


How to View Passwords Hidden Under Asterisks [Video] Google Chrome, Firefox and other browsers hide passwords behind asterisks but you can easily view the saved passwords using the built-in developer tools. Web browser hide passwords under asterisk characters for improved security. Say you are on the Gmail login page and the web browser, as always, has auto-filled the username and passwords fields for you.
Online Visual Traceroute Map Data Map data ©2017 Google, INEGI Map Satellite Download Test Files These files are provided to help users test their download speeds from our servers. You can also run a speed test however downloading files may be useful if you want to do so from different tools. Please be aware that downloading these files will count towards your download usage allowances imposed by your broadband provider and the large files may use up a large proportion of this if you only have a small allowance (1GB - 3GB for example).
tools:ipv4_route_servers [BGP4.net] IPv4 Route Servers, listed by ASN. (An IPv6 Route Servers page is also available.) If you know of a working IPv4 route server that isn't listed below, feel free to add it. Open Ports Tool Remote Address Port Number Check a port's status by entering an address and port number above. Linux Commando: Splitting up is easy for a PDF file Occasionally, I needed to extract some pages from a multi-page pdf document. Suppose you have a 6-page pdf document named myoldfile.pdf. You want to extract into a new pdf file mynewfile.pdf containing only pages 1 and 2, 4 and 5 from myoldfile.pdf. I did exactly that using pdktk, a command-line tool. If pdftk is not already installed, install it like this on a Debian or Ubuntu-based computer. $ sudo apt-get update $ sudo apt-get install pdftk
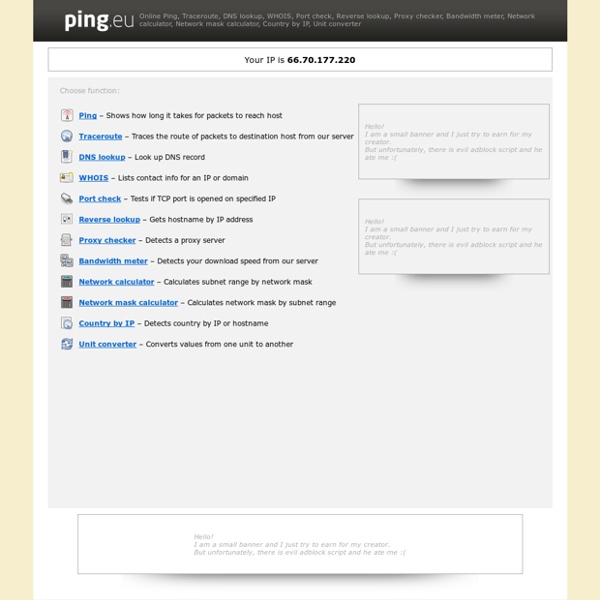
15 Online Tools That You Will Come To Love As A Tech I have compiled a list of 15 free online tools that will help you greatly as a tech. I’m sure that there are other good ones that I have left out so please feel free to post the ones that you like as well. IPTools offers a wide variety of online networking tools. With this site you can look up IP address information, check spam databases, run pings, run traceroutes, lookup WHOIS information and much more.
How to Identify the Cookies Your Site Installs in Browsers How do I know which cookies are installed by my website? To properly inform users about cookies that your site installs in their browsers, you must learn to identify them. This is not an easy task, so we have created a brief guide to help you with it. 1 – Browser extensions The identification of cookies installed on your website may end up being a result from the combined use of different tools, the main and most commonly used are Wappalyzer and BuiltWith, both are available as add-ons to all the most widely used browsers and allow a thorough analysis of all the resources and technologies implemented within a website. They do not only disclose cookies installed on a site, but also list all the technologies used on that site, such as server infrastructure, the CMS used and other specific information.
How to Verify if an Email Address Is Real or Fake How do you verify if a given email address is real or fake? The obvious solution is that you send a test mail to that email address and if your message doesn’t bounce, it is safe to assume* that the address is real. [*] Some web domains may have configured a catch-all email address meaning that messages addressed to a non-existent mailbox will not be returned to the sender but in most cases, such email messages will bounce. Browser Toolbars Online Privacy - Toolbar Removal Tool The risk with website monitoring is that it's possible for query strings to be monitored and retransmitted. Query strings are data strings following the '?' delimiter in urls often used by webform submissions and search engines. Query strings may contain sensitive information such as credit card numbers, passwords, names, addresses, hotel/flight reservation details and other personally identifiable information which an unethical browser extension could monitor and retransmit to its home server or a third party. Firewalls won't block browser extensions because they're integrated into the web browser. Browser toolbars can sometimes be removed by using the Windows Add/Remove Programs utility or by running the toolbar's uninstaller which should be packaged with it.
Screaming Frog SEO Spider Tool & Crawler Software About The Tool The Screaming Frog SEO Spider is a fast and advanced SEO site audit tool. It can be used to crawl both small and very large websites, where manually checking every page would be extremely labour intensive, and where you can easily miss a redirect, meta refresh or duplicate page issue. IP Calculator / IP Subnetting ipcalc takes an IP address and netmask and calculates the resulting broadcast, network, Cisco wildcard mask, and host range. By giving a second netmask, you can design subnets and supernets. It is also intended to be a teaching tool and presents the subnetting results as easy-to-understand binary values. Enter your netmask(s) in CIDR notation (/25) or dotted decimals (255.255.255.0). Inverse netmasks are recognized. If you omit the netmask ipcalc uses the default netmask for the class of your network.
25, 465, 587... What port should I use? It's a common question that we receive here at Mailgun. To ensure connectivity to our Simple Mail Transfer Protocol (SMTP) endpoint, Mailgun offers multiple port options, but which one should you use? Let's first take a historical look at each port and then we'll discuss today's methodology for usage. If you're not a history buff, go to "Todays Usage".