


The Tin Hat | Simple Online Privacy Guides and Tutorials TestGrid – tahoe-lafs This page is about the "Public Test Grid", which is also called the "pubgrid". The pubgrid has several purposes: to make it easier for people new to tahoe to begin to experiment to enable small-scale trial use of tahoe to help the tahoe community gain experience with grids of heterogenous servers without a pre-existing social organization The pubgrid also has two critical non-goals The pubgrid is not intended to provide large-scale storage, and it is not intended to be reliable. How To Connect To The Public Test Grid ¶ The test grid is subject to being updated at random times, so compatibility is likely to break without notice. The test grid is currently running an 1.0.0-compatible release (allmydata-tahoe: 1.9.2) (see "My versions" on the welcome page for the current version of the web gateway server). Set up the code according to docs/quickstart.rst and docs/running.rst. Then run bin/tahoe start. Publicly writable test directory ¶ Social Norms ¶ Suggested server setup: Status ¶ History ¶
MediaGoblin:: GNU MediaGoblin Seafile DLFP: MooseFS, système de fichier réparti à tolérance de panne MooseFS est un système de fichiers distribué méconnu regorgeant de qualités. En vrac : Le code est distribué sous GPLv3 ; Il utilise FUSE et fonctionne en espace utilisateur ; Il dispose d'une poubelle automatique à durée de rétention modifiable à souhait ; Il est très simple à déployer et administrer : comptez une heure, lecture de la documentation comprise pour avoir un serveur maître et quatre serveurs de données fonctionnels ; Compatible POSIX, il ne requiert aucune modification des programmes pour pouvoir y accéder ; L'ajout de machines pour agrandir l'espace disponible est d'une simplicité enfantine ; Vous choisissez le nombre de réplicas que vous désirez, par fichier ou par répertoire, pour la tolérance de panne, avec une seule commande, le tout à chaud… Le développement de MooseFS a débuté en 2005, et il a été libéré le 30 mai 2008. MooseFS est un système de fichiers méconnu regorgeant de qualités : Un peu d'histoire. C'est stable ! Bien sûr, tout n'est pas si parfait.
JStylo-Anonymouth - PSAL From PSAL The JStylo and Anonymouth integrated open-source project (JSAN) resides on GitHub. What is JSAN? JSAN is a writing style analysis and anonymization framework. It consists of two parts: JStylo - authorship attribution framework Anonymouth - authorship evasion (anonymization) framework JStylo is used as an underlying feature extraction and authorship attribution engine for Anonymouth, which uses the extracted stylometric features and classification results obtained through JStylo and suggests users changes to anonymize their writing style. Details about JSAN: Use Fewer Instances of the Letter "i": Toward Writing Style Anonymization. Tutorial JSAN tutorial: Presented at 28c3 video Download Downloads: If you use JStylo and/or Anonymouth in your research, please cite: Andrew McDonald, Sadia Afroz, Aylin Caliskan, Ariel Stolerman and Rachel Greenstadt. If you use the corpus in your research, please cite: Michael Brennan and Rachel Greenstadt. Developers
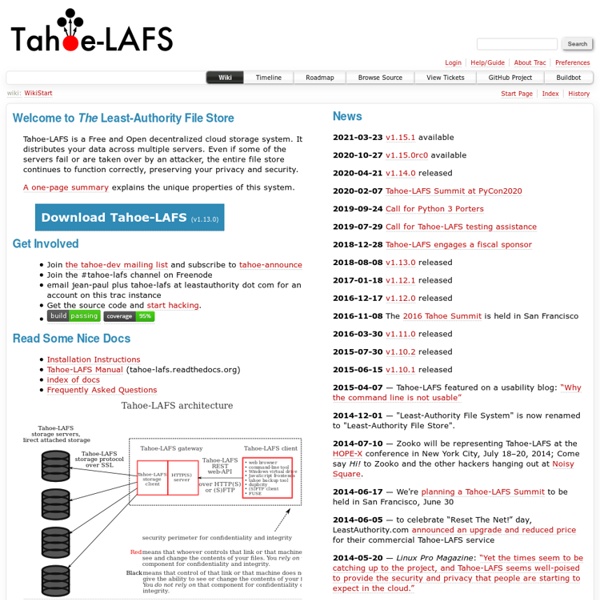
P2P-like Tahoe filesystem offers secure storage in the cloud Tahoe is a secure distributed filesystem that is designed to conform with the principle of least authority. The developers behind the project announced this month the release of version 1.5, which includes bugfixes and improvements to portability and performance, including a 10 percent boost to file upload speed over high-latency connections. Tahoe's underlying architecture is similar to that of a peer-to-peer network. Tahoe was originally developed with funding from Allmydata, a company that provides Web backup services. The idea was that every user would be able to get the benefits of distributed off-site backups by sharing a portion of their local drive space with the rest of the network. When a file is deployed to Tahoe, it is encrypted and split into pieces that are spread out across ten separate nodes. Although Tahoe is a distributed filesystem, it is not entirely decentralized. Tahoe is being used in a number of different ways. Listing image by Wikimedia Commons
Unhosted: separating web apps from data storage IPFS Features, Architecture and Requirements :: MooseFS network file system - Moose FS