

How to Keep Your PC Safe With Sandboxing. If viruses and malware are a regular problem for you, or if you're simply worried that your antivirus program isn't sufficient, you can add an extra layer of defense to your PC by setting up a sandboxing application.

A properly sandboxed set of Windows programs can protect you from malware that your antivirus utilities miss, keeping your PC and your personal data more secure while you're shopping online, say, or visiting potentially dicey Web sites. Sandboxing is a form of software virtualization that lets programs and processes run in its isolated virtual environment. Typically, programs running within the sandbox have limited access to your files and system, and they can make no permanent changes. That means that whatever happens in the sandbox stays in the sandbox. Using the Trend Micro Ransomware File Decryptor Tool. Due to the advanced encryption of this particular Crypto-Ransomware, only partial data decryption is currently possible on files affected by CryptXXX V3.

The tool will try and fix certain file formats after the decryption attempt, including DOC, DOCX, XLS, XLSX, PPT, and PPTX (common Microsoft Office) files. The fixed file will have the same name of the original file with "_fixed" appended to the file name and will be placed in the same location. When opening the fixed file with Microsoft Office, it may present a message to try and repair the file again, and this process may be able to recover the document. Please note that due to the different versions of Microsoft Office and particular file behaviors, it is not guaranteed that this method will completely recover the document. However, for other files after the partial data decryption, users may have to utilize a 3rd party corrupted file recovery tool (such as the open source program JPEGSnoop*) to try and recover the full file. Home · AfshinZlfgh/pumax_ransomware_decryptor Wiki.
STOP ransomware (.STOP, .SUSPENDED - !!! YourDataRestore !!! txt) Support Topic - Page 2 - Ransomware Help & Tech Support. Hello.
I am here as a victim of Ransomware seeking whatever possible help decrypting my files that got infected . Here is the read.me message I got: our databases, files, photos, documents and other important files are encrypted and have the extension: .DATAWAIT The only method of recovering files is to purchase an decrypt software and unique private key. DMARC Inspector - dmarcian. FAQ - DMARC Wiki. Frequently Asked Questions This page has many frequently asked questions, and their answers, about different aspects of email authentication and DMARC.
They are organized into four areas: General, End User, Email Receiver (ISP, mailbox provider, domain owner), and Sender (domain or brand owner, email marketer, etc). Many of these questions were first asked on the public DMARC discussion lists. RACKSPACE - We Can Help You Protect Your Data. Your customers trust you with their information.
Are you doing enough to protect it? If your business generates, stores or transmits sensitive data, it’s your responsibility to keep that data safe.
How to Fix (and Adjust) Automatic Updating in Google Chrome. By default, Google Chrome automatically updates itself to make sure you’re running the safest and best optimized version of Chrome.
Sometimes the auto-update process hiccups, however, and you need to manually adjust it. The process is more complicated than it should be, but don’t worry: we’re here to walk you through it. In case you can’t see the picture above, the full text of this error message is “Google Chrome or Google Chrome Frame cannot be updated due to inconsistent Google Update Policy settings. Use the Group Policy Editor to set the update policy override for the Google Chrome Binaries application and try again;” Note: if your Google Chrome is updating just fine, stop reading this article and go check out our SysInternals Pro series instead.
Why Do I Want To Do This? Manage Chrome updates (Windows) - Google Chrome Enterprise Help. If a Chrome Browser release causes an issue in your organization, you can turn off auto-updates until the issue is resolved.
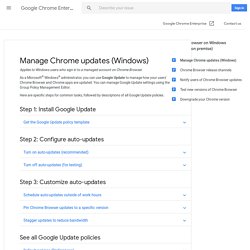
Change default installation folder c:\inetpub to another volume : The Official Microsoft IIS Forums. Brother MFC-9840-cdw and windows 7 - problems with control center. Hello Welcome to Microsoft answers (A).
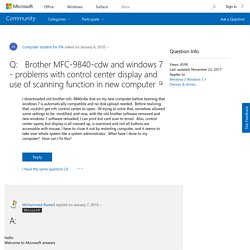
United States. Internet Content Filtering - DNSFilter. DNSFilter makes it easy to deploy comprehensive, yet customizable URL filtering and internet blocker policies specifically tailored to your network.
Start building your web content filtering policy by selecting the categories you want to block. Simply tell DNSFilter what type of websites you want to block - Adult Content, Illegal Content, Streaming Media, Chat & Instant Messaging, Social Networking, etc. - and we’ll do the rest. Our proprietary internet filtering algorithms intelligently categorize sites so you don’t have to constantly maintain a list of blocked sites. You can even enforce Google SafeSearch, YouTube restricted mode, and block uncategorized/unknown sites so nothing slips through the cracks.
Ubiquiti. CryptoWall 3. Can't start Disk Management - Unable to connect to Virtual Disk. Hi Robert111222333, Welcome to Microsoft Answers.
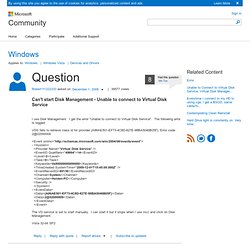
Check if the following steps help:A) Try this: i. Click start->Type Services.msc in the search bar and hit Enter ii. B) System File Checker tool scans system files and replaces incorrect versions of the system files by using the correct versions. Ii) Right-click cmd in the Programs list, and then click Run as administrator. Iii) At the command prompt, the following line, and then press ENTER:sfc /scannow. Asus UEFI/BIOS options - How to boot from DVD? DL - Asus R510C. Free ebooks from Microsoft Press. Ebook - Introducing Server 2012 PDF. Transfer documents to another printer: Print Services. Updated: January 21, 2005 Applies To: Windows Server 2003, Windows Server 2003 R2, Windows Server 2003 with SP1, Windows Server 2003 with SP2. SenderBase. System Center: Getting Started with System Center Essentials 2007. System Center Getting Started with System Center Essentials 2007. Viktor T. Toth - The Win 16 Subsystem has insufficient resources.
Cause: Windows NT 4.0 and Windows 2000 have a limit of 16384 GDI objects per session. This means that the only way to get around this is to log on in a different new session using Terminal Services/Remote Desktop. The console session (session 0) controls the actual physical display and input devices (keyboard mouse), and there is no way to get around this limit. Access Your Computer Anytime and Save Energy with Wake-on-LAN. A discussion about Wake-on-LAN.
Did you know that System Center Configuration Manager 2007 will include support for Wake-on-LAN? See for the full details, as well as Jeff Gilbert's blog posting at So what is Wake-on-LAN? It's a way to send a "magic packet" to a machine that isn't powered on. That package is received by the still-powered-up network card, and that causes the machine to be powered on. The Wikipedia entry at provides a good overview, and the links at the bottom provide the historical perspective. But there is no discussion about the different ways of implementing Wake-on-LAN, or the potential security implications of each of those ways. Limited broadcast. How To Launch Control Panel Application From The Command Line. How To View and Kill Processes On Remote Windows Computers. Windows provides several methods to view processes remotely on another computer. Terminal Server is one way or you can use the command line utility pslist from Microsoft Sysinternals site.
While both options are good alternatives, Windows XP and Vista provides a built in utility for viewing and killing process on remote Computers using Tasklist and Taskkill commands. Both tasklist.exe and taskkill,exe can be found in %SYSTEMROOT%\System32 (typically C:\Windows\System32) directory. To view processes on a remote Computer in your home, you will need to know the username and password on the Computer you want to view the processes. Once you have the user account information, the syntax for using tasklist follows: tasklist.exe /S SYSTEM /U USERNAME /P PASSWORD.
Windows 8. Migrating User Settings & Docs. Infrastructure Software and Management. Lisa. Hardware. MAC. WSUS. Server 2008. Microsoft Outlook categories. How to migrate custom categories to other users in Outlook 2002 and in Outlook 2003. In Microsoft Outlook, you can add new categories to the default Master Category List. This article describes how to share a modified Master Category List with other users. To share the Master Category List, export the Categories key from the registry and distribute this key to other users. NOTE: The registry key reference in the steps below only exists if the Master Category List has had a custom entry added. Important This section, method, or task contains steps that tell you how to modify the registry. However, serious problems might occur if you modify the registry incorrectly.
How to fix the 550 #5.1.0 Address rejected email problem « « Digital Tool Factory blog. RackSpace - Exchange Hybrid Email Details. Combine Exchange with Rackspace Email and save Exchange Hybrid is the smart way to handle email users with different needs, while saving money. Power users get the robust features of Microsoft Exchange, while casual users enjoy affordable, business-class Rackspace Email - all on the same domain! Integrated platforms, unified management, and Fanatical Support® make Exchange Hybrid an easy choice. 2 platforms, 1 domain Your users can share email at the same domain. RackSpace - Exchange Server Hosting Hybrid. Can't start Disk Management - Unable to connect to Virtual Disk.