

Platform Cooperativism on Livestream. The Peer to Peer Search Engine: Home. Top 10 Best Alternatives To YouTube. The open-source whistleblower submission system managed by Freed... Aaron Swartz Hackathon This Weekend Is Your Chance To Hack for a Better World. A Beginners Guide Into The Darknet AnonHQ. A lookup, with searching engines like Google or Bing, generally comes back with a large number of pages for every term typed.

One can try to estimate “the Internet” by considering the number of sites that exist solely for searching x amount of phrases, and you will be astonished by the results that Google, Yahoo or any other respective search engine would offer. This bit of the world wide web is visible and known to people. But what Google and the rest are doing are “just scratching the surface.” Save WiFi/Individual Comments - LibrePlanet. Right now, the FCC is considering a proposal to require manufacturers to lock down computing devices (routers, PCs, phones) to prevent modification if they have a "modular wireless radio"[1][2] or a device with an "electronic label"[3].
The rules would likely: Restrict installation of alternative operating systems on your PC, like GNU/Linux, OpenBSD, FreeBSD, etc. Prevent research into advanced wireless technologies, like mesh networking and bufferbloat fixes Ban installation of custom firmware on your Android phone Discourage the development of alternative free and open source WiFi firmware, like OpenWrt Infringe upon the ability of amateur radio operators to create high powered mesh networks to assist emergency personnel in a disaster. TrueCrypt. TrueCrypt is a discontinued source-available freeware utility used for on-the-fly encryption (OTFE).
It can create a virtual encrypted disk within a file or encrypt a partition or (under Microsoft Windows except Windows 7/8 boot drive with GPT) the entire storage device (pre-boot authentication). On 28 May 2014, the TrueCrypt website announced that the project was no longer maintained and recommended users to find alternative solutions. Though development of TrueCrypt has ceased, an independent audit of TrueCrypt has concluded that no significant flaws are present.[8] Alternatives include two freeware projects based on the TrueCrypt code, VeraCrypt and CipherShed, as well as numerous commercial and open-source products. History[edit] Internet Party (New Zealand) The Internet Party is a political party in New Zealand promoting Internet freedom and privacy.

Founded in January 2014 with the support of Internet entrepreneur, Kim Dotcom. The party contested the 2014 New Zealand elections under an electoral alliance with the Mana Movement but failed to win any seats in the House of Representatives of New Zealand. Kim Dotcom. He rose to fame in Germany in the 1990s as a self-proclaimed internet entrepreneur.
He received prison time in 1994 for computer fraud and data espionage, and another suspended prison sentence in 2003 for insider trading and embezzlement.[13] Personal life[edit] Dotcom was born as Kim Schmitz in Kiel, West Germany.[17] His mother was Finnish and so he holds a Finnish passport. His father was German. Beginners' guide. 5 Best Free VPNs. DedSec - Watch Dogs Wiki. "A secret society of hackers, serving our own brand of justice" ―DedSec DedSec is a secret hacking collective featured in the game Watch Dogs.
Among their numbers is the son of Connor Malley (as indicated in the mission "No Turning Back"), and tattoo artist Clara Lille, who directly assists Aiden Pearce. Description Edit. Raymond "T-Bone" Kenney - Watch Dogs Wiki. "Careful, Aiden, when the lights go out, bad things tend to happen.

" ―T-Bone, to Aiden before leaving the bunker during "Sometimes You Still Lose". Raymond Kenney or "T-Bone Grady" is a supporting character that appears in Watch Dogs and is the main protagonist of Watch Dogs: Bad Blood. Description Edit. Tailored Access Operations. A reference to Tailored Access Operations in an XKeyscore slide The Office of Tailored Access Operations (TAO) is a cyber-warfare intelligence-gathering unit of the National Security Agency (NSA).
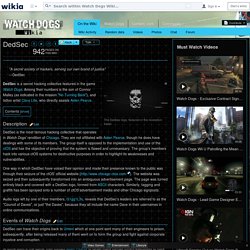
It has been active since at least circa 1998.[1][2] TAO identifies, monitors, infiltrates, and gathers intelligence on computer systems being used by entities foreign to the United States.[3][4][5][6] The NSA terms these activities "computer network exploitation". TAO is reportedly "now the largest and arguably the most important component of the NSA's huge Signal Intelligence (SIGINT) Directorate, consisting of more than 1,000 military and civilian computer hackers, intelligence analysts, targeting specialists, computer hardware and software designers, and electrical engineers. "[1] Physical locations[edit] Pretty Good Privacy. Tails (operating system) XKeyscore. Logo for the XKeyscore program XKeyscore or XKEYSCORE (abbreviated as XKS) is a formerly secret computer system first used by the United States National Security Agency for searching and analyzing global Internet data, which it collects on a daily basis.

The program has been shared with other spy agencies including the Australian Signals Directorate, Communications Security Establishment Canada, New Zealand's Government Communications Security Bureau and the German Bundesnachrichtendienst.[1] The program's purpose was publicly revealed in July 2013 by Edward Snowden in The Sydney Morning Herald and O Globo newspapers.
TorrentFreak. Datataffel.