

NOTE: I have put a duplicate of the Pearldrop "Life Hacks: Institute of Hacking" into my Pearldrop "Lifehacks" because it has alot more "life hack" info than "tech hack" info.
OSINT Framework. How To Set Up A Wireless Router. Want to set up your wireless router, but don’t know where to start?

You’re not alone. The assortment of cables, ports, and other components stashed in your router leaves most people scratching their heads. Every router is different, and the specific steps for setting them up depend on your model. In most cases, the easiest thing to do is to follow the instructions that come with the device. But if you can’t find those instructions, or just don’t understand them, these general steps should help.
How to Reveal Passwords (Asterisks) in Browsers. How to Test Your Internet Speed [Easy, Under 5 Minutes] Security and hacking. Security and hacking. Practically Networked Troubleshooting Guides. Wireless network troubleshooting: Connectivity problems. When you have trouble connecting a wireless client (a desktop, laptop, PDA, or phone) to an office network, these step-by-step debugging tips can help with your wireless network connectivity problems.

Windows 7 and Vista Network Problems. Windows 7, Windows 8 and Vista laptops may have problems with "Unidentified Networks" and broken network connections.
This article discusses the solution, mainly by disabling IPV6. Download DNS Benchmark (DNSBench) Manufacturer’s Description GRC's DNS Benchmark performs a detailed analysis and comparison of the operational performance and reliability of any set of up to 200 DNS nameservers (sometimes also called resolvers) at once.
When the Benchmark is started in its default configuration, it identifies all DNS nameservers the user's system is currently configured to use and adds them to its built-in list of publicly available “alternative” nameservers. Each DNS nameserver in the benchmark list is carefully “characterized” to determine its suitability — to you — for your use as a DNS resolver. This characterization includes testing each nameserver for its “redirection” behavior: whether it returns an error for a bad domain request, or redirects a user's web browser to a commercial marketing-oriented page.
Cannot connect to primary dns server. Microsoft Windows [Version 6.0.6002] Copyright (c) 2006 Microsoft Corporation.

All rights reserved. C:\Users\Derek>ipconfig/all Windows IP Configuration Host Name . . . . . . . . . . . . : Derek-PC Primary Dns Suffix . . . . . . . : Node Type . . . . . . . . . . . . : Broadcast IP Routing Enabled. . . . . . . . : No WINS Proxy Enabled. . . . . . . . : No Ethernet adapter Local Area Connection 2: DNS server not responding error fix. This is a complete guide on fixing DNS Server isn’t Responding error.
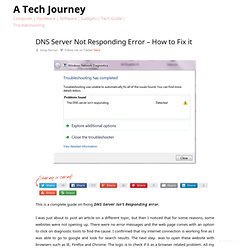
I was just about to post an article on a different topic, but then I noticed that for some reasons, some websites were not opening up. There were no error messages and the web page comes with an option to click on diagnostic tools to find the cause. I confirmed that my internet connection is working fine as I was able to go to google and look for search results. The next step was to open these website with browsers such as IE, Firefox and Chrome. The logic is to check if it as a browser related problem. Try this step if you still have the same problem.
Network tests and diagnostics. April 2014 Testing the IP configuration Before doing anything else, you are advised to check the computer's IP configuration.
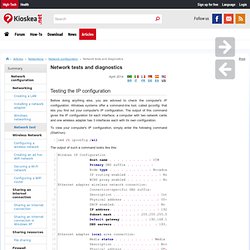
Windows systems offer a command-line tool, called ipconfig, that lets you find out your computer's IP configuration. The output of this command gives the IP configuration for each interface; a computer with two network cards and one wireless adapter has 3 interfaces each with its own configuration. To view your computer's IP configuration, simply enter the following command (Start/run): What is ping. Ping is a basic Internet program that allows a user to verify that a particular IP address exists and can accept requests.

Ping is used diagnostically to ensure that a host computer the user is trying to reach is actually operating. Ping works by sending an Internet Control Message Protocol (ICMP) Echo Request to a specified interface on the network and waiting for a reply. Ping can be used for troubleshooting to test connectivity and determine response time. As a verb, ping means "to get the attention of" or "to check for the presence of" another party online. The computer acronym (for Packet Internet or Inter-Network Groper) was contrived to match the submariners' term for the sound of a returned sonar pulse.
This was last updated in February 2009. Computer Networking Tips. Check Your WiFi Connection – Who is Using Your Internet Connection? Troubleshooting Connectivity Problems on Windows Networks (Part 1) If you would like to read other parts to this article please go to: If you would like to be notified when Brien M.

Posey releases the next part of this article series please sign up to the WindowsNetworking.com Real time article update newsletter. Today’s network hardware and software is more reliable than ever but even so, things do occasionally go wrong. In this article series, I am going to discuss some troubleshooting techniques that you can use when a host on your Windows network has trouble communicating with other network hosts. For the sake of those with less experience in working with the TCP/IP protocol, I’m going to start with the basics, and then work toward the more advanced techniques.
Using ping command for troubleshooting Windows network connectivity. Using ping command for troubleshooting networks will help narrow down the causes of your Windows PC connectivity problems.
The introduction to this TCP/IP diagnostic utility will give you an understanding and syntax of how ping works, plus what it means when your ping request times out or reaches a network host. Diagnose issues from the command line (CL) prompt window and learn how to verify network connections in this tip, originally seen on WindowsNetworking.com. Today's network hardware and software are more reliable than ever; but even so, things do occasionally go wrong. Best tricks for speeding up your Wi-Fi router. A sluggish wireless network is frustrating. It's no fun when an exciting movie suddenly starts buffering or an important Internet video call breaks up. A few years ago, families didn't put much demand on routers. All they did was browse the Web and read email. The average home had one or two PCs. Today, a family might have several computers, a wireless printer, a game console, a streaming video gadget and a variety of smartphones and tablets. Hack by asrinet oldream. FAQ. What You Need to Know About the Java Exploit.
On Thursday, the world learned that attackers were breaking into computers using a previously undocumented security hole in Java, a program that is installed on hundreds of millions of computers worldwide. This post aims to answer some of the most frequently asked questions about the vulnerability, and to outline simple steps that users can take to protect themselves. Update, Jan. 13, 8:14 p.m. ET: Oracle just released a patch to fix this vulnerability. Read more here. Q: What is Java, anyway? Q: So what is all the fuss about? Q: Yikes. Q: How do I know if I have Java installed, and if so, which version? Either way, it’s important not to get too hung up on which versions are affected, as this could become a moving target.
Q: A site I use often requires the Java plugin to be enabled. Q: I am using a Mac, so I should be okay, right? Q: I don’t browse random sites or visit dodgy porn sites, so I shouldn’t have to worry about this, correct? Secure Your Wireless Router In The Short Term By Assigning It An Aggressive Name. As more devices ship with wireless networking capabilities, it becomes increasingly important to have routers that are capable of handling connections from hardware such as tablets, laptops and mobile phones. The problem is that many routers still in use are perfectly good pieces of hardware, except for one drawback – they don’t support Wireless-N or offer advanced encryption such as WPA. With the threat of drive-by Wi-Fi theft and the risk of secure data being transferred over a non-secure connection, wireless routers without the most current security options can be temporarily shored up with just a bit of imagination. Meanwhile, there are ways in which you can get hold of modern routers for free and connect to them using low-cost USB devices.
Wireless Tips – Does Your Wireless Router Keep Disconnecting or Dropping the Connection? I’ve had a Netgear wireless router for about a year now and it’s been pretty good until a couple of weeks back all of sudden my wireless connection kept dropping or I could not connect to the router unless I restarted the router! It was a royal pain in the butt, but because I’m lazy I didn’t get around to fixing it earlier! If you’re in the same situation, here’s what you can do to fix the problem! The issue is usually caused by one of two things: the driver for your wireless card or the firmware version on your router (basically the driver for the router). I have found that unless you’re using a really old wireless router, it’s more than likely an old driver for your wireless card that is the culprit.
How to Crack a Wi-Fi Network's WPA Password with Reaver. How to Crack a Wi-Fi Network's WEP Password with BackTrack. Hacking. Network ,Hack,tools sites. Life Hacks: Institute of Hacking. TCP/IP Overview and History. TCP/IP Overview and History(Page 1 of 3) The best place to start looking at TCP/IP is probably the name itself. TCP/IP in fact consists of dozens of different protocols, but only a few are the “main” protocols that define the core operation of the suite. Of these key protocols, two are usually considered the most important. The Internet Protocol (IP) is the primary OSI network layer (layer three) protocol that provides addressing, datagram routing and other functions in an internetwork.
The Transmission Control Protocol (TCP) is the primary transport layer (layer four) protocol, and is responsible for connection establishment and management and reliable data transport between software processes on devices. Due to the importance of these two protocols, their abbreviations have come to represent the entire suite: “TCP/IP”.
As I said earlier, the Internet is a primary reason why TCP/IP is what it is today. Home - Table Of Contents - Contact Us. The TCP/IP Guide. The TCP/IP Guide Welcome to the free online version of The TCP/IP Guide! How to Find Your Computer’s Private & Public IP Addresses. Ipconfig - Windows Command Line Utility. IP Addresses - Working With My IP Addresses. Working w/ IP Addresses & Subnets. IP addresses are the fundamental method for computers to identify themselves on the Internet and many other computer networks. SecTools.Org Top Network Security Tools. Network Monitoring Tools.
Les Cottrell, SLAC. Last Update: December 14, 2015 ESnet | ESCC | PinGER Internet monitoring | Tutorial This is a list of tools used for Network (both LAN and WAN) Monitoring tools and where to find out more about them. Probably the Best Free Security List in the World. Security List Index. Hack by asrinet oldream. How to Hack: Ethical Hacking and Cyber Security.