

Web Design and Development. What are all the whole numbers between 1 and 10000. We come from the future. The Tesseract. Non-Euclidean Geometry. Introduction to Algorithms - Download free content from MIT. Dual Tessellation. Dave's short course in trigonometry. Table of Contents Who should take this course?

Trigonometry for you Your background How to learn trigonometry Applications of trigonometry Astronomy and geography Engineering and physics Mathematics and its applications What is trigonometry? Trigonometry as computational geometry Angle measurement and tables Background on geometry The Pythagorean theorem An explanation of the Pythagorean theorem Similar triangles Angle measurement The concept of angle Radians and arc length Exercises, hints, and answers About digits of accuracy Chords What is a chord? Matrix (mathematics) Each element of a matrix is often denoted by a variable with two subscripts.
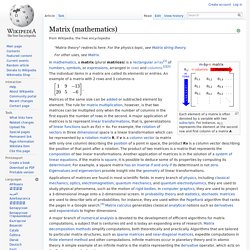
For instance, a2,1 represents the element at the second row and first column of a matrix A. Applications of matrices are found in most scientific fields. In every branch of physics, including classical mechanics, optics, electromagnetism, quantum mechanics, and quantum electrodynamics, they are used to study physical phenomena, such as the motion of rigid bodies.
In computer graphics, they are used to project a 3-dimensional image onto a 2-dimensional screen. In probability theory and statistics, stochastic matrices are used to describe sets of probabilities; for instance, they are used within the PageRank algorithm that ranks the pages in a Google search.[4] Matrix calculus generalizes classical analytical notions such as derivatives and exponentials to higher dimensions. The numbers, symbols or expressions in the matrix are called its entries or its elements. Lorenz Butterfly. Maze Generator. List of mathematical symbols. When reading the list, it is important to recognize that a mathematical concept is independent of the symbol chosen to represent it.
For many of the symbols below, the symbol is usually synonymous with the corresponding concept (ultimately an arbitrary choice made as a result of the cumulative history of mathematics), but in some situations a different convention may be used. For example, depending on context, the triple bar "≡" may represent congruence or a definition. Further, in mathematical logic, numerical equality is sometimes represented by "≡" instead of "=", with the latter representing equality of well-formed formulas. In short, convention dictates the meaning. Each symbol is shown both in HTML, whose display depends on the browser's access to an appropriate font installed on the particular device, and in TeX, as an image.
Guide[edit] This list is organized by symbol type and is intended to facilitate finding an unfamiliar symbol by its visual appearance. Basic symbols[edit] Non-Euclidean geometry. Version for printing In about 300 BC Euclid wrote The Elements, a book which was to become one of the most famous books ever written.
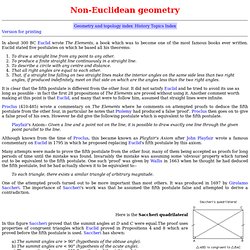
Euclid stated five postulates on which he based all his theorems: To draw a straight line from any point to any other. Philosophy of Mathematics. First published Tue Sep 25, 2007; substantive revision Wed May 2, 2012 If mathematics is regarded as a science, then the philosophy of mathematics can be regarded as a branch of the philosophy of science, next to disciplines such as the philosophy of physics and the philosophy of biology.
However, because of its subject matter, the philosophy of mathematics occupies a special place in the philosophy of science. Whereas the natural sciences investigate entities that are located in space in time, it is not at all obvious that this also the case of the objects that are studied in mathematics. MIT Video Course - StumbleUpon.
Www.maa.org/devlin/LockhartsLament.pdf. Non-Euclidean geometry. Behavior of lines with a common perpendicular in each of the three types of geometry In mathematics, non-Euclidean geometry consists of two geometries based on axioms closely related to those specifying Euclidean geometry.
As Euclidean geometry lies at the intersection of metric geometry and affine geometry, non-Euclidean geometry arises when either the metric requirement is relaxed, or the parallel postulate is set aside. In the latter case one obtains hyperbolic geometry and elliptic geometry, the traditional non-Euclidean geometries. When the metric requirement is relaxed, then there are affine planes associated with the planar algebras which give rise to kinematic geometries that have also been called non-Euclidean geometry. Another way to describe the differences between these geometries is to consider two straight lines indefinitely extended in a two-dimensional plane that are both perpendicular to a third line: History[edit] Early history[edit] Terminology[edit]
Relplot: equation plotter. Relplot constructs high-resolution PostScript or PDF plots of the solutions to equations on two variables.
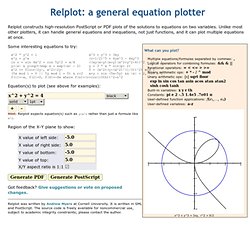
Unlike most other plotters, it can handle general equations and inequations, not just functions, and it can plot multiple equations at once. What can you plot? Multiple equations/formulas separated by commas: ,Logical operators for combining formulas: && & ||Relational operators: = < <= > >=Binary arithmetic ops: + * - / ^ modUnary arithmetic ops: |x| sqrt floor exp ln sin cos tan asin acos atan atan2 sinh cosh tanhBuilt-in variables: x y r thConstants: pi e 2 -.5 1.4e5 .7e01 πUser-defined function applications: f(e1,..., en)User-defined variables: a-z x^3 + y^3 = 3xy, r^2 = 9/2 Some interesting equations to try: Got feedback? Relplot was written by Andrew Myers at Cornell University. Cryptographers chosen to duke it out in final fight - physics-math - 13 December 2010. A competition to find a replacement for one of the gold-standard computer security algorithms used in almost all secure, online transactions just heated up.

The list of possibilities for Secure Hash Algorithm-3, or SHA-3, has been narrowed down to five finalists. They now face the onslaught of an international community of "cryptanalysts" – who will analyse the algorithms for weaknesses – before just one is due to be selected as the winner in 2012. The competition, which is being run by the US National Institute of Standards and Technology in Gaithersburg, Maryland, is a huge deal for cryptographers and cryptanalysts alike.
"These are incredibly competitive people. La difficile ascension vers la résolution d'un problème mathématique.