

Clicking pictures has never been so much fun! - clikr. How To Hack Wireless. Google Search 3T. Synergy. ViewDNS.info - Your one source for DNS related tools! How to gain access to system account the most powerful account in Windows. « Alien Eyes. There is an account in Microsoft Windows that is more powerful than the Administrator account in Windows Operating Systems.

That account is called System account it is similar to the root OR super user in the Linux/Unix world . I will show you how to access this system account in this article. You can use this facility for removing programs that are causing problems to your system, malware etc. Introduction If you look at the task manager (which can be launched by pressing [CTRL]+[ALT]+[DEL]) you will see some processes that are running with System level privileges. System is the highest account in Windows (like root),You can be a super power user by accessing the system account (even while you are logged in as a restricted user) Note: Accessing system account may cause serious problems.
Local system differs from an administrator account in that it has full control of the operating system, similar to root on a Unix machine. Check the name of the account you’ve logged into (Click start. Peoplehacking - ToorCon 2010. 64-bit OS written entirely in assembly. Top 10 facebook Hacks. How to Hack: Ethical Hacking and Cyber Security. Exploits Database by Offensive Security. Cracking. Index of / Overview - Spotify - Developers' home.
Use the Metadata API to explore the Spotify music catalog and retrieved track, album and artist data.
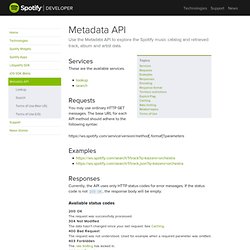
Services These are the available services. Requests You may use ordinary HTTP GET messages. The base URL for each API method should adhere to the following syntax: Examples Responses Currently, the API uses only HTTP status codes for error messages. Available status codes The request was successfully processed. 304 Not Modified The data hasn’t changed since your last request. 400 Bad Request The request was not understood. 403 Forbidden The rate limiting has kicked in. 404 Not Found The requested resource was not found. 406 Not Acceptable The requested format isn’t available. 500 Internal Server Error The server encountered an unexpected problem. 503 Service Unavailable The API is temporarily unavailable.
Encoding All requests must be UTF-8. Response format There are two ways of negotiating response formats. In order to search for “true affection”, and get JSON back, you can either do GET /search/1/track? <? Google Hacking Database, GHDB, Google Dorks. Internet Security and Ethical Hacking. How To. How to There are just 3 simple steps for watching your videos on our site: 1.
First you need to copy video url from hosting site. We currently support all most popular video hosting websites and megavideo alternatives: putlocker.com, novamov.com, sockshare.com, videoweed.com, veoh.com, divxstage, filebox, filenuke, movreel, movshare, nosvideo, nowdownload.eu, nowvideo.eu, sharerepo, sharesix, vidbux, videobam, videoslasher, vidhog, maxvideo, youtube and vidxden. Cracks serials keygens keys warez software application program download. Glasnost: Test if your ISP is shaping your traffic. The goal of the Glasnost project is to make ISPs' traffic shaping policies transparent to their customers.
To this end, we designed Glasnost tests that enable you to check whether traffic from your applications is being rate-limited (i.e., throttled) or blocked. Glasnost tests work by measuring and comparing the performance of different application flows between your host and our measurement servers. The tests can detect traffic shaping in both upstream and downstream directions separately. The tests can also detect whether application flows are shaped based on their port numbers or their packets' payload. For more details on how Glasnost tests work, please read our NSDI 2010 paper. As of Feburary 2017 Glasnost is no longer available. Who are we? We are researchers at the Max Planck Institute for Software Systems.