

Password-less logins with OpenSSH. Posted by Steve on Fri 3 Jun 2005 at 09:45 Because OpenSSH allows you to run commands on remote systems, showing you the results directly, as well as just logging in to systems it's ideal for automating common tasks with shellscripts and cronjobs.
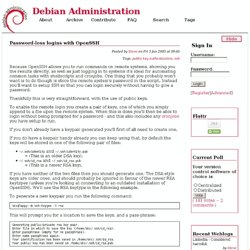
One thing that you probably won't want is to do though is store the remote system's password in the script. Pass on Passwords with scp. In this article, I show you how to use the scp (secure copy) command without needing to use passwords. I then show you how to use this command in two scripts. One script lets you copy a file to multiple Linux boxes on your network, and the other allows you to back up all of your Linux boxes easily. If you're a Linux sysadmin, you frequently need to copy files from one Linux box to another. Or, you may need to distribute a file to multiple boxes. You could use FTP, but using scp has many advantages. But what I like best about scp is it's easily scriptable. Here's an example demonstrating the most basic syntax for scp. Scp abc.tgz root@bozo:/tmp You now are asked for bozo's root password, so we're not quite there yet. Decide which user on the local machine will be using scp later on. Simple SSH Tutorial Outline. Passwordless SSH.
SSH concepts With remote access via ssh, there are 2 user accounts to consider : luser@local ---becomes---> ruser@remote Although both accounts can have the same account name (e.g. jdoe@local, jd@remote), and although ssh assumes that you will use the same username on both local and remote system, they are 2 distinctive user accounts, on separate machines. objective : while logged in at 'local' as 'luser', do one of the following : start a shell session on remote, as user ruser.
(This can be extended to running remote applications, including X applications or remote desktops ) copy files, owned by ruser (or at least readable by ruser), from remote to local (into a directory where luser has write access, eg [local:]/home/luser) copy files, owned by luser (or at least readable by luser), from local to remote (into a directory where ruser has write access, eg [remote:]/home/ruser) Those are the basic ssh operations. Key pairs and host-based authentication. Public Key authentication.
How to SSH into Your Palm Pre! The second day I got the Palm Pre, I was able to SSH into my own Palm Pre and also make it into a WiFi Router. Of course, this is usual business for me as I manage about 30+ web servers on a daily basis. Execute commands via ssh - Linux / UNIX Forum. SSH vs. VPN. VPN Definition An IP-based Virtual Private Network (VPN) provides a secure tunnel for transmitting data through an unsecured network such as the Internet. There are several protocols that can be used to achieve this such as PPTP, L2TP, L2F, IPSEC etc. IPSEC is the only protocol that is an IETF standard. A VPN is “virtual” because it does not require dedicated lines.
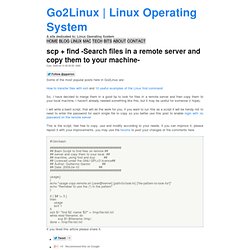
It is “private” because encryption is used to achieve security. Setting up a reverse SSH tunnel. Scp + find -Search files in a remote server and copy them to your machine- 1. Some of the most popular posts here in Go2Linux are:
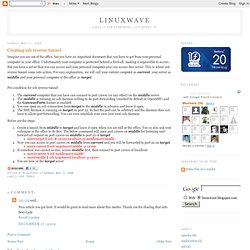
Creating ssh reverse tunnel. Imagine you are out of the office, but you have an important document that you have to get from your personal computer in your office.
Unfortunately your computer is protected behind a firewall, making it impossible to access. But you have a server that you can access and your personal computer also can access this server. How to alter system-wide $PATH for non-interactive, non-login bash shells invoked via sshd? Transferring files with OpenSSH. Posted by Anonymous on Mon 11 Oct 2004 at 12:49 OpenSSH is a well known program which allows you to login to a host remotely, and run commands etc.
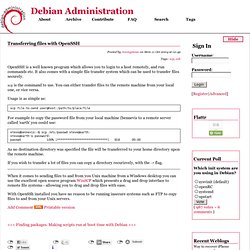
CUED ssh - how to use it. How should I authenticate myself The simplest use of slogin and friends will seem identical in terms of perceived behaviour to rlogin and equivalents, in that you will either be prompted for your normal password, or the server will honour an entry in your .rhosts file on the server machine.
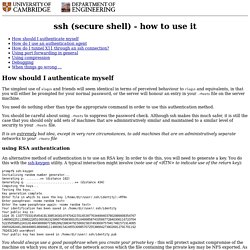
You need do nothing other than type the appropriate command in order to use this authentication method. You should be careful about using .rhosts to suppress the password check. Although ssh makes this much safer, it is still the case that you should only add sets of machines that are administratively similar and maintained to a similar level of security to your .rhosts file. Getting started with SSH - Kimmo Suominen. The following sections hope to provide enough information to setup a user new to ssh with the appropriate files necessary for accessing remote hosts in a secure manner.

Improvements to and comments about this document are welcome. Updated: The examples now show ssh version 2 commands, using OpenSSH. There are several security vulnerabilities in protocol version 1. Everyone should have already migrated to version 2 by now, so it was about time for me to also reflect best practises in this document. I also updated the link section at the end of the document to better reflect today’s software selection. Contents About public key cryptography.