

Configure DNS Failover with Round Robin : DNS Made Easy. What is round-robin?
For an explanation of the round-robin configuration, please visit our tutorial here. What is DNS Failover? The DNS Failover service from DNS Made Easy is used to keep sites and web services online in the event of system or network issues. This is done by moving DNS traffic to another IP address that you have running at another location. This service can also be used to migrate traffic between redundant internet connections. Ps pcs pps 9.1r6 rest api solutions guide.
Step-by-step instructions on how to install SSL certificates on a Aruba Controller in GUI. The Illustrated TLS Connection: Every Byte Explained.
Microsoft Windows Updates fail to install through ProxySG or Advanced Secure Gateway. The Windows Update application does not like to be proxied.
The application has issues with the proxy's authentication, caching, ICAP services, and SSL interception. The main reasons why Windows Update cannot be cached at this time: Dynamically-created filenames Almost all Windows Updates are downloaded using dynamically-created temporary filenames – the proxy recognizes cache hits based on the requested URI – since this will be different for each client, it cannot determine if the object has been cached or not, therefore a new request is made. The main reason Microsoft does this is because most updates are tailored to the Operating System requesting the file. Jira Core Data Center and Server 8.14. -filter - The Wireshark Network Analyzer 3.4.5. Wireshark-filter - Wireshark display filter syntax and reference wireshark [other options] [ -Y "display filter expression" | b<--display-filter "display filter expression" ]> tshark [other options] [ -Y "display filter expression" ] Wireshark and TShark share a powerful filter engine that helps remove the noise from a packet trace and lets you see only the packets that interest you.
If a packet meets the requirements expressed in your filter, then it is displayed in the list of packets. Display filters let you compare the fields within a protocol against a specific value, compare fields against fields, and check the existence of specified fields or protocols.
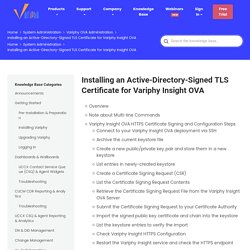
Pycharm. Creating Your Own Sophos UTM Bootable USB Installation Drive. Infoblox. : Qenker 2 Player LED Arcade DIY Parts 2X USB Encoder + 2X Joystick + 20x LED Arcade Buttons for PC, MAME, Raspberry Pi, Windows (Mixed Color Kit): Computers & Accessories. Postman. Solarwinds. Java keytool keystore commands. Java keytool keystore commands. Installing an Active-Directory-Signed TLS Certificate for Variphy Insight OVA – Variphy Cisco CDR Reporting & Call Analytics. OverviewNote about Multi-line CommandsVariphy Insight OVA HTTPS Certificate Signing and Configuration StepsConnect to your Variphy Insight OVA deployment via SSHArchive the current keystore fileCreate a new public/private key pair and store them in a new keystoreList entries in newly-created keystoreCreate a Certificate Signing Request (CSR)List the Certificate Signing Request ContentsRetrieve the Certificate Signing Request File from the Variphy Insight OVA ServerSubmit the Certificate Signing Request to your Certificate AuthorityImport the signed public key certificate and chain into the keystoreList the keystore entries to verify the importCheck Variphy Insight HTTPS ConfigurationRestart the Variphy Insight service and check the HTTPS endpointOptional: Active Directory Root Certificate.
Cloudflare Developer Docs. Magic Transit delivers its connectivity, security, and performance benefits by serving as the “front door” to your IP network.
This means it accepts IP packets destined for your network, processes them, and then outputs them to your origin infrastructure. The Cloudflare network uses Border Gateway Protocol (BGP) to announce your company’s IP address space, extending your network presence globally, and Cloudflare uses Anycast to ingest your traffic. Today, Cloudflare's Anycast edge network spans 193 cities in more than 90 countries around the world. Once packets hit Cloudflare's network, traffic is inspected for attacks, filtered, steered, accelerated, and sent onward to your origin.
AWS. Updox Web Application 2.0 Documentation. Andrew Connell - DIY Home Security System with Konnected.io & SmartThings. Me Home security systems usually mean expensive boxes in an obscure place in your house with a bundle of messy sensor wires hooked up to a circuit board, dumb keypads from the 1980’s and other uninspiring tech.

You know, like what I had in my house? Some monitoring companies have come up with more modern solutions, at a price. ESAP%20Troubleshooting%20Guide. Using jamCommand to Import Pulse Secure Connections. The jamCommand.exe program is a command line program that imports a .pulsepreconfig file into the Pulse client.
The jamCommand program is available for Windows (Vista, Windows 7, and Windows 8) and macOS. A .pulsepreconfig file includes Pulse connection parameters. You can create a .pulsepreconfig file on the Pulse server, and then use it as part of a Pulse installation to ensure that Pulse users have one or more Pulse connections when they start Pulse for the first time. Start and stop services in vCenter Server Appliance (vCSA) 6.5. CaptureFilters. An overview of the capture filter syntax can be found in the User's Guide.
A complete reference can be found in the expression section of the pcap-filter(7) manual page. Wireshark uses the same syntax for capture filters as tcpdump, WinDump, Analyzer, and any other program that uses the libpcap/WinPcap library. A Wireshark capture filter for HTTP 503 errors. Using Wireshark capture filters to track down specific HTTP error codes on a web server.

Wireshark is an excellent tool, and capture filters can be quite daunting, but they can also be very powerful and useful. Recently I was helping to troubleshoot some HTTP 503 error codes which were happening on an couple of IIS servers. These systems were handling over a million requests per day between the two systems, and intermittently responding with 503 errors for a small percentage of requests. It was difficult for us to find any reason for these errors, and unfortunately, IIS does not log 503 errors (as far as we could see) so we could not tell how many were occurring, when they were occurring, or if there were any other associated patterns. We really needed to log the 503 errors, so that we could continue to troubleshoot and perform some configuration optimization. Splash page not showing automatically - The Meraki Community. Hi Jonas You are correct.
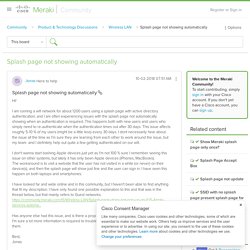
If you manually open a browser and try to browse to a URL that starts with (or a site that only uses - then the AP cannot redirect you to the splash page, because it cannot intercept the traffic. Therefore, it will time out. To reach the splash page, you have to navigate to a site. I understand this is difficult to have users understand and they will typically just try and search Google from their browser, which will also fail as Google use also.
Using PowerShell Behind a Proxy. If you can access the Internet from your computer only via a proxy server, then by default you won’t be able to access external web resources from your PowerShell session: a webpage (Invoke-WebRequest cmdlet), update help using the Update-Help cmdlet, connect to Office365/Azure, or download an application package from an external package repository (using PackageManagement or NanoServerPackage). In this article we’ll show you how to access web from a PowerShell session via a proxy server with the authentication. (122) Building an Intel NUC BDR for the SMB with ShadowProtect. Robocopy. Following the 802.1X AAA process with Packet Captures – Wirelessly WIRED. EDIT: After chatting with David Westcott (@davidwestcott) I have made a few additions to this post. He has graciously asked that I add a little more details including the packet captures so everyone can follow along.
This was a great idea, so please enjoy! 802.1X is typically the first step in one of the more advanced security implementations you will have to dip your toes into when moving your network to a secure state. That being said a lot of times we as engineers get stuck in a state of understanding enough to be dangerous and not enough to be highly successful and more importantly, capable.
I personally learned a lot about dot1x via trial and error through implementations in the past as well as lab time at home and during my CCIE studies. So the question is, how do we become masters of a protocol that is literally quite capable of being the success or demise of a network’s security and operation? …By taking advantage of the resources that are out there as well as practical labs.
Ansible. Create a .pfx/.p12 certificate file using OpenSSL - SSL.com. The PKCS#12 or PFX format is a binary format for storing the server certificate, any intermediate certificates, and the private key into a single encryptable file. PFX files are usually found with the extensions .pfx and .p12. PFX files are typically used on Windows machines to import and export certificates and private keys. Migrating Sites with Site Export Wizard. How to deploy VMware virtual machine from an OVA directly from local datastore.
VMware Knowledge Base. "Telephone activation is no longer supported for your product" error when activating Office. Python. Npcap: Windows Packet Capture Library & Driver.
XMedius. Infoblox. Export lots and lots of fixed addresses and Import... - Infoblox Experts Community. Susan, You can get basic examples from the API documentation for simple tasks with just copy and paste from the API guide. That will get you started without you having to be an experience scripter/programmer. Just look for the SAMPLES section at the bottom of each of the respective areas. You won't have a "bulk" import tool with just the copy/paste but it will get you started on scripting. For what you need though, you can use the CSV import for fixed addresses. The CSV format is documented in the CSV reference manual but I find this to be the easiest way to have a complete view of what you'll want to work with. 802.1x multi authentication vs 802.1x multi domain authentication - 49774.
Hi Scott, m seeing a strange behavior on cc3850 where multi-auth mode also let the hosts (on a port) to participate on both Voice and Data vlan (like multi-domain) Please share your view on this behavior . Logs: switch1#sh run int gigabitEthernet 1/0/3 Building configuration... Microsoft Management Console: "An attempt was made to reference a token that does not exist" Creating an Updox printer. This article is about the process used to install an Updox printer. Microsoft Management Console: "An attempt was made to reference a token that does not exist" Robocopy. WSUS - Move SUSDB.mdf and SUSDB_log.ldf. HowTo: WSUS Cleanup - Shrink a WSUS database (susdb) to almost zero. Using Infoblox DHCP failover - DNS, DHCP, IPAM (IP Address Management) How to set the ProxySG to act as a DNS server for a Client. How to set the ProxySG to act as a DNS server for a Client. How does the DNS resolution work on the ProxySG?
DNS requests sent from a client to the proxy are generally forwarded to the defined DNS server in the ProxySG Network Setup page. Solved: DHCP - Difference between IPV4 Fixed Address and I... - Infoblox Experts Community. Hello Mayur, vNIOS for VMware 7.2 Install Guide. Mg sg ccs uc 1. FreePBX 13 Setup Guide. Topics tagged under "jareds guide to freepbx 13" How to Set Traffic Bandwidth Limits. UTM: How to create a VLAN Interface. Ethernet VLAN interfaces are often used on internal, managed networks, that are segmented into VLANS. Sophos UTM: How to create a VLAN Interface.
Presence icon missing in Outlook 2013 and 2016. Hi all, How to Make a Factory Recovery Partition to Protect Windows System? Export an NPS Server Configuration for Import on Another Server. Mancunian sayings: our guide to common words and phrases. We had more than 600 responses via Facebook and Twitter - here's a selection of them: Let us know any we've missed either in the comments or via Twitter and Facebook. Words 1. iPad / iPhone Certificate Issuance. Hey all, Rob here again. Connecting iPads to an Enterprise Wireless 802.1x Network Using Certificates and Network Device Enrollment Services (NDES) – Windows PKI blog.
Find which DC a computer is authenticated to - Windows Server. How To Expand Your Virtual Machine's Storage Capacity. How to install Active Directory Users and Computers in Windows Server 2012 - Windows Server 2012 R2. Export an NPS Server Configuration for Import on Another Server. Routing and Filtering Network Traffic. How to fix ‘Antimalware Service Executable’ high CPU usage. Export an NPS Server Configuration for Import on Another Server. Find your Installed SQL Server Versions and Instances. Tcpdump command. 12 Tcpdump Commands - A Network Sniffer Tool. Convert a Sonicwall Config file to a "readable" text file. How Do I Configure Health Check Monitors on NetScaler? Hardening WordPress. 10 point wp hardening checklist plain2. Complete List of Default WordPress Files. Customize Support Portals - GoToAssist Remote Support - LogMeIn.
Pimoroni Picade Cabinet Kit [PIM105] ID: 2706 - $239.95. USB Stick Install Solved - Hardware, Installation, Up2Date, Licensing - Sophos UTM 9. UTM Tweaking Guide 2.0 - General Discussion - Sophos UTM 9. An exercise in frustration: Setting up Web Filtering on Sophos UTM – Drashna's Demesne. Wireshark: Determining a SMB and NTLM version in a Windows environment. You receive a "The User Profile Service failed the logon” error message. GameWizard. Super Easy RetroPie Gaming Install w/ 3000+ Games!!! The micro retro gaming console. Your recalbox / Vos recalbox. Eligible Expenses HSA & FSA - SelectAccount. HowTo: WSUS Cleanup - Shrink a WSUS database (susdb) to almost zero - 3aIT Ltd.