

Learn ethical hacking with the Pay What You Want White Hat Hacker Bundle. Stay Connected with Us!

Follow TechnoBuffalo. Learn how to code. Google Search Operators. The following table lists the search operators that work with each Google search service.

Click on an operator to jump to its description — or, to read about all of the operators, simply scroll down and read all of this page. The following is an alphabetical list of the search operators. This list includes operators that are not officially supported by Google and not listed in Google’s online help. Each entry typically includes the syntax, the capabilities, and an example. Rosetta Code. Regular Expressions. Python. Software - Regular Expressions. One class of objects that some object oriented programming languages support is called Regular Expressions.
These are basically patterns that can be used for string manipulation. The typical syntax for a regular expression involves placing the pattern code between slashes with optional characters after the trailing slash. A trailing i indicates that case should be ignored when processing the pattern and g indicates that the pattern should be processed global instead of stopping at the first occurrence, gi would indicate that the pattern should be processed globally ignoring case.
The supported methods will depend on the programming language but a regular expression class will probably support the following methods and possibly many more: 80+ Best Free Hacking Tutorials. Learning to become hacker is not as easy as learning to become a software developer. I realized this when I started looking for learning resources for simple hacking people do. Even to start doing the simplest hack on own, a hacker requires to have in depth knowledge of multiple topics. Windows PowerShell Scripting. PowerShell Tutorials. PowerShell Tutorial for beginners.
Windows PowerShell instruction thought-out for those new to PowerShell. In the next few weeks I will be posting a series of PowerShell basics that will provide a good start for a solid foundation. Here is what I have slated: The Windows PowerShell Console – Configuration and Customization.PowerShell Basics - Cmdlets, Parameters, Command Types, Command Information, etc…Output using the PowerShell Format command.Engaging the Windows File System.WMI and .NET primer (real basic)Variables in PowerShellTaking what you have learned and applying it.
Cheat Sheet : All Cheat Sheets in one page. Mozilla Firefox Start Page. Hacking News. Metasploit Unleashed - Mastering the Framework. Quick Tips for Network Security Manager. Malware. International_strategy_for_cyberspace.pdf (application/pdf Object) HowTo: Find switchport of a MAC Address on Cisco Catalyst Switch. If you have a big network with multiple Access Switches connecting to the core switches or routers then tracing a device like a PC or a laptop for troubleshooting or security purposes is one of those tasks that you often end up doing.
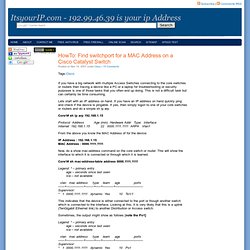
This is not a difficult task but can certainly be time consuming. Lets start with an IP address on hand. If you have an IP address on hand quickly ping and check if the device is pingable. If yes, then simply logon to one of your core switches or routers and do a simple sh ip arp Core1# sh ip arp 192.168.1.15 Protocol Address Age (min) Hardware Addr Type Interface Internet 192.168.1.15 22 0000.1111.1111 ARPA Vlan1 From the above you know the MAC Address of for the device: IP Address : 192.168.1.15 MAC Address : 0000.1111.1111 Now, do a show mac-address command on the core switch or router.
Core1# sh mac-address-table address 0000.1111.1111. NIST.gov - Computer Security Division - Computer Security Resource Center. CC Blog: Recommendations to vendors for communicating product security information. I-Hacked.com Taking Advantage Of Technology. Malware Removal Guide for Windows. Analyzing Teredo Traffic Using Wireshark. Internet Crime Schemes. Auction Fraud Auction fraud involves fraud attributable to the misrepresentation of a product advertised for sale through an Internet auction site or the non-delivery of products purchased through an Internet auction site.
Consumers are strongly cautioned against entering into Internet transactions with subjects exhibiting the following behavior: The seller posts the auction as if he resides in the United States, then responds to victims with a congratulatory email stating he is outside the United States for business reasons, family emergency, etc. National Vulnerability Database Home. National Vulnerability Database CVSS Scoring. This page shows the components of the CVSS score for example and allows you to refine the CVSS base score.
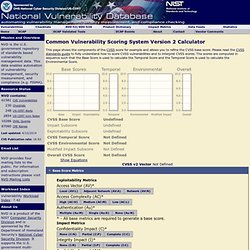
Please read the CVSS standards guide to fully understand how to score CVSS vulnerabilities and to interpret CVSS scores. The scores are computed in sequence such that the Base Score is used to calculate the Temporal Score and the Temporal Score is used to calculate the Environmental Score. Alert: Environmental Modified Impact CVSS Base Score. How To Become A Hacker. Copyright © 2001 Eric S.
Raymond As editor of the Jargon File and author of a few other well-known documents of similar nature, I often get email requests from enthusiastic network newbies asking (in effect) "how can I learn to be a wizardly hacker? ". Back in 1996 I noticed that there didn't seem to be any other FAQs or web documents that addressed this vital question, so I started this one. Krobar's Collection of Cracking Tutorials. Tips to Keep your Online Accounts Safe and Secure. You probably use strong and unique passwords do protect your accounts safe but is that enough?

This page provides a security checklist and tips to keep your online accounts safe and secure. You probably use strong and unique passwords to prevent hackers from taking over your online accounts but is that enough? Five of the best encryption tools. Equipping your PC with a firewall and antivirus tool may keep out most hackers, but doesn't guarantee your security.

If someone gets physical access to your system (it's stolen, say, or a computer repair technician is snooping around) then the best internet security suite will be no use at all, and there's only one way to ensure you're protected: encryption. Here are five free tools to encrypt your data to ensure they can't be accessed by hackers, no matter where they're stored. Comodo Disk Encryption 1.2 Comodo Disk Encryption not only allows you to create a virtual encrypted drive that will hold your most confidential files but also lets users encrypt an entire partition of their hard drive. Blocking Unwanted Parasites with a Hosts File. What it does ... You can use a modified HOSTS file to block ads, banners, 3rd party Cookies, 3rd party page counters, web bugs, and even most hijackers and possibly unwanted programs.
This is accomplished by blocking the connection(s) that supplies these little gems. The Hosts file is loaded into memory (cache) at startup, so there is no need to turn on, adjust or change any settings with the exception of the DNS Client service (see below). How to be a Programmer: A Short, Comprehensive, and Personal Summary. Debugging is the cornerstone of being a programmer. The first meaning of the verb to debug is to remove errors, but the meaning that really matters is to see into the execution of a program by examining it. A programmer that cannot debug effectively is blind. Idealists that think design, or analysis, or complexity theory, or whatnot, are more fundamental are not working programmers. The working programmer does not live in an ideal world. Even if you are perfect, your are surrounded by and must interact with code written by major software companies, organizations like GNU, and your colleagues.
Python Programming Language – Official Website. Ethical Hacking, Penetration Testing & Computer Security. CSIRT, Computer Security Incident Response Team. State Guard Association of the United States. Infosec Island. FCC's Ten Key Cybersecurity Tips for Businesses. Broadband and information technology are powerful factors in small businesses reaching new markets and increasing productivity and efficiency. However, businesses need cybersecurity tools and tactics to protect themselves, their customers, and their data from growing cyber threats. Here are ten key cybersecurity tips for businesses to protect themselves: 1. Train employees in security principles Establish basic security practices to protect sensitive business information and communicate them to all employees on a regular basis.
Establish rules of behavior describing how to handle and protect customer information and other vital data. Hacking the WPA Airwaves. It is interesting how many people believe that their wireless is secure because they are using WPA. Well we did a test recently and were able to basically password guess our way with a dictionary attack using either a straight dictionary or a rainbow table. The cool thing is I bought an ALFA USB antenna and could sit down at the corner coffee place and still see my wireless access point. Information Security Policies and Procedures Part 1. Information Security Policies and Procedures Part 2. Information Security Policies and Procedures Part 3. Information Security Policies and Procedures Part 4. Information Security Policies and Procedures Part 5. CISSP Reloaded Domain Three: Telecoms and Network Security. Emergency Management Institute - FEMA Independent Study Program. Emergency Management Institute.
Emergency Management Institute. Course Date *This course has been reviewed for doctrine related changes and therefore is dated October 31, 2013.