

David
Recipes. ICE-CREAM. Networks. Evernote. Work together in Evernote with Work Chat. Evernote has always been the place where your most productive work happens.
Now, you can also share, chat, and collaborate with others without ever having to leave your workspace to send an email or jump to another app. Meet Work Chat, a new way to share and discuss the things you’re working on in Evernote with the people who’ll help you get them done. Chat to work together efficiently Click or tap on the Work Chat icon to launch a new chat and bring the right people into the conversation—even if they don’t use Evernote yet.
You can chat with as many people or as few people as you need to get the job done. Sharing made simple Work Chat gives all of your conversations focus around the work you’re doing in shared notebook and, for the first time, editable single notes. Scannable: A New Mobile Scanning App from Evernote. Given how much the modern workflow relies on mobile devices, mobile scanning needs to be better.

Mobile document scanning doesn’t happen in a vacuum — one way or another it’s part of a larger process in your life that a scanning app should speed up, not slow down. Done well, a great scanning app should emphasize action, not archiving. It should be about the words on the paper, not the paper itself. Get Scannable from the App Store, free >> How to Email Content Into Evernote. What will you accomplish in 2015?
Throughout January, we’ll share our favorite Evernote tips, shortcuts, and tricks to make the most of your Evernote experience. Perfect for powering productivity, whether you work for yourself or on a team. How to Use Tags to Organize Evernote. The power of Evernote is that there is no right or wrong way to use it.
From audio notes to websites, it’s the perfect place to capture and store the content you need to be productive. The question we get from many users is how to organize the material they bring into Evernote. From notebooks to tags, you have the option to decide your own personal classification system. That taxonomy can be as simple or complex as you need, but it’s remarkable how powerful Evernote becomes when you find the right system that works. Yesterday, we discovered a post on Medium that provides a clear example of how one user has successfully structured his Evernote account to help make the most impact in his work with an emphasis on tags.
Thomas Honeyman is a student at the University of Southern California and co-founder of a music collaboration platform. Much like author Michael Hyatt, tags have become the engine that helps power the organizational success with how Thomas manages content in Evernote. 1. 10 Tricks to Make Yourself an Evernote Master. Devops. Free cloud storage |& online backup. Screencast, tutorial & webinar tools. _Br0wser. Back Pain. Online Guide to Practical Privacy Tools. How to Avoid Identity Theft. Secure Digital. Secure Digital (SD) is a nonvolatile memory card used extensively in portable devices, such as mobile phones, digital cameras, GPS navigation devices, handheld consoles, and tablet computers.
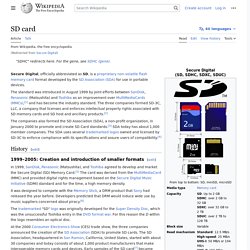
The Secure Digital standard was introduced in August 1999 as an evolutionary improvement over MultiMediaCards (MMC). The Secure Digital standard is maintained by the SD Association (SDA). SD technologies have been implemented in more than 400 brands across dozens of product categories and more than 8,000 models.[1] The Secure Digital format includes four card families available in three different form factors. The four families are the original Standard-Capacity (SDSC), the High-Capacity (SDHC), the eXtended-Capacity (SDXC), and the SDIO, which combines input/output functions with data storage.[2][3][4] The three form factors are the original size, the mini size, and the micro size. Overview[edit] SD[edit] SDHC[edit] SDXC[edit] Ghostzilla - the invisible browser. Three steps to properly protect your personal data.
With groups like Anonymous actively looking to embarrass your company, laptops thefts occurring every second, and the recent poor US District Court ruling on fifth amendment password protection rights, it is time you actually encrypt your data properly.

Your Windows login password is not encrypting your computer (surprise!). Full-disk encryption (used by very few people) is a good step, but by itself it still will not completely protect your data from prying eyes, overzealous governments, or your own mistake of leaving your company's crown jewels at the local coffee shop. More in the Investigator's Toolkit:
Telegram Messenger for iPhone and Android. Google tracks you. We don't. An illustrated guide. Find Your Own Private Internet With Freenet. PC World – by Alex Wawro Anonymous peer-to-peer communication on the Internet isn’t just a handy tool for privacy enthusiasts; it’s critical for preserving free speech in the digital world.
Anonymous file-sharing services like BitTorrent are legion, but their utility is limited—you can share only files—and their reputations are unfairly tarnished by people who use them to share media illegally. If you’re looking for a highly anonymous peer-to-peer network with websites, forums, and more, look no farther than the Free Network, one of the best-kept secrets in anonymous communication. Here’s how it works: Freenet is an anonymous peer-to-peer data-sharing network similar to BitTorrent, but with one key difference: All uploaded data is assigned a unique key, sliced up into small, encrypted chunks and scattered across different computers on the network.
Next, head over to the Freenet Project website, and download the Freenet client for your operating system. Passwords: Why "This Is Fun" Is 10x Safer Than "J4fS!2" DeleteMe. Hacker Attack Tools. Top 75 Network Security Tools. Monitoring. Monitoring. Virtualization and Cloud. The 101 Most Useful Websites on the Internet. Services. Dropbox Tips, Tricks & Tools.
Screencasting. Tor. TAILS & TOR. Free Cloud Services: 2-20 GB Free Storage. PRIVACY TEST RESSOURCES. Tools: Developer. Filesharing. Monitoring & Management. #dNET 'Net décentralisé" / Privacity / Crypto / Anonymat / Cloud storage.