

Social Engineering — The Art Of Hacking Humans. Infosec_getting_started/README.md at master · gradiuscypher/infosec_getting_started. Hack with GitHub. Awesome-Hacking/README.md at master · Hack-with-Github/Awesome-Hacking. Security forum. Tools for a Safer PC. An important aspect of securing any system is the concept of “defense-in-depth,” or having multiple layers of security and not depending on any one approach or technology to block all attacks.

Here are some links to tools and approaches that I have found useful in stopping malware from invading a PC. Your mileage may vary. Learn, Memorize, Practice the 3 Rules Follow Krebs’s 3 Basic Rules for online safety, and you will drastically reduce the chances of handing control over your computer to the bad guys. In short, 1) If you didn’t go looking for it, don’t install it; 2) If you installed, update it. 3) If you no longer need it, get rid of it! Keep Up-to-Date with Updates! It shouldn’t be this way, but the truth is that most software needs regular updating. Put a Leash on Javascript Most Web sites use JavaScript, a powerful scripting language that helps make sites interactive.
Anonymat - Censure. Anonymous. Digital citizenship. Transmit Data Through Sound: Quiet. This library uses liquid SDR to transmit data through sound.
This makes it suitable for sending data across a 3.5mm headphone jack or via speaker and mic. Quiet can build standalone binaries for encoding/decoding data via .wav files or for streaming through your soundcard via PortAudio. It can also be built as a library to be consumed by other C programs. TOR Mail Encrypted Server: OnionMail. TOR Mail Encrypted Server for Hidden Services OnionMail is an anonymous, encrypted mail server made to run on TOR network without losing the ability to communicate with the Internet.

All OnionMail servers are configured as TOR hidden services and use SSL (via STARTTLS). To use OnionMail all you need is an email client connected to the TOR network – Example: Claws-Mail or Thunderbird. All OnionMail servers are connected in a ‘federated network’. All ‘federated servers’ can connect to the Internet via exit/enter servers to forward messages between networks while OnionMail forwards messages between TOR and the Internet in a transparent manner. Pattern Matching Swiss Knife: YARA. YARA is a tool aimed at (but not limited to) helping malware researchers to identify and classify malware samples.
With YARA you can create descriptions of malware families (or whatever you want to describe) based on textual or binary patterns. Each description, a.k.a rule, consists of a set of strings and a boolean expression which determine its logic. Dark Internet Mail Environment: DIME. Internet electronic mail (email) was designed in the early days of the Internet, and so lacks any mechanism to protect the privacy of the sender and addressee.
Several techniques have been used in an attempt to increase the privacy of email. These techniques have provided either modest increases in privacy, or have proven to be very difficult to use for most people. In addition to protection of content, truly private email must limit information disclosed to handling agents, only exposing information necessary for delivery (the metadata), and provide robust identity guarantees which prevent the impersonation of senders. The Dark Internet Mail Environment (DIME) achieves this level of privacy with core protocols using multiple layers of key management and multiple layers of message encryption.
The DIME Protocol Specifications contain the full technical details of the DIME. Automated Modular Cryptanalysis Tool: FeatherDuster. Automated Modular Cryptanalysis Tool FeatherDuster is a tool written by Daniel “unicornfurnace” Crowley of NCC Group for breaking crypto which tries to make the process of identifying and exploiting weak cryptosystems as easy as possible.

Cryptanalib is the moving parts behind FeatherDuster, and can be used independently of FeatherDuster. Cryptanalib can be used separately of FeatherDuster to make Python-based crypto attack tools. Documentation for cryptanalib functions can be accessed through the Python help() function The analysis engine in Cryptanalib, used by FeatherDuster, can automatically detect encodings and decode samples.
The engine assumes that all samples are generated with the same process (for instance, base64encode(aes_encrypt(datum))), but can handle mixed samples to some degree. Multiprotocol Network Emulator - Simulator: IMUNES. IMUNES GUI is a simple Tcl/Tk based management console, allowing for specification and management of virtual network topologies.
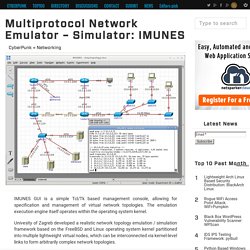
The emulation execution engine itself operates within the operating system kernel. Univesity of Zagreb developed a realistic network topology emulation / simulation framework based on the FreeBSD and Linux operating system kernel partitioned into multiple lightweight virtual nodes, which can be interconnected via kernel-level links to form arbitrarily complex network topologies.
Main advantages: Open-Source Phishing Toolkit: gophish. Gophish is an open-source phishing toolkit designed for businesses and penetration testers.

It provides the ability to quickly and easily setup and execute hishing engagements and security awareness training. Installing Gophish Using Pre-Built Binaries. Malicious Traffic Detection System: Maltrail. Maltrail is a malicious traffic detection system, utilizing publicly available (black)lists containing malicious and/or generally suspicious trails, along with static trails compiled from various AV reports and custom user defined lists, where trail can be anything from domain name (e.g. zvpprsensinaix.com for Banjori malware), URL (e.g. for known malicious executable) or IP address (e.g. 103.224.167.117 for known attacker).
Also, it has (optional) advanced heuristic mechanisms that can help in discovery of unknown threats (e.g. new malware). The following (black)lists (i.e. feeds) are being utilized: As of static entries, the trails for the following malicious entities (e.g. malware C&Cs) have been manually included (from various AV reports): Open-Source Disk Encryption for Windows: LibreCrypt. LibreCrypt is an Open-Source “on-the-fly” transparent disk encryption for Windows (both 32 and 64 bit).
LUKS compatible – (formerly DoxBox). This software can create “virtual disks” on your computer – anything written to these disks is automatically encrypted before being stored on your computer’s hard drive. Features Easy to use, with a ‘wizard’ for creating new ‘containers’.Full transparent encryption, containers appear as removable disks in Windows Explorer.Explorer mode lets you access containers when you don’t have admin permissions.Compatible with Linux encryption, Cryptoloop “losetup”, dm-crypt, and LUKS.
Please note this is a Beta version with some known limitations. New features in version 6.2. Best Free Server Monitoring Tools. Monitoring Linux System and Network Performance can be a daunting task for a new system admin. Network and system monitoring is a broad category. There are solutions that monitor for the proper operation of servers, network gear, and applications, and there are solutions that track the performance of those systems and devices, providing trending and analysis.
These tools can make your life easier. Note: All tools are available under all flavors of Linux . Top – Linux Process Monitoring. Network Forensic Analysis Tool: Xplico. CyberPunk » Digital Forensic The goal of Xplico is extract from an internet traffic capture the applications data contained. Open Source Network Access Control: Packet Fence. PacketFence is a fully supported, trusted, Free and Open Source network access control (NAC) system. Boasting an impressive feature set including a captive-portal for registration and remediation, centralized wired and wireless management, 802.1X support, layer-2 isolation of problematic devices, integration with IDSs and vulnerability scanners; PacketFence can be used to effectively secure networks – from small to very large heterogeneous networks.
Free and Open Source Network Access Control Boasting an impressive feature set including a captive-portal for registration and remediation, centralized wired and wireless management, powerful BYOD management options, 802.1X support, layer-2 isolation of problematic devices; PacketFence can be used to effectively secure networks small to very large heterogeneous networks. Among the different markets are : Network Security Testing: Evil Foca [DefCon Edition] Evil Foca is a tool for security pentesters and auditors whose purpose it is to test security in IPv4 and IPv6 data networks.
The software automatically scans the networks and identifies all devices and their respective network interfaces, specifying their IPv4 and IPv6 addresses as well as the physical addresses through a convenient and intuitive interface. Network Security Testing: Evil Foca The tool is capable of carrying out various attacks such as: MITM over IPv4 networks with ARP Spoofing and DHCP ACK Injection.MITM on IPv6 networks with Neighbor Advertisement Spoofing, SLAAC attack, fake DHCPv6.DoS (Denial of Service) on IPv4 networks with ARP Spoofing.DoS (Denial of Service) on IPv6 networks with SLAAC DoS.DNS Hijacking.
Suricata - Open Source Next Generation IDS/IPS Engine. The Suricata Engine is an Open Source Next Generation Intrusion Detection and Prevention Engine. This engine is not intended to just replace or emulate the existing tools in the industry, but will bring new ideas and technologies to the field. Suricata 3.0 Available! OISF is part of and funded by the Department of Homeland Security’s Directorate for Science and Technology HOST program (Homeland Open Security Technology), by the the Navy’s Space and Naval Warfare Systems Command (SPAWAR), as well as through the very generous support of the members of the OISF Consortium.
More information about the Consortium is available, as well as a list of our current Consortium Members. The Suricata Engine and the HTP Library are available to use under the GPLv2. Network Security Toolkit - NST. Automate Security Audit: Netool.sh. System Hardening Guide. Rogue Wi-Fi Access Point: 3vilTwinAttacker. CyberPunk » Information Gathering This tool create an rogue Wi-Fi access point , purporting to provide wireless Internet services, but snooping on the traffic 3vilTwinAttacker is security tool that provide the Rogue access point to Man-In-The-Middle and network attacks. purporting to provide wireless Internet services, but snooping on the traffic. can be used to capture of credentials of unsuspecting users by either snooping the communication by phishing. Adversary Resistant Computing Platform: SubgraphOS. Subgraph OS is an adversary resistant computing platform. The main purpose of Subgraph OS is to empower people to communicate, share, and collaborate without fear of surveillance and interference.
CyberPunk: Open Source CyberSecurity. #!/bin/the hacker's choice - THC. NST Links. Insecure.Org - Nmap Free Security Scanner, Tools & Hacking resources. SecDev.org. GitHub - PowerShellMafia/PowerSploit: PowerSploit - A PowerShell Post-Exploitation Framework. NST Pro Site. Open Source abuse management. GitHub - AbuseIO/AbuseIO at AbuseIO-3.0: AbuseIO is a toolkit to receive, process, correlate and notify about abuse reports received by network operators, typically hosting and access providers.
Creepy/README.md at master · ilektrojohn/creepy. Creepy by ilektrojohn. Creepy, the Geolocation Information Aggregator. What is Creepy ? So what is Creepy actually and how does it come into the “Geolocation” picture ? Creepy is a geolocation information aggregation tool. It allows users to gather already published and made publicly available geolocation information from a number of social networking platforms and image hosting services. In its current, beta form, it caters to harvesting geolocation information from twitter in the form of geotagged tweets, foursquare check-in’s, geotagged photos posted on twitter via image hosting services such as yfrog, twitpic, img.ly, plixi and others, and Flickr. The geolocation information that Creepy retrieves is presented to the user in the form of points on a navigable embedded map along with a list of locations (geographic latitude and longitude accompanied with the date and time). Introduction — Terminology.
Home - OkayFreedom. Cryptostorm's community forum - cryptostorm forum. EC-Council Certification Guide: Overview and Career Paths - Tom's IT Pro. Best Information Security Certifications for 2016 - Certs - Tom's IT Pro. InfoSec professionals who want to set themselves apart as leaders in IT security should seriously consider one of these top five information security certifications for 2016. IT Career Paths - A Guide to Credentials and Certifications. If you love technology, then the IT field can offer a number of opportunities and areas to specialize in. As you hone in on your skills, you can validate your knowledge by advancing up the certification ladder to achieve new career heights. Anonymous. Ciberativismo. Net Privacy and Anonymity. Anonymat - Censure.
Web Privacy. Deep_Web. Training and cheatsheets. Anonymat - Censure. Minds. Web Privacy. Web Privacy. Wilders Security Forums. SecTools.Org Top Network Security Tools. Most popular VMWare Virtual Appliances for IT Administrators. Updated on September 23, 2009: Please review the updated list of virtual appliances. You may also be interested in reviewing virtual appliances for Security. The original post has been retained as a historical reference. The download links for most of the appliances in the following table no longer work since VMware has revamped the Appliance Marketplace.
Thanks I have ranked the virtual appliances for IT Administrators available at the VMWare Virtual Appliance Marketplace (VVAM) as described below. Methodology I accessed the listings for Administration, sorted them by Rating and cut and pasted the first 100 listing into an Excel spreadsheet.The Star rating that is visible on the web page shows up as a decimal fraction in Excel, this is what you see in the Customer Rating column below.I computed a Rank for each listing by multiplying the Customer Rating x 100 x the number of ratings for that appliance.Finally I sorted the result by the rank to prepare the table that appears below.
Whonix/apparmor-profile-torbrowser. Introducing Slur. Pro Hack. Your secure private social network. Ipredia OS for anonymous browsing and communications. Mobile phone private messaging with Schmoose App. SHREDroid. Securely wipe Android phone data with SHREDroid. Secure Text Messaging: The Mobile Enterprise. Email Encryption with Tutanota - Easy and Secure. Free encrypted webmail service Tutanota. ProtonMail Is A Swiss Secure Mail Provider That Won’t Give You Up To The NSA. ProtonMail. Web Privacy. Web Privacy. Anonymat - Censure. Erik Voorhees response to NYDFS Bitcoin Proposal. Cryptome. Let them Find us. Anonymous. How to Create a SSH Tunnel Through Your Seedbox IP (Proxy for Your Home PC)
Anonymously / surfer anonymement. The 20 Coolest Jobs in Information Security. Project Meshnet. JStylo-Anonymouth - PSAL. Simple Online Privacy Guides and Tutorials. Tahoe-LAFS. Forums - Securibox Forums. The Cracking Bible - Team 3x. Opt out of global data surveillance programs like PRISM, XKeyscore, and Tempora - PRISM Break - PRISM Break.
Home. 2013/10/nsa-tor-stinks. Anonbib/cache/entropist.pdf. VENONA Cypherpunks Archives. Free Haven's Selected Papers in Anonymity. A Declaration of the Independence of Cyberspace. Start - netsec. INTO THE DEEP - totse's deepweb guide - freenet, i2p, and tor. The paranoid #! Security Guide (Page 1) / Tips, Tricks & Scripts. Part II: How to Be Anonymous Online (for Beginners) Comparison with Others - Whonix.