

TiddlyWiki. A standard edit dialog on a tiddler TiddlyWiki is an open-source single page application wiki.
A single HTML file contains CSS, JavaScript, and the content. The content is divided into a series of components, or Tiddlers. Natural Area Code. The Natural Area Code (or Universal Address) is a proprietary geocode system for identifying an area anywhere on the Earth, or a volume of space anywhere around the Earth.
The use of thirty alphanumeric characters instead of only ten digits makes a NAC shorter than its numerical latitude/longitude equivalent. §Two-dimensional system[edit] Instead of numerical longitudes and latitudes, a grid with 30 rows and 30 columns - each cell denoted by the numbers 0-9 and the twenty consonants of the Latin alphabet - is laid over the flattened globe. A NAC cell (or block) can be subdivided repeatedly into smaller NAC grids to yield an arbitrarily small area, subject to the ±1 m limitations of the World Geodetic System (WGS) data of 1984. A NAC represents an area on the earth—the longer the NAC, the smaller the area (and thereby, location) represented. Future Transportation Technology Will Blow Your Mind.
The web performance & security company. RANDOM.ORG - Manual Signature Verification. <p style="background-color:#ffff90;padding: 0em .5em 0em .5em;font-size:.9em"><strong>Warning:</strong> Your browser does not support JavaScript – RANDOM.ORG may not work as expected</p> RANDOM.ORG's API can digitally sign random data for you, such that it can be proved to originate from our service.
The signature format is specified in PKCS #1 v2.0. You can use our API to verify the signature, but it is also possible to do it yourself. This page explains how to perform signature verification without using the RANDOM.ORG API. Working with Math. First things first.
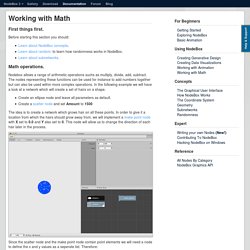
Before starting this section you should: Math operations. Cargomatic plays the role of hero, swooping in to help unclog America’s largest ports. By Michael Carney On March 6, 2015 Southern California ports typically handle 40 percent of all US container imports, and yet, for much of the last year, that flow of imported goods has slowed to barely a trickle.

A protracted labor dispute between Pacific Maritime Association and the International Longshore and Warehouse Union has left critical goods sitting on ships in the harbor waiting to be offloaded or, often more frustratingly, piled in container stacks across the port waiting to be unloaded and cleared of customs. The Union workers signed a tentative contract in late February, but that agreement only marked the beginning of what will surely be a months long process of digging out from under the massive container backlog. Plus.google. How To Automate Excel Using Perl for Win32. Developers familiar with using Perl can take advantage of the Automation capabilities in Perl for Win32 to integrate with applications such as Microsoft Office.
This article gives you some example Perl code that sends data to Microsoft Excel and then creates a Chart and PivotTable. Before executing any Perl scripts, you need to have Perl installed and configured on your machine. Because Perl is freely distributed, anyone can provide an implementation of Perl for Win32. Two commonly used ported versions are provided by ActiveState, formerly ActiveWare, and Mortice Kern System (MKS). This example uses ActiveState's Perl for Win32. Follow the steps below to create and run the sample: Ruling the world with Perl and Excel. Mailinator(tm) Blog: Mailinator launches Private Domains. Get your own (very) private Mailinator !

Mailinator.com If you weren't aware, Mailinator has always allowed you to point any domain you own to the Mailinator SMTP servers (i.e. the MX record). The Mailinator email system accepts any and all email sent to it and happily delivers it to the designated inbox. For example, if you own "yourdomain.com", point the MX record to mail.mailinator.com and send email to joe123@yourdomain.com - that email will end up in the "joe" inbox at You don't even have to sign-up with Mailinator to do all that - just point your domain! Neat, huh? Email sent to Mailinator this way however follows the same fate as any other email in the public system. CloudCorner - Your Geolocated Cloud Storage. Lorem Ipsum - All the facts - Lipsum generator. Lorem Ipsum (lipsum) generator, in Perl, using lipsum.com.
PsychSim_Shell. Big Bang, la théorie qui pourrait tout changer : ce ne serait pas l’origine de l’univers. C'est une idée qui fait son bonhomme de chemin dans la communauté scientifique : le Big Bang ne serait pas le commencement de tout.

Autrement dit, contrairement au modèle standard actuel il est possible que l'Univers ait existé de toute éternité. Aurélien Barrau est professeur à l’Université Joseph Fourier, membre de l’Institut Universitaire de France et chercheur au Laboratoire de Physique Subatomique et de Cosmologie du CNRS. Energy salt water. Water wheel pump. Rife River Pump. 21 Products For Coffee Lovers That Will Blow Your Caffeine-Loaded Mind. Edmund Horner's projects, opinions, and other nerdy stuff. Malcolm Gladwell's David And Goliath. Jill Hutchison/Flickr Malcolm Gladwell seems to think attending an elite college or working for a famous company could kill your dreams.
The popular author lays out his argument for being a big fish in a little pond in his latest book, "David and Goliath," a work that aims to overturn conventional notions about what makes for a disadvantage and who should be considered an underdog. Gladwell's basically against anyone attending a famous university just for the name, or really doing anything for the sake of prestige. To choose something elite is, more often than not, to choose being a little fish in a big pond, he says, since only a select few will shine among the best. Éducation bienveillante. Puzzle: Fast Bit Counting. Devise a fast algorithm for computing the number of 1-bits in an unsigned integer.

If the machine supports n-bit integers, can we compute the number of 1-bits in O(log n) machine instructions? Can we compute the number of 1-bits in O(b) machine instructions where b is the number of 1-bits in the integer? Source: Commonly asked in job interviews for Software Engineers. I first heard it in 1996 when I was a graduate student. Solution: This article presents six solutions to this problem. Iterated Count runs in time proportional to the total number of bits. Sparse Ones runs in time proportional to the number of 1 bits. Dense Ones runs in time proportional to the number of 0 bits. IBM 'Watson' Wins: 'Jeopardy' Computer Beats Ken Kennings, Brad Rutter. (SETH BORENSTEIN and JORDAN ROBERTSON, AP) Machines first out-calculated us in simple math.
Then they replaced us on the assembly lines, explored places we couldn't get to, even beat our champions at chess. Swarm intelligence. Swarm intelligence (SI) is the collective behavior of decentralized, self-organized systems, natural or artificial. The concept is employed in work on artificial intelligence. The expression was introduced by Gerardo Beni and Jing Wang in 1989, in the context of cellular robotic systems.[1] The application of swarm principles to robots is called swarm robotics, while 'swarm intelligence' refers to the more general set of algorithms. Main Page - BaseX Documentation. Turn Your Dropbox Account Into a WebDAV Server With DropDAV. DropDAV is a nifty service that enables you to use Dropbox with WebDAV clients.
It was developed to work with the iWork suite for the iPad, but it will work with any WebDAV client, so you could also use it to sync OmniFocus through your Dropbox account, for example. It’s simple to set up, although you do need to provide it with your Dropbox username and password to get going. Once set up, you connect to with your WebDAV client and log in using your Dropbox credentials. How to use WebDAV in Pages, Keynote, or Numbers with Dropbox.
Amazon CEO Jeff Bezos wants to ship goods using unmanned aircraft. Some are skeptical, others nervous, but drones already are improving the way we live. Davfs. DAVfs is a Linux file system driver that allows you to mount a WebDAV server as a disk drive. WebDAV is an extension to HTTP/1.1 that allows remote collaborative authoring of Web resources, defined in RFC 4918. Installing DAVfs Install davfs2 from official repositories. Mounting the partition. DeCasteljau Algorithm. Hamburg (Germany), the 19th September 1999. Written by Nils Pipenbrinck aka Submissive/Cubic & $eeN Introduction I learned a nice way to calculate bezier-curves a couple of weeks ago. This algorithm is that nice and easy to understand. So if you ever had problems remembering the basis-matrix of bezier curves don't worry... after this article you'll never need it again. Machine learning.
Elastic map. Heuristics. A*’s ability to vary its behavior based on the heuristic and cost functions can be very useful in a game. Pinguin Software. Hands-on: Tempo brings its super-smart calendaring to iPad. Tempo, a powerful calendar app for the iPhone, goes beyond just displaying events and dates, instead pulling together multiple calendars and contextual data to serve as a digital assistant. It’s a productivity powerhouse on the iPhone, but until now has been missing from the iPad.
This is finally being rectified, as starting on Thursday Tempo is available as a universal app. Expanding the Science and Practice of Gratitude. For too long, we’ve taken gratitude for granted. Yes, “thank you” is an essential, everyday part of family dinners, trips to the store, business deals, and political negotiations. Custom Login Experiences: Credential Providers in Windows Vista. New information has been added to this article since publication.
Refer to the Editor's Update below. COCOMO. The Constructive Cost Model (COCOMO) is an algorithmic software cost estimation model developed by Barry W. Boehm. Jason Savard - The Green Programmer. About. What is Lua? Lua is a powerful, efficient, lightweight, embeddable scripting language. It supports procedural programming, object-oriented programming, functional programming, data-driven programming, and data description. Lua combines simple procedural syntax with powerful data description constructs based on associative arrays and extensible semantics. Lua is dynamically typed, runs by interpreting bytecode with a register-based virtual machine, and has automatic memory management with incremental garbage collection, making it ideal for configuration, scripting, and rapid prototyping. Simply the Best Free VPN. HOWTO. Introduction OpenVPN is a full-featured SSL VPN which implements OSI layer 2 or 3 secure network extension using the industry standard SSL/TLS protocol, supports flexible client authentication methods based on certificates, smart cards, and/or username/password credentials, and allows user or group-specific access control policies using firewall rules applied to the VPN virtual interface.
Lnternet_Securlty_Prlvacy. Android - Security Concerns for Keyboard input. Best Free Onscreen Keyboard for Security. Making Windows Usable. New IT Farmer. OTPW – a one-time password login package. OTPW – a one-time password login package. Overview of Moonshot Components - Moonshot - Moonshot Wiki. Introduction to Moonshot - Moonshot - Moonshot Wiki. How It Works. Crypt. Misc/OPIEandSKey - IetfngPub. RFC 4226 - HOTP: An HMAC-Based One-Time Password Algorithm.
RFC 2289 - A One-Time Password System. Multi-factor authentication. Hard, Soft, or Smart? Evaluating the Two-Factor Authentication Options - Infosecurity Magazine. AuthLite: Affordable Two-factor Authentication for Windows Active Directory. Classless Inter-Domain Routing. Malware FAQ: Reverse WWW Tunnel Backdoor. OpenSSH: Reuse existing connections / Reverse tunnel. Apps. Silent Circle. The Zfone Project - Getting Started with Zfone. Labs - BitTorrent Chat. ChatSecure: Private Messaging. Experts Find a Door Ajar in an Internet Security Method Thought Safe. Send Private Info That Self-Destructs. The Ultimate IFTTT Guide: Use The Web's Most Powerful Tool Like A Pro. Turning Gmail into Google Reader. How to Get Gmail Notifications in Your RSS Feed Reader. How To Use NTFS Alternate Data Streams. Turn Any Browser Window Into a Quick-Edit Notepad. How to Create RSS Feeds for Twitter - Video Tutorial.
Drive storage. Rss - Create a feed of someone's facebook wall. The Official YAML Web Site. Typinator - the fastest text expander in town. The Hacker's Keyboard will become one of your top 10 Android apps. Tokyo Cabinet: a modern implementation of DBM. Eprd. Application Bridging for Federated Access Beyond web (abfab) - Documents. A better PROMPT for CMD.EXE or Cool Prompt Environment Variables and a nice transparent multi-prompt. Camera - QR code (2D barcode) coding and decoding algorithms? DropboxPortableAHK - Portable Dropbox App. Free preview thumbnails on your site. Web page screenshot image. Pinboard: social bookmarking for introverts. Utilities: Time Converter. Receive SMS Online.
Receive SMS Online for FREE. Receive SMS Online For Free - US,UK,Austria,Sweden,BELGIUM Free Virtual Numbers. Free US/UK/Sweden/AU/Norway Virtual Numbers. QMixFA9B2C. Mscgen: A Message Sequence Chart Renderer.