

Go Deep. Aircrack-ng. Description Aircrack-ng is an 802.11 WEP and WPA/WPA2-PSK key cracking program.
Aircrack-ng can recover the WEP key once enough encrypted packets have been captured with airodump-ng. This part of the aircrack-ng suite determines the WEP key using two fundamental methods. The first method is via the PTW approach (Pyshkin, Tews, Weinmann). Have I been pwned? API v2. Overview You're reading about v2 of the API which is presently the current version and returns a significant amount of additional data over v1.
You can still access the documentation for v1 which continues to be available in the form it was originally released in. Index. BREWER'S DICTIONARY OF PHRASE & FABLE. A Brief History of Hacking 1980s - ppt SearchFileType. TheShipsList: Passengers, Ships, Shipwrecks. A-Z List of Country and Other Area Pages. RootsLinks. SecurityFocus. Public Proxy Servers - Free Proxy Server List. The Denied Persons List. Access denied. Infoplease: Encyclopedia, Almanac, Atlas, Biographies, Dictionary, Thesaurus. Free online reference, research & homework help.
NARA - AAD - List of Series - Genealogy/ Personal History: Passenger Lists. List of countries of the world in alphabetical order. What is decision support system (DSS)? - Definition from WhatIs.com. A decision support system (DSS) is a computer program application that analyzes business data and presents it so that users can make business decisions more easily.
It is an "informational application" (to distinguish it from an "operational application" that collects the data in the course of normal business operation).Typical information that a decision support application might gather and present would be: By submitting your email address, you agree to receive emails regarding relevant topic offers from TechTarget and its partners. You can withdraw your consent at any time. Contact TechTarget at 275 Grove Street, Newton, MA. CVE List Main Page HTML Quick List. Socks proxy list: buy socks list, free and anonymous socks proxy servers, socks4 socks5 proxy for free, US socks.
PBL. The Spamhaus PBL is a DNSBL database of end-user IP address ranges which should not be delivering unauthenticated SMTP email to any Internet mail server except those provided for specifically by an ISP for that customer's use.

The PBL helps networks enforce their Acceptable Use Policy for dynamic and non-MTA customer IP ranges. PBL IP address ranges are added and maintained by each network participating in the PBL project, working in conjunction with the Spamhaus PBL team, to help apply their outbound email policies. Additional IP address ranges are added and maintained by the Spamhaus PBL Team, particularly for networks which are not participating themselves (either because the ISP/block owner does not know about, is proving difficult to contact, or because of language difficulties), and where spam received from those ranges, rDNS and server patterns are consistent with end-user IP space which typically contain high concentrations of "botnet zombies", a major source of spam.
Bing. Google. DuckDuckGo. Ixquick Search Engine. iZito. Lycos.com. ZapMeta - All Web Results, One Engine. Meta Searches. iBoogie - MetaSearch Document Clustering Engine and Personalized Search Engines Directory. Practical Tools for Dynamic Search Suggestions. Iboogie.com. What IP addresses does iboogie.com use?
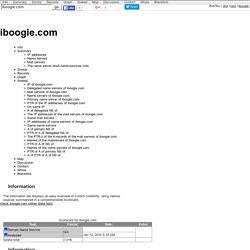
Iboogie.com uses the IP address 64.28.108.56 hosted by Onramp Access Inc ONR in Austin TX United States, which also a5.iboogie.com, *.iboogie.com, 6461796c6967687477696e64796a616e6540686f746d616message.iboogie.com and about twenty other use. Which name servers does iboogie.com use? The five name servers dns1.name-services.com, dns2.name-services.com, dns3.name-services.com, dns4.name-services.com and dns5.name-services.com , hereafter referred to as "name server group 1", which also janmalcom.com, listsociety.com, wargunz.com and more than two hundred other use. Universal Meta Search and Discovery Engine. Dogpile Web Search. Search engine and human edited web directory KartOO. New generation metasearch engine and web portal. 1874onondaga. Iboogie.biz and www.iboogie.biz information. Domain-kb.com iboogie.biz General information iboogie.biz has been registered on 11/02/2013.
The main IP address of iboogie.biz is 184.168.221.23 (Note : www.iboogie.biz may be hosted on a different IP address). Find all domains with IP address 184.168.221.23. IPalyzer. Docs Archive - is a convenient place for downloading free pdf, doc, xls, ppt or rtf documents. Access denied. Glossaries by Subject. Online whois network utility: get domain registration information. Internet Archive: Digital Library of Free Books, Movies, Music & Wayback Machine. Random featured wallpapers. Self Publishing Basics: How to Read an ISBN. Some years ago, I published a book that landed on the front page of the Sunday New York Times Book Review, which was quite a thrill for my wife and me, as we were running our publishing company from a spare bedroom in our house.
Soon enough, the phone started to ring, and one call was from a distributor in New York. “Hey, we’re all wondering down here, is this some guy publishing from his dining room? Data mining-MeltData.com.