

Divide and Conquer: Cracking MS-CHAPv2 with a 100% success rate. Divide and Conquer: Cracking MS-CHAPv2 with a 100% success rateJul 29, 2012 At Defcon 20 last weekend, David Hulton and I gave a presentation on cracking MS-CHAPv2.

This blog post is meant to be a rough overview of what we covered in our talk. Why MS-CHAPv2? HTML Templates. News or Magazine This template puts a focus on bold images, perfect for a magazine style site with eye catching content.
Your stories are easy to find with large feature blocks. See Demo Real Estate or Travel Big thumbnails with a space for captions and descriptions along with an informative header make this the perfect template for real estate or hotel booking. Training, Videos, Tools, Resources, Learning. Hacking n cracking. Web Application Vulnerability Scanner. Advanced password recovery. John the Ripper password cracker. John the Ripper is free and Open Source software, distributed primarily in source code form.
If you would rather use a commercial product tailored for your specific operating system, please consider John the Ripper Pro, which is distributed primarily in the form of "native" packages for the target operating systems and in general is meant to be easier to install and use while delivering optimal performance. This version integrates lots of contributed patches adding GPU support (OpenCL and CUDA), support for a hundred of additional hash and cipher types (including popular ones such as NTLM, raw MD5, etc., and even things such as encrypted OpenSSH private keys, ZIP and RAR archives, PDF files, etc.), as well as some optimizations and features. Unfortunately, its overall quality is lower than the official version's. Penetration Testing Tools and How2s. Talend Data Preparation for Analytics: Self-Service Data Prep Tools.
DataCracker - Plans, features and pricing. Free Features include: Analyze up to 100 responses per survey All results are based on the first 100 responses; enough for a small survey.
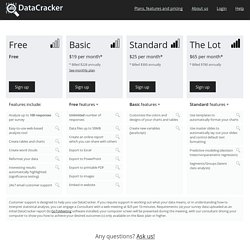
Easy-to-use web-based analysis tool Office-like interface and work flow.Works in your web browser. Create tables and charts Create tables, crosstabs, column charts, bar charts, pie charts, grid of bars charts, line charts, snake charts, dot charts, stacked column/bar charts, stacked column/bar charts with negatives, mosaic charts, trend charts, scatter charts, bubble charts, quantized scatter charts and histograms. Create word clouds Create a word cloud to visualize open-ended text.Modify the interactive word cloud - combine, split, rename or hide words. Weka – Graphical User Interference Way To Learn Machine Learning. In this era of data science where R and Python are ruling the roost, let’s take a look at another data science tool called Weka.
Weka has been around for quite a while and was developed internally at University of Waikato for research purpose. What makes Weka worthy of try is the easy learning curve. For someone who hasn’t coded for a while, Weka with its GUI provides easiest transition into the world of Data Science. Being written in Java, those with Java experience can call the library into their code as well. Personally, I had my first shot at Data Science when I took a course at University of Waikato. 18 Free Exploratory Data Analysis Tools For People who don't code so well.
Introduction Some of these tools are even better than programming (R, Python, SAS) tools.

All of us are born with special talents. It’s just a matter of time until we discover it and start believing in ourselves. We all have limitations, but should we stop there? No. IT-Tools. Pen Testing and Hacker-Do. Mad-Hatting Blacks. Hacker9 - Social media, Hacking & Security. Wireshark Display Filters. Top 50 Hacking Tools That You Must Have. Whether you are a Penetration tester, a hacker or an aspiring newbie trying to learn Cyber Security, you must have a nice catalogue of tools to make your life easier.

While these tools do make working simpler but cannot compensate for the vast amount of knowledge required in this field. In this post i’m going to mention 50 different tools under 9 categories that your ‘Hack Lab’ must have. Hack a Day — Fresh hacks every day. Top 15 Open Source/Free Security/Hacking Tools. 1.

Nmap Nmap (“Network Mapper”) is a free and open source (license) utility for network discovery and security auditing. Nmap uses raw IP packets in novel ways to determine what hosts are available on the network, what services (application name and version) those hosts are offering, what operating systems (and OS versions) they are running, what type of packet filters/firewalls are in use, and dozens of other characteristics.