’s no question that bottlenecks, downtime, and other common network performance issues can vastly affect the end-user experience and put productivity on hold, ultimately cutting into your company’s bottom line.
Getting to the root cause of performance problems is a top priority for nearly every sysadmin. This is where packet sniffers, also known as network sniffers or network analyzers, come into play. With the right packet sniffer, you’ll be well-equipped to capture and analyze network traffic, helping you identify the cause of network performance problems and prevent them from recurring. ProcDump - Windows Sysinternals. Defaultnamehere/cookie_crimes: Read local Chrome cookies without root or decrypting. Metasploit-framework/firefox_creds.rb at master · rapid7/metasploit-framework. Fail2ban. JSOFTWARE. Coalition Against Stalkerware. - My journey into learning about Cyber-Security, Ethical Hacking and Networking. %
Sci-Hub: removing barriers in the way of science. The National Archives. National Archives. Home. Library and Archives Canada (LAC) StegFS: a steganographic file system. 1.

Introduction User access control and encryption are standard data protection mechanisms in current file system products, such as the Encrypting File System (EFS) in Microsoft Windows 2000 and XP. These mechanisms enable an administrator to limit user access to a given file or directory, as well as the specific types of actions allowed. However, access control and encryption can be inadequate where highly valuable data is concerned. Specifically, an encrypted file in a directory listing or an encrypted disk volume is itself evidence of the existence of valuable data; this evidence could prompt an attacker to attempt to circumvent the pro-tection or, worse, coerce an authorized user into unlocking it. MX Lookup Tool - Check your DNS MX Records online - MxToolbox. Home. The Best VPN Service Provider with Fast, Secure VPN Access. Google/lyra: A Very Low-Bitrate Codec for Speech Compression.
Learn to think. National Security Agency Central Security Service > About Us > Cryptologic Heritage > National Cryptologic Museum. ICEYE- Your choice for Persistent Monitoring. American Science and Surplus. Business Executives for National Security - Business Executives for National Security. Federation Of American Scientists – Science for a safer, more informed world. Improve Security with Threat Detection - Red Canary. Digital Shadows - Digital Risk Protection.
Videos de Immunity Videos en Vimeo. Untitled. I know it's hard to believe, but we're citizens just like you!! World–Leading AI for Cyber Security. Intelligence, strategy, and security in a dangerous world. DEF CON® Hacking Conference. CircleCityCon 8.0 – Happy Little Conference. Nolacon. THOTCON - Chicago's Hacking Conference. ShmooCon – Less Moose Than Ever. Startseite. SecureWV 12. PhreakNIC 24 – PhreakNIC 24 – November 6-7. Home - GrrCON. Maker Faire Rome - The European Edition. The Chromium Projects. Wget. GNU Wget is a free software package for retrieving files using HTTP, HTTPS, FTP and FTPS, the most widely used Internet protocols.
It is a non-interactive commandline tool, so it may easily be called from scripts, cron jobs, terminals without X-Windows support, etc. GNU Wget has many features to make retrieving large files or mirroring entire web or FTP sites easy, including: Downloading GNU Wget The source code for GNU Wget can be found on the main GNU download server or (better) on a GNU mirror near you. For more download options, see the FAQ. Documentation GNU Wget documentation is available online, as are the manuals of other GNU packages. Additional Information Currently GNU Wget2 is being developed.
Maintainer GNU Wget is currently being maintained by Tim Rühsen, Darshit Shah and Giuseppe Scrivano. Donators We thank the TYPO3 & Magento partner AOE media for donating to the Wget project. SeleniumHQ Browser Automation. .net. Simpler social media tools for authentic engagement. Zello - The Most Reliable Push-to-Talk Walkie Talkie App. HTTP Monitor / HTTP Proxy / HTTPS & SSL Proxy / Reverse Proxy. Mitmproxy - an interactive HTTPS proxy.
Welcome to DialABC. SpiderOak & SpiderOak Mission Systems. Errata Security: How to build your own ProxyHam. "ProxyHam" created controversy because the talk was supposedly suppressed by the US government.
In this post, I'll describe how you can build your own, with off-the-shelf devices, without any code. First, head on over to NewEgg. For a total of $290.96, buy two locoM9 repeaters (for $125.49 each), and two WiFi routers, like the TL-WR700N for $19.99 each. Grab your first WiFi device. Configure it in "client" mode, connecting it to the "Starbucks" SSID.