


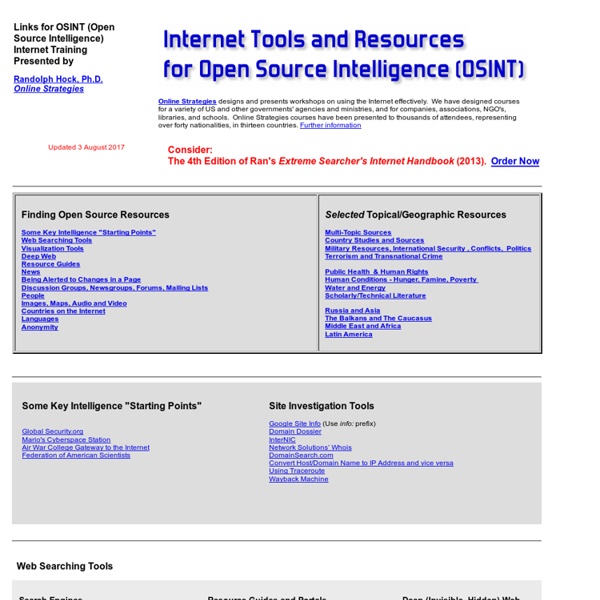
Network Intelligence Gathering This article is all about different information-gathering techniques on the network. It is the most essential and important task of attackers. Knowing the opponents and their interests can be valuable. Here I am going to show you which are the different ways and techniques one can do the network information/intelligence gathering. OSINT (Open-Source Intelligence) With an estimated 80% of required information available for use in an open source for specific information vital for a deep analysis in newspapers, magazines, industry newsletters, television transcripts, and blogs. OSINT makes our work easier, by using OSINT we are able to get important information in just a couple of minutes. Ethical Hacking Training – Resources (InfoSec)
How to Search Google Like a Pro: 11 Tricks You Have to Know Google is a powerful tool, but you’re missing out on a lot of that power if you just type words into it. Master Google and find the best results faster with these search tricks. Whether you’re an inexperienced user or a seasoned professional, you’ll probably find at least one search operator you weren’t aware of here. Many of Google’s search operators aren’t very well-known.
OSINT Tools - Recommendations List With the New Year fast approaching I thought now would be a great time to post the first draft of some recommended Open Source Intelligence (OSINT) gathering tools and resources. I will look to maintain this list overtime and have it grow, so if you come across something you think should be on the list, drop me an email or leave a comment for consideration. The reconnaissance phase of any engagement is very important and can often save you alot of time and of course money. Transcript: Sir Tim Berners-Lee Talks with Talis about the Seman I think, it depends really, it depends so much on how you look at it. So, the Web, and the Semantic Web, the existing Web... maybe we should say, the hypertext Web, the document Web, and a Data Web, are... In some ways we are not leaving the document Web behind.
5 Places to Look for Your Digital Footprint Recently, many iPhone and iPad users were incensed to learn that Siri — the personal digital assistant for iOS devices — has an eerily long memory. Unbeknownst to Apple customers, Siri sends all your queries directly to Apple's company’s servers, where it is kept for two years before being deleted. And while the truth about Siri is making headlines, it's not really shocking. Top 9 Popular OSINT Facebook Tools Social networks are indeed a big part of any OSINT investigation. They can reveal useful information about individuals, what they look for, how they do it, what they like and many other personal details. But OSINT Facebook data-gathering doesn’t stop with tools that show you only information about Facebook profiles. Today we’ll show you the best OSINT utilities that not only gather information about Facebook public data but also dig a little bit deeper under the surface — so keep reading.
Super Tuesday's Gadgets: Touch Screen Monitors, New Noteboo TV coverage of Super Tuesday was riveting, and not just because of the virtual tie between Democratics Barack Obama and Hillary Clinton, or the fascinating and involuntarily twitching left eye of John McCain during his victory speech. The networks also featured some of the latest shiny gadgetry available, including multi-touch screens, elephant-sized screens, floating logos and robotics. Okay, we’re kidding about that last part — the only robots we spotted were among the candidate pool. Here’s the lowdown on each news outfit’s gadget setup. CNN: The Perceptive Pixel Touch screen, a Pie Chart, and the Overflowing Dells Facebook FBStalker tool uses Graph Search for powerful OSINT analysis Facebook, and more in general social networks, is a platform that if not properly managed could harm user’s privacy, the fact that also friends’ social behavior could have a dangerous impact on our digital experience is very concerning. Recently at the Hack In The Box conference in Kuala Lumpur, security experts Jonathan Werrett and Keith Lee from SpiderLabs demonstrated how to conduct a powerful OSINT analysis using a simple tool they created, anyone using it could find a comprehensive amount of data on any user of the popular social network. The tool for information gathering on Facebook created by the researchers is named FBStalker, a name that give us the idea of the potential of the instrument.
Decentralized Information Group (DIG) Bread Well, it has been a long time since my last post here. So many topics, so little time. Some talks, a couple of Design Issues articles, but no blog posts. To dissipate the worry of expectation of quality, I resolve to lower the bar. More about what I had for breakfast. So The Graph word has been creeping in.
Free Moodle Web Conferencing Block and Activity - WiZiQ Live Cla 1. Can I use WizIQ Virtual Classroom with my Moodle website? Yes, the WizIQ Virtual Classroom is an online teaching tool you can integrate with your Moodle website and offer real-time collaboration and two-way communication, creating new capabilities for synchronous learning - all from within your Moodle online classroom. 2. If I purchase a plan of 5 teacher accounts with up to 10 attendee limit, does this mean I can run 5 classes with 10 attendees in each class and any number of times? Yes, this plans means that you can conduct 5 simultaneous classes with 5 teachers and 10 attendees in each class.