

Shodan. Privacy for anyone anywhere. Push The Limits. Elite Proxy Switcher - Professional Proxy Software. Toutes les astuces de Chine-Astuces. Download Android app and Windows client. Uncensored Internet access for Windows and Mobile. Super Free PPTP VPN Accounts. 100% Free PPTP and OpenVPN Service. Free PPTP VPN $0/mo PPTP (point to point tunneling) is widely used since it is supported across all Microsoft Windows, Linux, Apple, Mobile and PS3 platforms.
Media Hint. ASTALAVISTA. hacking tool & serial. Hide IP and Anonymous Web Browsing Software. Home. How to delete yourself from the Internet. The Internet companies that power your online life know that data equals money, and they're becoming bolder about using that data to track you.

If they get their way, your every online step would be not only irrevocable, but traceable back to you. Fortunately, there are some positive steps you can take to reclaim your online history for yourself. The online privacy software company Abine, which makes Do Not Track Plus, also offers a service called DeleteMe, which removes your data from numerous tracking sites and keeps it from coming back.
In an unusual gesture, though, they've made public how to do for yourself everything that DeleteMe does. Here's my take on their advice. Be warned, though. Should I Change My Password? Download History Viewer for free. Serials & keys - unlocks the world. Proxy Lists. List of Free Proxy Servers - Page 1 of 10.
Proxy 4 Free - Free Proxy Servers - Protect Your Online Privacy with Our Proxy List. KPROXY - Free Anonymous Web Proxy - Anonymous Proxy. ChrisPC Free Anonymous Proxy Software FREE Download - Enjoy your privacy and surf anonymously online and watch TV abroad USA, UK, Hulu, TV.com, iPlayer - Chris P.C. srl. ChrisPC Anonymous Proxy Pro is the privacy tool that anybody would need to use to protect their online experience.

Browsing, buying online, watching online TV channels or reading online newspapers are part of our daily life. What is important to know is that when we connect to the Internet we are exposed, our buying/browsing habits and our confidential data are at risk. Of course there are several means and levels of security you can take online, like the ones you have for your home: you have a door lock, you have even a dog barking and you may have also a security system, surveillance system and so on. Every person needs a different level of protection for his/her privacy. Therefore you are in charge with deciding the level of protection you need. Download - SoftEther VPN Project.
Dtunnel.com will protect your anonymity on the internet, helping. Download - I2P. Dependency Java Runtime 1.6 or higher.
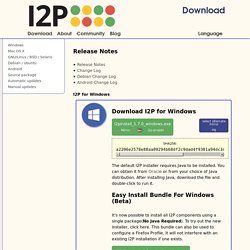
(Oracle Java Version 7, OpenJDK 7, or IcedTea7 recommended, except Raspberry Pi: JDK 8 for ARM, PowerPC: IBM SDK 7) Determine your installed Java version here or type java -version at your command prompt. Clean installs 186bbe30a37802b6201fe129516e2d9515925cfc60e2f68645eb6413ec172953 Download that file and run it. 5b2a1e23273e1d76a071142adc58b836ed300e2c1f2fd80d330ac61632fab173 Download that file and double-click it (if that works) or type java -jar i2pinstall_0.9.16.jar in a terminal to run the installer. 100% Free PPTP and OpenVPN Service. TunnelBear. Best Free Anonymous Surfing Services. This is the 21st century, the so-called Digital Age, an age where information is more public than it is private.

The sheer growth and pervasiveness of the Internet have led to additional concerns over privacy issues for a great number of people. As we are entitled to our privacy in the physical world, why not so in the virtual one too? There are a lot of genuine reasons for why many persons wish to stay anonymous on the Internet, reasons ranging from simple precaution over personal issues, to more extreme behavior such as hiding browsing activities from a spouse and averting coercive authority.
We are not here to debate the legal, moral or ethical issues surrounding anonymity on the Internet, but merely to provide you with reviews of several methods available for you to achieve it. VPN Gratuit et Communautaire. VPN Gratuit. Comparatif VPN gratuit Vous êtes nombreux à vouloir découvrir ou utiliser un VPN mais de façon gratuite.

La liste proposée ci-dessous vous présentent des VPN gratuits avec ou sans aucune limitation de données, avec ou sans restrictions d’ usage (vitesse, VOIP, P2P, port de connexion pour le FTP, ….). Les meilleurs VPN gratuits sont ceux qui ont un forfait Premium (sans limitation d’ usage) comme SecurityKiss. Delivering the net. Public-Proxy-Server ... Ein guter Weg, seine Surfspuren im Internet zu verschleiern, sind die so genannten anonymen Proxy-Server.

Ist ein solcher anonymer Proxy-Server zwischen Ihren Rechner und die von Ihnen besuchte Homepage geschaltet, kann vom Betreiber der Homepage nur die IP-Adresse des Proxys festgestellt werden, nicht aber Ihre eigene. Umgekehrt kann nur der Weg von Ihrem PC zum Proxy-Server nachvollzogen werden, aber nicht das eigentliche Ziel. Tor Browser Bundle. Download the file above, and save it somewhere, then double click on it. (1) Click "Run" then choose the installer's language and click OK (2).
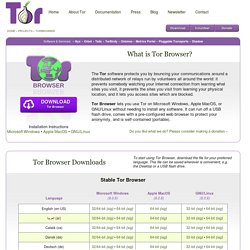
Make sure you have at least 80MB of free disk space in the location you select. If you want to leave the bundle on the computer, saving it to the Desktop is a good choice. If you want to move it to a different computer or limit the traces you leave behind, save it to a USB disk. Click Install (3) Wait until the installer finishes. This may take a few minutes to complete. Once the installation is complete, click Finish to launch Tor Browser's wizard. Best Free Anonymous Surfing Services. Read this article in Spanish (Español) Introduction This is the 21st century, the so-called Digital Age, an age where information is more public than it is private.

The sheer growth and pervasiveness of the Internet have led to additional concerns over privacy issues for a great number of people. Spotflux – Le petit VPN qui monte, qui monte… Best SSTP Free VPN Account - VPN Account - Free SSTP VPN. Free VPN Software: Virtual Networking with LogMeIn Hamachi. Centralized Software Deployment Save yourself onsite visits.

Quickly and easily dispatch virtual network client software to new computers remotely. Simply send end users a link to download and install the client to participate in a specific virtual network. Manage and Restore Networks Handle your virtual networks virtually. Manage and restore virtual networks for end-users with the click of a mouse, from anywhere via the web. Client Configuration Management Configure settings for individual networks and clients.
Set default settings for individual networks and clients, with support for full, restricted and minimal client interface modes. Up to 256 clients per LogMeIn ID. Centralized Access Controls. UK TV Proxy - Fast Proxy Browser. List of Free Proxy Servers - Page 1 of 14. Fake Identity Generator. Free File Sharing - Minus.com. Free large file hosting. Send big files the easy way! Internet Privacy & Security. Locks (Mainly Picking Them) Freedom Toolbox. How To Find Unprotected Website Directories & Get “Interesting” Files. Advertisement With all the risks involved in using file sharing networks, browsing unprotected website directories is probably a lot easier and safer. Only when you start doing that do you realise half the stuff that people keep in their website folders (Sports Illustrated magazines!)
Top 5 Websites To Learn How To Hack Like A Pro. You might be surprised to learn just how many people want to learn how to hack. The stereotype is that of the young college guy – a computer science major for sure – who spends his evenings and weekends writing up intricate hacking scripts to break into whatever computer system he can get his hands on. The truth is that what was once a male-dominated community is fast changing into one that includes folks – men and women – from many walks of life, from many countries and with many backgrounds. A recent CNET article about DEFCON makes note of the fact that claims of sexual harassment and unwanted advances are increasing. This isn’t because hackers are getting more obnoxious or offensive, but because more female hackers are entering into the community and trying to find a home there, only to find insulting behavior, and other actions unbecoming of a gentleman.
There’s a caveat that I have to share before diving into these sites. Search Engine. Startpage offers you Web search results from Google in complete privacy! When you search with Startpage, we remove all identifying information from your query and submit it anonymously to Google ourselves. We get the results and return them to you in total privacy. Your IP address is never recorded, your visit is not logged, and no tracking cookies are placed on your browser. When it comes to protecting your privacy, Startpage runs the tightest ship on the Internet. Spam-free search. Scr.ım. Ultrasurf - Free Proxy-Based Internet Privacy and Security Tools.
Unblock The Internet! Unblock favorite site. Free web proxy – unblock any website – webproxy.net. Media Hint. JonDonym.