

ViewDNS.info - Your one source for DNS related tools! Email Trace - Trace Email and find out who is the email owner. Email address header trace. Time.is. Disposable Email. Free online network utilities - traceroute, nslookup, automatic whois lookup, ping, finger. Online Ping, Traceroute, DNS lookup, WHOIS, Port check, Reverse lookup, Proxy checker, Mail relaying, Bandwidth meter, Network calculator, Network mask calculator, Country by IP, Unit converter.
MonitoringForge: Network Management Software. Online traceroute from 4 locations @ Just-traceroute.com. Create and Collaborate on Online Diagrams - Try it Free. Speedtest.net - The Global Broadband Speed Test. C Link Checker. Identify any Language from Text. Download Test Files. These files are provided to help users test their download speeds from our servers.

You can also run a speed test however downloading files may be useful if you want to do so from different tools. Please be aware that downloading these files will count towards your download usage allowances imposed by your broadband provider and the large files may use up a large proportion of this if you only have a small allowance (1GB - 3GB for example). We suggest only testing the large files if you have a connection speed faster than 10 Mbps. Click the file you want to download to start the download process. If the download does not start you may have to right click on the size and select "Save Target As”. NOTE: We provide these download files primarily for UK broadband users; although we do not prohibit their use by others, we do not allow scripted/automated download of these files.
Very Large File (1GB) Learn Who is Hosting Any Website. Quick Check - Pingability.com. Who is Hosting southafrica. Bandwidth Meter. Open Ports Tool. Remote Address Port Number Check a port's status by entering an address and port number above.
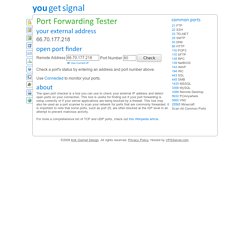
The open port checker is a tool you can use to check your external IP address and detect open ports on your connection. This tool is useful for finding out if your port forwarding is setup correctly or if your server applications are being blocked by a firewall. This tool may also be used as a port scanner to scan your network for ports that are commonly forwarded. For more a comprehensive list of TCP and UDP ports, check out this Wikipedia article. If you are looking for a software solution to help you configure port forwarding on your network, try using this powerful Port Forwarding Wizard. IPtect.com - What is my IP address? Show my IP address. Find my IP address. IP trace locate.
Email Blacklist Check - See if your server is blacklisted. 15 Online Tools That You Will Come To Love As A Tech. I have compiled a list of 15 free online tools that will help you greatly as a tech.

I’m sure that there are other good ones that I have left out so please feel free to post the ones that you like as well. IPTools offers a wide variety of online networking tools. The Scrutinizer - 283 Tools in One Place. Real time spam black lists (RBL) Network Calculators. Us: see the sites - viewing culture. Ip Tools, DNS tools, internet tools, WHOIS, traceroute, ping, domain name tools. Accurate time for all time zones. DNS Stuff: DNS tools, DNS hosting tests, WHOIS, traceroute, ping, and other network and domain name tools.
Blummy - The bookmarklet management bookmarklet. Home Page - free tools for power surfing. Clipmarks. InternetFrog.com: Network Tools, Internet Speed Test and Website Tools. Absolutely Del.icio.us - Complete Tool Collection. Browser Toolbars Online Privacy - Toolbar Removal Tool. The risk with website monitoring is that it's possible for query strings to be monitored and retransmitted.

Query strings are data strings following the '? ' delimiter in urls often used by webform submissions and search engines. Query strings may contain sensitive information such as credit card numbers, passwords, names, addresses, hotel/flight reservation details and other personally identifiable information which an unethical browser extension could monitor and retransmit to its home server or a third party. Firewalls won't block browser extensions because they're integrated into the web browser. Browser toolbars can sometimes be removed by using the Windows Add/Remove Programs utility or by running the toolbar's uninstaller which should be packaged with it. Before removing an adware toolbar you may like to take notes and screenshots of the companies being advertised in its links, search listings or pop-up ads.
Home. Site Language Translation. IP Calculator / IP Subnetting. Ipcalc takes an IP address and netmask and calculates the resulting broadcast, network, Cisco wildcard mask, and host range.
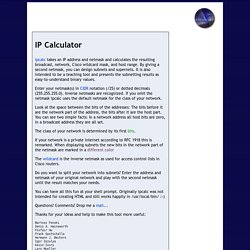
By giving a second netmask, you can design subnets and supernets. It is also intended to be a teaching tool and presents the subnetting results as easy-to-understand binary values. Enter your netmask(s) in CIDR notation (/25) or dotted decimals (255.255.255.0). Inverse netmasks are recognized. If you omit the netmask ipcalc uses the default netmask for the class of your network. Look at the space between the bits of the addresses: The bits before it are the network part of the address, the bits after it are the host part.