

Reverse IP Lookup - Find Other Web Sites Hosted on a Web Server. Find other sites hosted on a web server by entering a domain or IP address above.
Note: For those of you interested, as of May 2014, my database has grown to over 100 million domain names. I am now offering this domain list for purchase. A reverse IP domain check takes a domain name or IP address pointing to a web server and searches for other sites known to be hosted on that same web server. Data is gathered from search engine results, which are not guaranteed to be complete. IP-Address.org provides interesting visual reverse IP lookup tool. Background All web sites are hosted on web servers, which are computers running specialized software that distribute web content as requested.
As of 2003, more than 87% of all active domains names were found to share their IP addresses (i.e. their web servers) with one or more additional domains. While IP sharing is typically transparent to ordinary users, it may cause complications for both search engine optimization and web site filtering. Solution. Yara-project - A malware identification and classification tool. RIPS - free PHP security scanner using static code analysis. Code search ⋅ search. Protect Your Interwebs. BFT a Browser forensic tool. Labs Research: Solving a Little Mystery. Firmware analysis is a fascinating area within the vast world of reverse engineering, although not very extended.

Sometimes you end up in an impasse until noticing a minor (or major) detail you initially overlooked. That's why sharing methods and findings is a great way to advance into this field. While looking for certain information during a session of reversing, I came across this great post. There is little to add except for solving the 'mystery' behind that simple filesystem and mentioning a couple of technical details. This file system is part of the WindRiver's Web Server architecture for embedded devices, so you will likely find it inside firmwares based on VxWorks. Maltego 3 > Maltego Client. Code Exploration Blog. Jsunpack-n - A generic JavaScript unpacker. Jsunpack-n emulates browser functionality when visiting a URL.

It's purpose is to detect exploits that target browser and browser plug-in vulnerabilities. It accepts many different types of input: TheHarvester – Gather E-mail Accounts, Subdomains, Hosts, Employee Names – Information Gathering Tool. TheHarvester is a tool to gather emails, subdomains, hosts, employee names, open ports and banners from different public sources like search engines, PGP key servers and SHODAN computer database.

This tools is intended to help Penetration testers in the early stages of the project It’s a really simple tool, but very effective. The sources supported are: Google – emails,subdomains/hostnames Google profiles – Employee names Bing search – emails, subdomains/hostnames,virtual hosts Pgp servers – emails, subdomains/hostnames Linkedin – Employee names Exalead – emails,subdomain/hostnames New Features Time delays between requests XML and HTML results export Search a domain in all sources Virtual host verifier Shodan computer database integration Active enumeration (DNS enumeration,DNS reverse lookups, DNS TLD expansion) Basic graph with stats.
Raz0r.name — блог о web-безопасности. Тема декодирования зашифрованных PHP-скриптов уже однажды мной затрагивалась в посте PHP и зашифрованный код . В нем я описал способ получения значений всех инициализированных переменных и списка объявленных функций в скрипте, зашифрованным протектором ionCube. Тогда, в 2009 году, расшифровать скрипт под ionCube было проблематично – на тот момент существовали лишь платные сервисы. Однако с ростом популярности ionCube стало ясно, что рано или поздно его постигнет участь Zend Encoder (сейчас Zend Guard), павшего в 2008 году перед ставшими повсеместно доступными «дезендерами». Действительно, за последнее время появилось множество декодеров ionCube, можно даже найти бесплатные онлайн-сервисы. Один из них позволяет расшифровать практически любые скрипты. Antepedia. Koders.com. Open Search - Home. FAQ - GrepCode.com - Java Source Code Search 2.0.
DEFT Linux 7 RC1. List of tools for static code analysis. This is a list of tools for static code analysis.

Language[edit] Multi-language[edit] .NET[edit] JavaScript[edit] Google's Closure Compiler – JavaScript optimizer that rewrites code to be faster and smaller, and checks use of native JavaScript functions.JSHint – A community driven fork of JSLint.JSLint – JavaScript syntax checker and validator. Cppcheck - A tool for static C/C++ code analysis. FindBugs v.2.0 - Find Bugs in Java Programs. Javasnoop - A tool that lets you intercept methods, alter data and otherwise hack Java applications running on your computer. Normally, without access to the original source code, testing the security of a Java client is unpredictable at best and unrealistic at worst.

With access the original source, you can run a simple Java program and attach a debugger to it remotely, stepping through code and changing variables where needed. Doing the same with an applet is a little bit more difficult. Unfortunately, real-life scenarios don't offer you this option, anyway. Compilation and decompilation of Java are not really as deterministic as you might imagine. Therefore, you can't just decompile a Java application, run it locally and attach a debugger to it. Next, you may try to just alter the communication channel between the client and the server, which is where most of the interesting things happen anyway. VirSCAN.org - Free Multi-Engine Online Virus Scanner v1.02, Supports 36 AntiVirus Engines!
Arachni Web scanner (CLI & WEB GUI) ~ Sudhir @ Pentester. Download the CDE package from: Linux users enjoy the privilege of a CDE package which is a compressed archive and contains a full preconfigured Linux environment in the form of a sandbox.

Quick Basic Usage of Arachni: To see help type : p0f v3. Copyright (C) 2012 by Michal Zalewski <lcamtuf@coredump.cx> Yeah, it's back!
1. What's this? Loadbalancer-finder - Load Balancer Finder. Wavsep - Web Application Vulnerability Scanner Evaluation Project. A vulnerable web application designed to help assessing the features, quality and accuracy of web application vulnerability scanners. This evaluation platform contains a collection of unique vulnerable web pages that can be used to test the various properties of web application scanners. AS OF 2014/01/01, The Project File Hosting was migrated to Sourceforge. New downloads (WAVSEP 1.5+) can be obtained from the project sourceforge repository Quickstart: The easiest way to get started with wavsep evaluations is to use a pre-installed instance in one of the following training VMs (note that some of the path traversal test cases only work under windows): Web Security Dojo v2.0+ OWASP Broken Web Apps null's GAMEOVER VM.
Особенности поведения нового TCP/IP стека Windows / Блог компании Positive Technologies. Начиная с Windows Vista, компания Microsoft в своих операционных системах перешла на новый сетевой стек — Next Generation TCP/IP Stack.
Стек включает в себя множество различных плюшек: Windows Filtering Platform, масштабируемое TCP-окно и прочие вкусности, однако речь пойдет совсем не о них, а об одной конкретной особенности поведения нового сетевого стека. Всякий уважающий себя сетевой сканер должен уметь определять ОС сканируемого узла, при этом чем больше параметров используется, тем более точный ожидается результат. Online JavaScript beautifier. Metagoofil - Metadata Information Gathering.
Metagoofil is an information gathering tool designed for extracting metadata of public documents (pdf,doc,xls,ppt,docx,pptx,xlsx) belonging to a target company.
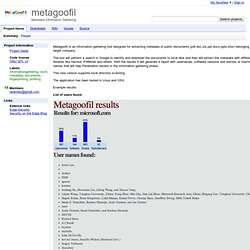
The tool will perform a search in Google to identify and download the documents to local disk and then will extract the metadata with different libraries like Hachoir, PdfMiner and others. With the results it will generate a report with usernames, software versions and servers or machine names that will help Penetration testers in the information gathering phase. This new version supports local directory scanning The application has been tested in Linux and OSX.