

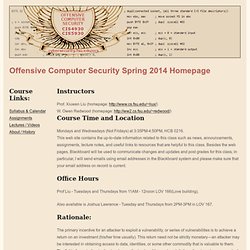
Google Search Operators - Google Guide - Vimperator. The following table lists the search operators that work with each Google search service.

Click on an operator to jump to its description — or, to read about all of the operators, simply scroll down and read all of this page. The following is an alphabetical list of the search operators. This list includes operators that are not officially supported by Google and not listed in Google’s online help. Each entry typically includes the syntax, the capabilities, and an example. Some of the search operators won’t work as intended if you put a space between the colon (:) and the subsequent query word. Allinanchor: If you start your query with allinanchor:, Google restricts results to pages containing all query terms you specify in the anchor text on links to the page. Anchor text is the text on a page that is linked to another web page or a different place on the current page. Offensive Computer Security Home Page (CIS 4930 / CIS 5930) Spring 2014 - Vimperator.
Instructors Prof.
Xiuwen Liu (homepage: W. Owen Redwood (homepage: Course Time and Location. Index of / - Vimperator. Home - Vimperator.
[PentesterLab] Learn Penetration Testing: The Right Way. [PentesterLab] The Exercises. [PentesterLab] Bootcamp. RFC Sourcebook - Vimperator. Big Port DB. The TCP/IP Guide. The TCP/IP Guide Welcome to the free online version of The TCP/IP Guide!
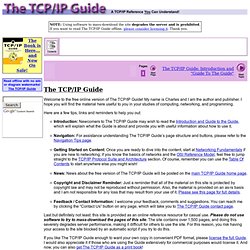
My name is Charles and I am the author and publisher. I hope you will find the material here useful to you in your studies of computing, networking, and programming. Here are a few tips, links and reminders to help you out: Introduction: Newcomers to The TCP/IP Guide may wish to read the Introduction and Guide to the Guide, which will explain what the Guide is about and provide you with useful information about how to use it. Last but definitely not least: this site is provided as an online reference resource for casual use. If you like The TCP/IP Guide enough to want your own copy in convenient PDF format, please license the full Guide. Free Online Virus, Malware and URL Scanner - Vimperator. FotoForensics - Vimperator. DanMcInerney/LANs.py · GitHub - Vimperator.
v3n0m-Scanner/Linux-v3n0m · GitHub - Vimperator.
DVWA - Damn Vulnerable Web Application. Damn Vulnerable Web App. BlackArch Linux. BlackArch - ArchWiki - Vimperator. Specialty Distributions alphaOS alphaOS is a simple and minimalistic Linux distribution for the x86-64 architecture, built using Linux Live Kit set of scripts developed by Tomas M.
It is based on Arch Linux and uses pacman as the default package manager. This operating system features highly configurable and lightweight Openbox window manager. Modular by design, alphaOS makes it easy to add desired functionality. Antergos Antergos is an elegant and very customizable system for desktop. BlackArch/blackarch · GitHub - Vimperator.
Linux and Open source PortSpoof – An interesting anti-snooping tool for Linux - Vimperator. Fool those who try to portscan your system!

The Portspoof program is designed to enhance OS security through emulation of legitimate service signatures on otherwise closed ports. It is meant to be a lightweight, fast, portable and secure addition to the any firewall system or security infrastructure. The general goal of the program is to make the port scanning software (Nmap/Unicornscan/etc) process slow and output very difficult to interpret, thus making the attack reconnaissance phase a challenging and bothersome task I’ve found the concept behind this small program really interesting : instead of close all your ports with a firewall deceive the real ports, thus annoying the guys who are running portscan versus your server/computer. The Portspoof program primary goal is to enhance OS security through a set of techniques that will slow down and keep your attackers out from staying low profile during their reconnaissance against your system(s).
Art of Active (Offensive) Defense Features 1. Drk1wi/portspoof. Pentester and Technical Manager - Vimperator. An Intro To Penetration Testing - Vimperator. SecTools.Org Top Network Security Tools. Excited Bit Tools - Vimperator. Linux and Open source Understanding Nmap Commands: In depth Tutorial with examples - Vimperator.
Article by James Hawkins As we all know, Nmap (Network Mapper) is a stealth port scanner widely used by network security experts (including forensics & Pen-testing Experts).
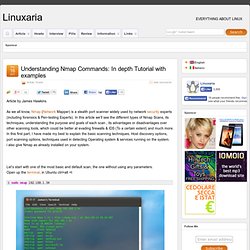
In this article we’ll see the different types of Nmap Scans, its techniques, understanding the purpose and goals of each scan , its advantages or disadvantages over other scanning tools, which could be better at evading firewalls & IDS (To a certain extent) and much more. In this first part, I have made my best to explain the basic scanning techniques, Host discovery options, port scanning options, techniques used in detecting Operating system & services running on the system. i also give Nmap as already installed on your system. Let’s start with one of the most basic and default scan, the one without using any parameters. Open up the terminal, in Ubuntu ctrl+alt +t This is a basic scan of the local IP address 192.168.1.34, we use sudo to gain administrator privileges, and then we give the target to Nmap.
ZMap · The Internet Scanner - Vimperator. Protect The Business - Enable Access. The Ethical Hacker Network. The Hacker News - Security in a Serious way. Ethical Hacking-Your Way To The World Of IT Security. Ethical Hacking and Penetration testing. Darknet - The Darkside - Ethical Hacking, Penetration Testing & Computer Security. IntroX86. Creator: Xeno Kovah @XenoKovah License: Creative Commons: Attribution, Share-Alike ( Class Prerequisites: Must have a basic understanding of the C programming language, as this class will show how C code corresponds to assembly code.

Lab Requirements: Requires a Windows system with Visual C++ Express Edition. Requires a Linux system with gcc and gdb, and the CMU binary bomb installed (use the one below, that link now holds the 64 bit version and this is the 32 bit class). Class Textbook: “Professional Assembly Language” by Richard Blum. Free IDA Pro Reverse Code Engineering and Binary Auditing Training Material for University Lectures. Penetration Testing and Vulnerability Analysis - Home. Blue For The Pineapple …. Background The WiFi Pineapple, was a device coined by the Hak5 (www.hak5.org) Team back in 2008.

Originally it was a hacked Fon/Fonera AccessPoint (AP) with Karma patches applied to hostapd. Back then Digninja (Robin wood) called it Jasager ( it was called this because the AP software answered “Yes” to all WiFi Beacon Frames; if a WiFi client was looking for the SSID BTOpenzone the Pineapple(or Jasager) would reply “That’s Me!” , if a second WiFi client was looking for an SSID of Starbucks, again the Pineapple would reply “Thats Me!” – Thus tricking unsuspecting users/devices into associating with its private network. As the device was small, it was a running joke to hide it within an actual pineapple. Cheat Sheet : All Cheat Sheets in one page. GE Geek - PC Tech Quick Reference BookMarks/ Tools / Solutions - Vimperator. Reverse Shell Cheat Sheet. If you’re lucky enough to find a command execution vulnerability during a penetration test, pretty soon afterwards you’ll probably want an interactive shell.
If it’s not possible to add a new account / SSH key / .rhosts file and just log in, your next step is likely to be either trowing back a reverse shell or binding a shell to a TCP port. This page deals with the former. Your options for creating a reverse shell are limited by the scripting languages installed on the target system – though you could probably upload a binary program too if you’re suitably well prepared. Explainshell.com - match command-line arguments to their help text. ->Security Lesson, Tools, Exploits, Topics, Forensics, Clothing. Privacy in Digital Era. Your Computer To date the NSA’s and FBI’s primary attacks on Tor users have been MITM attacks (NSA) and hidden service web server compromises (FBI) which either sent tracking data to the Tor user’s computer, compromised it, or both.
Thus you need a reasonably secure system from which you can use Tor and reduce your risk of being tracked or compromised. Don’t use Windows. Just don’t. This also means don’t use the Tor Browser Bundle on Windows. Your Environment Tor contains weaknesses which can only be mitigated through actions in the physical world. Never use Tor from home, or near home. Welcome - Vimperator. Dot]com - Vimperator. Index of /data/tut/Assembly_Videos - Vimperator. Metasploit Unleashed. Metasploit. Metasploit From Wikibooks, open books for an open world Jump to: navigation, search The Metasploit Book This project is an attempt to document the tools and research created by the Metasploit Project. Metasploit/MeterpreterClient. TODO - meterpreter introduction. Core Commands[edit] ?
[edit] Backtrack Tutorials. Hacking and network security tutorials - Vimperator. Socket programming tutorials in C, Python, Perl, Php, Java and Winsock - Vimperator. SocketTCP.pdf - Vimperator. Excess XSS: A comprehensive tutorial on cross-site scripting - Vimperator.